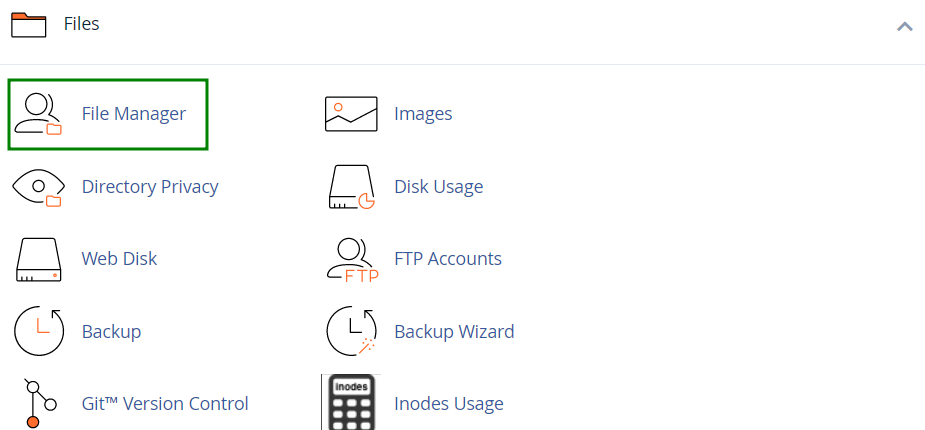
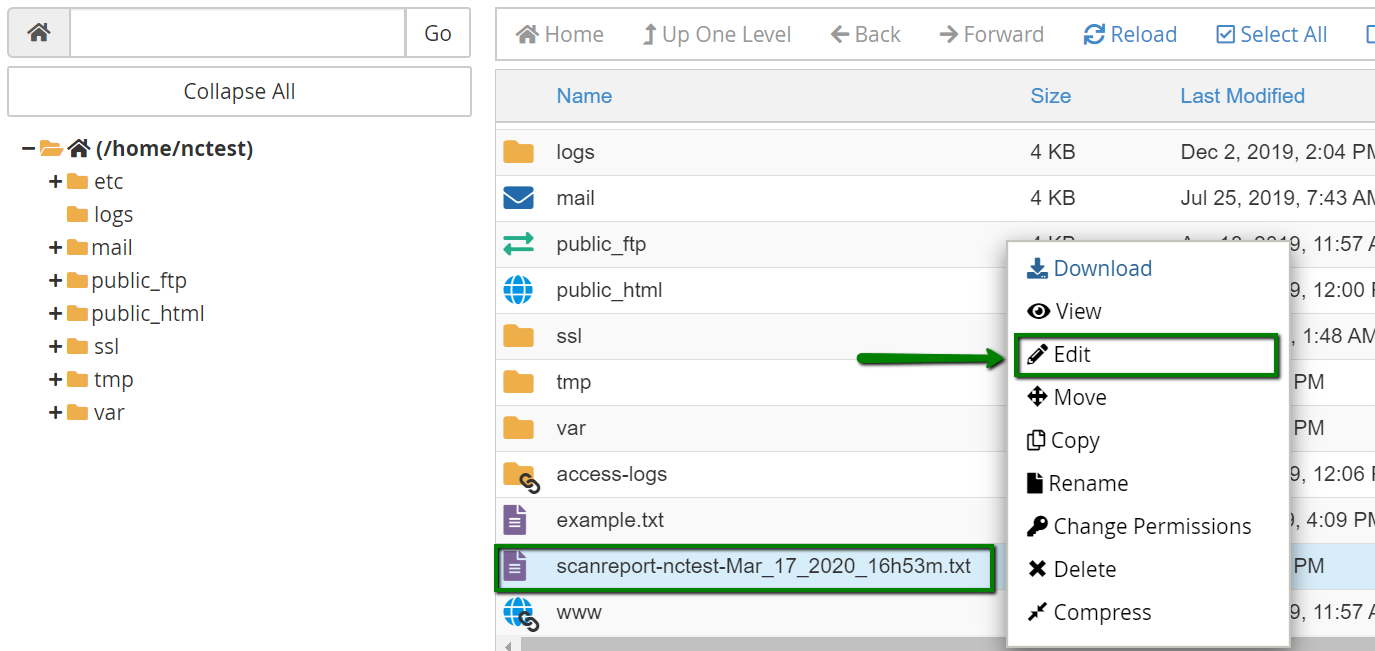
{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":10227,\\\"categoryId\\\":2194}\"":{"body":{"Id":10227,"FriendlyId":"","ArticleTypeId":0,"Title":"How to work with a scan report","ArticleName":"How to work with a scan report","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"VGhlIHRocmVhdCBvZiBoYWNraW5nIGlzIGEgdmVyeSBzZXJpb3VzIGlzc3VlLiBUaGF04oCZcyB3aHkgaXTigJlzIGltcG9ydGFudA0KIHRvIHBheSBhdHRlbnRpb24gdG8gdGhlIHNlY3VyaXR5IG9mIHlvdXIgY1BhbmVsIGFjY291bnQuPGJyIC8+PGJyIC8+T3VyIA0KU2hhcmVkIEhvc3Rpbmcgc2VydmVycyBoYXZlIGFuIGVmZmVjdGl2ZSBmaXJld2FsbCBzeXN0ZW0gYWxvbmcgd2l0aCBhIA0Kc2V0IG9mIG90aGVyIHNlY3VyaXR5IG1lYXN1cmVzLiBIb3dldmVyLCBjUGFuZWwgYWNjb3VudCBwcm90ZWN0aW9uIGFsc28gDQpkZXBlbmRzIG9uIHlvdS4gQnkgc2Nhbm5pbmcgeW91ciBob3N0aW5nIHNwYWNlIGZvciB2aXJ1c2VzLCB0cm9qYW5zLCANCm1hbHdhcmUsIGFuZCBvdGhlciB0aHJlYXRzLCB5b3UgZW5zdXJlIGl0cyBzYWZldHkuPGJyIC8+PGJyIC8+VG8gbG9jYXRlIGFueSBtYWxpY2lvdXMgc29mdHdhcmUgaW4geW91ciBjUGFuZWwsIHlvdSBjYW4gZWl0aGVyIHVzZSA8Yj5WaXJ1cyBTY2FubmVyPC9iPiBpbiB5b3VyIGNQYW5lbCwgb3IgY29udGFjdCBvdXIgPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0LyIgdGFyZ2V0PSJfcGFyZW50Ij5TdXBwb3J0IFRlYW08L2E+Lg0KIFdlIHdpbGwgcGVyZm9ybSBvbi1kZW1hbmQgc2Nhbm5pbmcgb2YgeW91ciBob3N0aW5nIGFjY291bnQgdG8gZW5zdXJlIGl0DQogaXMgY2xlYW4gYW5kIHNlY3VyZS4gQSBkZXRhaWxlZCByZXBvcnQgd2lsbCBiZSBwcm92aWRlZCBzbyB5b3UgY2FuIA0KZXhhbWluZSBpdC48YnIgLz48YnIgLz48cD48YSBocmVmPSIjbG9jYXRlX3NwYW0iPkhvdyB0byBsb2NhdGUgeW91ciBzY2FuIHJlcG9ydDwvYT48L3A+PHA+PGEgaHJlZj0iI3JlYWRfc3BhbSI+SG93IHRvIHJlYWQgeW91ciBzY2FuIHJlcG9ydDwvYT48L3A+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxwPjxhIG5hbWU9ImxvY2F0ZV9zcGFtIj48Yj5Ib3cgdG8gbG9jYXRlIHlvdXIgc2NhbiByZXBvcnQ8L2I+PC9hPjwvcD48L2Rpdj48ZGl2PjxiciAvPjwvZGl2Pk9uY2UNCiB0aGUgc2Nhbm5pbmcgcHJvY2VzcyBpcyBjb21wbGV0ZSwgYSByZXBvcnQgaXMgdXBsb2FkZWQgYXV0b21hdGljYWxseSB0bw0KIHlvdXIgY1BhbmVsIGFjY291bnQuIFRvIGxvY2F0ZSBpdCwgZm9sbG93IHRoZSBzdGVwcyBiZWxvdzo8YnIgLz48YnIgLz4xLiA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvMTAxMzIvMjcvd2hlcmUtY2FuLWktbG9nLWludG8tbXktY3BhbmVsLWhvc3RpbmctYWNjb3VudCIgdGFyZ2V0PSJfcGFyZW50Ij5Mb2cgaW48L2E+IHRvIHlvdXIgY1BhbmVsLjxiciAvPjIuIE5hdmlnYXRlIHRvIHRoZSA8Yj5GaWxlczwvYj4gc2VjdGlvbiAmZ3Q7Jmd0OyA8Yj5GaWxlIE1hbmFnZXI8L2I+OjxiciAvPjxiciAvPjxkaXY+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2ZpbGUxLjEucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj4zLiBHbyB0byB0aGUgPGI+L2hvbWUvY1BhbmVsX3VzZXJuYW1lPC9iPiBkaXJlY3RvcnkuIFRoZSBzY2FuIHJlcG9ydCBpcyB1cGxvYWRlZCB0byBpdC48L2Rpdj5Vc3VhbGx5LCBpdHMgbmFtZSBjb250YWlucyB5b3VyIGNQYW5lbCB1c2VybmFtZSBhbmQgdGhlIGRhdGUgd2hlbiB0aGUgZmlsZSB3YXMgZ2VuZXJhdGVkLCBlLmcuLCA8aT5zY2FucmVwb3J0LW5jdGVzdC1NYXJfMTdfMjAyMF8xNmhfNTNtLnR4dC48L2k+PGJyIC8+PGJyIC8+NC4gTG9jYXRlIHRoZSBmaWxlLCByaWdodC1jbGlja8KgICZndDsmZ3Q7IGNob29zZSB0aGUgPGI+RWRpdDwvYj4gb3B0aW9uLjxiciAvPjxkaXY+PGJyIC8+PC9kaXY+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvc2Nhbl9yZXBvcnQyLnBuZyIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+VGhlIHNjYW4gcmVwb3J0IHdpbGwgYmUgb3BlbmVkIGluIGEgbmV3IGJyb3dzZXIgd2luZG93LiANCg0KTm93IHlvdSBhcmUgcmVhZHkgdG8gZXhhbWluZSBpdC4gPGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+PHA+PGEgbmFtZT0icmVhZF9zcGFtIj48Yj5Ib3cgdG8gcmVhZCB5b3VyIHNjYW4gcmVwb3J0PC9iPjwvYT48L3A+PGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PkJlbG93IHlvdSBjYW4gZmluZCBhIHNob3J0ZW5lZCBleGFtcGxlIG9mIGEgc2NhbiByZXBvcnQgcHJvdmlkZWQgYnkgb3VyIFN1cHBvcnQgVGVhbTogPGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48cHJlIGNsYXNzPSJwcmV0dHlwcmludCI+LS0tLS0tLS0tLS0gU0NBTiBSRVBPUlQgLS0tLS0tLS0tLS0NClRpbWVTdGFtcDogV2VkLCAyNiBGZWIgMjAyMCAwMTozMTozOSAtMDUwMA0KDQoNClNjYW5uaW5nIC9ob21lL2NQYW5lbF91c2VybmFtZToNCg0KJy9ob21lL2NQYW5lbF91c2VybmFtZS8uYmN3ZmdpLnBocCcNCiMgQ2xhbUFWIGRldGVjdGVkIHZpcnVzID0gW1lBUkEucGhwX21hbHdhcmVfaGV4aW5qZWN0LlVOT0ZGSUNJQUxdDQoNCicvaG9tZS9jUGFuZWxfdXNlcm5hbWUvb2xkL3dwLWFkbWluL2NmZ3MucGhwJw0KIyBLbm93biBleHBsb2l0ID0gW0ZpbmdlcnByaW50IE1hdGNoXSBbUEhQIEV4cGxvaXRdDQoNCicvaG9tZS9jUGFuZWxfdXNlcm5hbWUvb2xkL3dwLWFkbWluL2ltYWdlcy9hbGlnbi1sZWZ0cy5wbmcnDQojIFN1c3BpY2lvdXMgaW1hZ2UgZmlsZSAoaGlkZGVuIHNjcmlwdCBmaWxlKQ0KDQonL2hvbWUvY1BhbmVsX3VzZXJuYW1lL3B1YmxpY19odG1sL2Fzc2V0cy9hc3NldC9qcy9wbHVnaW5zL2VkaXRvcnMvY29kZW1pcnJvci9tb2RlL2NsaWtlL2luZGV4Lmh0bWwnDQojIFN1c3BpY2lvdXMgZmlsZSB0eXBlIFthcHBsaWNhdGlvbi94LWNdDQoNCicvaG9tZS9jUGFuZWxfdXNlcm5hbWUvcHVibGljX2h0bWwvYXNzZXRzL2Fzc2V0L2pzL3BsdWdpbnMvdXBsb2FkZXJzL3BsdXBsb2FkL2ZpbGVzL01veGllLnhhcCcNCiMgKGNvbXByZXNzZWQgZmlsZTogTW94aWUuZGxsIFtkZXB0aDogMV0pIE1TIFdpbmRvd3MgQmluYXJ5L0V4ZWN1dGFibGUgW2FwcGxpY2F0aW9uL3gtd2luZXhlY10NCg0KJy9ob21lL2NQYW5lbF91c2VybmFtZS9wdWJsaWNfaHRtbC92ZW5kb3IvbGFyYXZlbC9mcmFtZXdvcmsvc3JjL0lsbHVtaW5hdGUvRmlsZXN5c3RlbS9GaWxlc3lzdGVtLnBocCcNCiMgUmVndWxhciBleHByZXNzaW9uIG1hdGNoID0gW3N5bWxpbmtccypcKF0NCg0KJy9ob21lL2NQYW5lbF91c2VybmFtZS9leGFtcGxlLmNvbS93cC1jb250ZW50L3BsdWdpbnMvY29udGFjdC1mb3JtLTcvd3AtY29udGFjdC1mb3JtLTcucGhwJw0KIyBTY3JpcHQgdmVyc2lvbiBjaGVjayBbT0xEXSBbQ29udGFjdCBGb3JtIDcgdjUuMC41ICZsdDsgdjUuMS4zXQ0KDQonL2hvbWUvY1BhbmVsX3VzZXJuYW1lL2V4YW1wbGUuY29tL3dwLWNvbnRlbnQvdGhlbWVzL3dlZGRpbmd2ZXJvL2F1dG8taW5zdGFsbC91cGxvYWRzL2VzcHJlc3NvL3RpY2tldHMnDQojIFdvcmxkIHdyaXRlYWJsZSBkaXJlY3RvcnkNCg0KDQotLS0tLS0tLS0tLSBTQ0FOIFNVTU1BUlkgLS0tLS0tLS0tLS0NClNjYW5uZWQgZGlyZWN0b3JpZXM6IDgyMjENClNjYW5uZWQgZmlsZXM6IDc3ODE4DQpJZ25vcmVkIGl0ZW1zOiAyMTcNClN1c3BpY2lvdXMgbWF0Y2hlczogODkzDQpWaXJ1c2VzIGZvdW5kOiA3NDMNCkZpbmdlcnByaW50IG1hdGNoZXM6IDg1DQpEYXRhIHNjYW5uZWQ6IDUyNDUuNzYgTUINClNjYW4gdGltZS9pdGVtOiAwLjAxMyBzZWMNClNjYW4gdGltZTogMTE0OS41ODAgc2VjDQo8L3ByZT48ZGl2Pg0KUGF5IGF0dGVudGlvbiB0byB0aGUgbWFpbiBib2R5IG9mIHRoZSByZXBvcnQuIEl0IGNvbnRhaW5zIHRoZSBmb2xsb3dpbmcgaW5mb3JtYXRpb246IDxiciAvPjwvZGl2Pjx1bD48bGk+cGF0aA0KIHRvIHRoZSBkaXJlY3Rvcnkgb3IgZmlsZSAoZS5nLiANCicvaG9tZS9jUGFuZWxfdXNlcm5hbWUvcHVibGljX2h0bWwvdmVuZG9yL2xhcmF2ZWwvZnJhbWV3b3JrL3NyYy9JbGx1bWluYXRlL0ZpbGVzeXN0ZW0vRmlsZXN5c3RlbS5waHAnKQ0KIDs8L2xpPjxsaT5zY2FuIHJlc3VsdCAoZS5nLiAjIFJlZ3VsYXIgZXhwcmVzc2lvbiBtYXRjaCA9IFtzeW1saW5rXHMqXChdKS48L2xpPjwvdWw+PGJyIC8+VGFraW5nDQogaW50byBhY2NvdW50IHRoZSBzY2FuIHJlc3VsdCwgeW91IHdpbGwgbmVlZCB0byBwZXJmb3JtIGNlcnRhaW4gYWN0aW9ucyANCnRvIGtlZXAgeW91ciBhY2NvdW50IHNlY3VyZS4gTW9zdCBjYXNlcyBhcmUgZGVzY3JpYmVkIGluIHRoZSB0YWJsZSANCmJlbG93OjxiciAvPjxiciAvPjxiPk5PVEUgMTwvYj46IE1ha2Ugc3VyZSB0byA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTM2NS8yMTk5L2hvdy10by1jcmVhdGUtYW5kLXJlc3RvcmUtYmFja3Vwcy1pbi1jcGFuZWwiIHRhcmdldD0iX3BhcmVudCI+Y3JlYXRlIGEgYmFja3VwPC9hPiBvZiB5b3VyIGNQYW5lbCBiZWZvcmUgbWFraW5nIGFueSBjaGFuZ2VzLjxiciAvPjxiciAvPjxkaXY+PGI+Tk9URSAyPC9iPjoNCiBGaWxlcyB3aXRoIHJhbmRvbWx5LWdlbmVyYXRlZCBuYW1lcyAoZS5nLiBiY3dmZ2kucGhwKSBhbG1vc3QgYWx3YXlzIA0KY29udGFpbiBtYWxpY2lvdXMgY29kZS4gVGhlc2UgZmlsZXMgZG8gbm90IGJlbG9uZyB0byBhbnkgQ01TIGFuZCBtdXN0IGJlDQogZGVsZXRlZC4gPGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PHN0eWxlIHR5cGU9InRleHQvY3NzIj48IVtDREFUQVsNCnRhYmxlLCB0ciwgdGQgew0KYm9yZGVyOiAxcHggc29saWQgYmxhY2s7DQoNCmZvbnQtc2l6ZToxNHB4Ow0KfQ0KdGQgew0KdGV4dC1hbGlnbjpjZW50ZXI7DQpvdmVyZmxvdzpoaWRkZW47DQp3b3JkLWJyZWFrOm5vcm1hbDsNCn0NCl1dPjwvc3R5bGU+PHRhYmxlIHN0eWxlPSJ3aWR0aDEwMCUiPjx0Ym9keT48dHI+PHRoPlJlc3VsdA0KCQkJCQkJCQk8L3RoPjx0aD5EZXNjcmlwdGlvbg0KCQkJCQkJCQk8L3RoPjx0aD5BY3Rpb24gdG8gdGFrZQ0KCQkJCQkJCQk8L3RoPjwvdHI+PHRyPjx0ZD4jIENsYW1BViBkZXRlY3RlZCB2aXJ1czwvdGQ+PHRkPkFudGl2aXJ1cyBzb2Z0d2FyZSBoYXMgZm91bmQgYSBwb3RlbnRpYWxseSBkYW5nZXJvdXMgZmlsZSB3aXRoIG1hbHdhcmUuPC90ZD48dGQ+UmVtb3ZlIHRoZSBmaWxlLjwvdGQ+PC90cj48dHI+PHRkPiMgU3VzcGljaW91cyBmaWxlIHR5cGUgW2FwcGxpY2F0aW9uL3gtY108YnIgLz48YnIgLz4jIE1TIFdpbmRvd3MgQmluYXJ5L0V4ZWN1dGFibGUgW2FwcGxpY2F0aW9uL3gtd2luZXhlY108YnIgLz48YnIgLz4jIChjb21wcmVzc2VkIGZpbGU6IE1veGllLmRsbCBbZGVwdGg6IDFdKSBNUyBXaW5kb3dzPGJyIC8+PGJyIC8+IyBCaW5hcnkvRXhlY3V0YWJsZSBbYXBwbGljYXRpb24veC13aW5leGVjXTxiciAvPjxiciAvPiMgTVMtRE9TIEJpbmFyeS9FeGVjdXRhYmxlIFthcHBsaWNhdGlvbi94LWRvc2V4ZWNdPC90ZD48dGQ+QW50aXZpcnVzIHNvZnR3YXJlIGhhcyBmb3VuZCBXaW5kb3dzIGJpbmFyeSBvciBleGVjdXRhYmxlIGZpbGVzLiA8YnIgLz48YnIgLz5TdWNoIGZpbGVzIGNhbm5vdCBiZSBleGVjdXRlZCBvbiBhIExpbnV4LWJhc2VkIE9TLiBZb3Ugd291bGQgbm90PGJyIC8+bm9ybWFsbHkgZXhwZWN0IHRvIGZpbmQgb25lIHdpdGhpbiBhIGNQYW5lbCBhY2NvdW50IC48YnIgLz48YnIgLz5Zb3UgY2FuIGRpc2NvdmVyIGEgVHJvamFuIGZpbGUgYW1vbmcgdGhlbS48L3RkPjx0ZD5SZW1vdmUgdGhlIGZpbGUuPC90ZD48L3RyPjx0cj48dGQ+IyBMaW51eCBCaW5hcnkvRXhlY3V0YWJsZSBbYXBwbGljYXRpb24veC1zaGFyZWRsaWJdPC90ZD48dGQ+QW50aXZpcnVzIHNvZnR3YXJlIGhhcyBmb3VuZCBMaW51eCBiaW5hcnkgb3IgZXhlY3V0YWJsZSBmaWxlcy48YnIgLz5TdWNoIGZpbGVzIGNhbiBiZSBleGVjdXRlZCBvbiBhIExpbnV4LWJhc2VkIE9TLiBTdGlsbCwgeW91IHdvdWxkIG5vdCBub3JtYWxseSBleHBlY3QgdG8gZmluZCBvbmUgd2l0aGluIGEgY1BhbmVsIGFjY291bnQuIDxiciAvPklmIGEgTGludXggYmluYXJ5IG9yIGV4ZWN1dGFibGUgZmlsZSBpcyBsb2NhdGVkIGluIGEgY1BhbmVsIGFjY291bnQsIGl0IGlzIG1vc3QgbGlrZWx5IGFuIGV4cGxvaXQgdGhhdCByZW1haW5zIGhpZGRlbi48YnIgLz48L3RkPjx0ZD5SZW1vdmUgdGhlIGZpbGUuPC90ZD48L3RyPjx0cj48dGQ+IyBLbm93biBleHBsb2l0ID0gW0ZpbmdlcnByaW50IE1hdGNoXTwvdGQ+PHRkPkFudGl2aXJ1cyBzb2Z0d2FyZSBjb25zaWRlcnMgYSBmaWxlIGFzIGFuIGV4cGxvaXQuIDxiciAvPkFuIGV4cGxvaXQgY2FuIGJlDQogYSBwcm9ncmFtLCBhIHBpZWNlIG9mIGNvZGUsIG9yIGV2ZW4ganVzdCBhIHN0cmluZyBvZiBjaGFyYWN0ZXJzLiBJdCANCnRha2VzIGFkdmFudGFnZSBvZiBhIHByb2dyYW0uIFRoZW4sIHRoaXMgcHJvZ3JhbSBhY3RzIGluIGFuIHVuZXhwZWN0ZWQgDQp3YXksIHdoaWNoIHJlc3VsdHMgaW4gdW5kZXNpcmFibGUgYmVoYXZpb3IuIEFsc28sIGV4cGxvaXRzIGFyZSANCm1hbGljaW91c2x5IHVzZWQgdG8gZ2FpbiB1bmF1dGhvcml6ZWQgYWNjZXNzLjwvdGQ+PHRkPlVubGVzcyB5b3Uga25vdyB0aGUgcHVycG9zZSBvZiB0aGlzIGZpbGUsIHJlbW92ZSBpdCBmcm9tIHlvdXIgY1BhbmVsLiBJZg0KIGl0IGlzIHJlbGF0ZWQgdG8gaW5zdGFsbGVkIHNvZnR3YXJlIGFuZCB5b3UgbmVlZCBpdCwgZWl0aGVyIGNsZWFuIGl0IG9yDQogdXBsb2FkIGFnYWluIGZyb20gYSB0cnVzdGVkIHNvdXJjZS4gPGJyIC8+PGI+UExFQVNFIE5PVEU8L2I+OiBJdCBpcyBzdHJvbmdseSByZWNvbW1lbmRlZCB0aGF0IHlvdSB1c2UgY29udGVudCBvbmx5IGZyb20gdGhlIG9mZmljaWFsIHNvdXJjZS48L3RkPjwvdHI+PHRyPjx0ZD4jIFN5bWxpbmsgdG88L3RkPjx0ZD5UaGUgZmlsZSBpcyBhIHN5bWJvbGljIGxpbmsuPGJyIC8+PGJyIC8+SXQgY29uc2lzdHMgb2YgYSBzcGVjaWFsIHR5cGUgb2YgZmlsZSB0aGF0IHNlcnZlcyBhcyBhIHJlZmVyZW5jZSB0byBhbm90aGVyIGZpbGUgb3IgZGlyZWN0b3J5LiA8YnIgLz48YnIgLz5Tb21lIGRlZmF1bHQgZmlsZXMgcmVxdWlyZSBzeW1saW5rcyBmb3IgdGhlIHByb3BlciB3b3JrIG9mIGNQYW5lbCBzZXJ2aWNlczo8YnIgLz48YnIgLz48aT4nL2hvbWUvY1BhbmVsX3VzZXJuYW1lLy5jYWdlZnMvb3B0L2FsdC9waHBYWC9saW5rL2NvbmYnPGJyIC8+Jy9ob21lL2NQYW5lbF91c2VybmFtZS9hY2Nlc3MtbG9ncyc8YnIgLz4nL2hvbWUvY1BhbmVsX3VzZXJuYW1lLy5jYWdlZnMvdG1wL215c3FsLnNvY2snPC9pPjxiciAvPsKgPGJyIC8+QnV0IHRoZSBjdXN0b20gc3ltbGlua3MgKGUuZy4gYSBzeW1saW5rIHRvIGZpbGVzIG91dHNpZGUgb2YgeW91ciBjUGFuZWwgYWNjb3VudCkgbWF5IGNhdXNlIHNlcmlvdXMgc2VjdXJpdHkgYnJlYWNoZXMuPC90ZD48dGQ+UGF5IGF0dGVudGlvbiB0byB0aGUgY3VzdG9tIHN5bWxpbmtzLiBTdWNoIGZpbGVzIHNob3VsZCBiZSByZW1vdmVkIGZyb20geW91ciBhY2NvdW50LjxiciAvPjxiciAvPlN5bWxpbmtzIHRvIGRlZmF1bHQgY1BhbmVsIGZpbGVzIGNhbiBiZSBpZ25vcmVkLjxiciAvPjwvdGQ+PC90cj48dHI+PHRkPiMgU29ja2V0PC90ZD48dGQ+QSBzb2NrZXQgaXMgdHlwaWNhbGx5IHVzZWQgdG8gdHJhbnNmZXIgZGF0YSBiZXR3ZWVuIHR3byBzZXBhcmF0ZSANCnByb2Nlc3Nlcy4gWW91IHdvdWxkIG5vdCBleHBlY3QgdG8gbm9ybWFsbHkgZmluZCBvbmUgd2l0aGluIGEgY1BhbmVsIA0KYWNjb3VudC48L3RkPjx0ZD5Vbmxlc3MgeW91IGtub3cgdGhlIHB1cnBvc2Ugb2YgdGhpcyBmaWxlIG9yIGl0IGlzIHJlbGF0ZWQgdG8gdGhlIA0Kc29mdHdhcmUgaW5zdGFsbGVkIGZyb20gdGhlIHRydXN0ZWQgc291cmNlLCByZW1vdmUgaXQgZnJvbSB5b3VyIGNQYW5lbC48YnIgLz48L3RkPjwvdHI+PHRyPjx0ZD4jIFJlZ3VsYXIgZXhwcmVzc2lvbiBtYXRjaCA9IFtzeW1saW5rXHMqXChdPC90ZD48dGQ+QSBmaWxlIGNvbnRhaW5zICdzeW1saW5rKHMpJyBleHByZXNzaW9uIGFzIGEgY29tbWVudCBvciB2YXJpYWJsZS48L3RkPjx0ZD5JdCBpcyBhIGZhbHNlLXBvc2l0aXZlLiBUaGUgZmlsZSBjYW4gYmUgaWdub3JlZC48L3RkPjwvdHI+PHRyPjx0ZD4jIFJlZ3VsYXIgZXhwcmVzc2lvbiBtYXRjaCA9IFtcbig/IVxzKigvL3xcI3xcKikpLiovZXRjL3Bhc3N3ZF08L3RkPjx0ZD5BIGZpbGUgY29udGFpbnMgJy9ldGMvcGFzc3dkJyBleHByZXNzaW9uIGFzIGEgY29tbWVudCBvciB2YXJpYWJsZS48L3RkPjx0ZD5JdCBpcyBhIGZhbHNlLXBvc2l0aXZlLiBUaGUgZmlsZSBjYW4gYmUgaWdub3JlZC48L3RkPjwvdHI+PHRyPjx0ZD4jIFJlZ3VsYXIgZXhwcmVzc2lvbiBtYXRjaCA9IFtcbig/IVxzKigvL3xcI3xcKikpLipcLnNzaC9dPC90ZD48dGQ+QSBmaWxlIGNvbnRhaW5zICcvLnNzaCcgZXhwcmVzc2lvbiBhcyBhIGNvbW1lbnQgb3IgdmFyaWFibGUuIFN1Y2ggZmlsZXMgDQphcmUgcG90ZW50aWFsbHkgaGFybWZ1bCB0byB5b3VyIGFjY291bnQgYXMgdGhleSBhbGxvdyByZW1vdGUgYWNjZXNzIA0KdXNpbmcgU1NIIGtleXMuPGJyIC8+PC90ZD48dGQ+VW5sZXNzIHlvdSBrbm93IHRoZSBwdXJwb3NlIG9mIHRoaXMgZmlsZSBvciBpdCBpcyByZWxhdGVkIHRvIHRoZSANCnNvZnR3YXJlIGluc3RhbGxlZCBmcm9tIHRoZSB0cnVzdGVkIHNvdXJjZSwgcmVtb3ZlIGl0IGZyb20geW91ciBjUGFuZWwuPC90ZD48L3RyPjx0cj48dGQ+IyBVbml2ZXJzYWwgZGVjb2RlIHJlZ2V4IG1hdGNoPC90ZD48dGQ+QSBmaWxlIGNvbnRhaW5zIHNvbWUgc3RyaW5nIGVuY29kZWQgd2l0aCBhIGNvbW1vbiBlbmNvZGVyLCBlLmcuIGJhc2U2NC4gVGhleSBhcmUgb2Z0ZW4gdXNlZCB0byBoaWRlIG1hbGljaW91cyBjb2RlLjwvdGQ+PHRkPlVubGVzcyB5b3Uga25vdyB0aGUgcHVycG9zZSBvZiB0aGlzIGZpbGUgb3IgaXQgaXMgcmVsYXRlZCB0byB0aGUgDQpzb2Z0d2FyZSBpbnN0YWxsZWQgZnJvbSB0aGUgdHJ1c3RlZCBzb3VyY2UsIHJlbW92ZSBpdCBmcm9tIHlvdXIgY1BhbmVsLjwvdGQ+PC90cj48dHI+PHRkPiMgU2NyaXB0IHZlcnNpb24gY2hlY2sgW09MRF08L3RkPjx0ZD5UaGUgaW5zdGFsbGF0aW9uLCBwbHVnaW4gb3IgdGhlbWUgdmVyc2lvbiBpcyBvdXRkYXRlZC4gU29mdHdhcmUgdXBkYXRlcyANCmFyZSBpbXBvcnRhbnQgYmVjYXVzZSB0aGV5IGNoZWNrIGZvciB0aGUgYnVncyBhbmQgdnVsbmVyYWJpbGl0aWVzIGZvdW5kIA0KaW4gdGhlIHByZXZpb3VzIHZlcnNpb25zLiBBIOKAmGhvbGXigJkgaW4gb25lIGNhbiBhZmZlY3QgeW91ciBlbnRpcmUgDQppbnN0YWxsYXRpb24gYXMgd2VsbCBhcyB5b3VyIGNQYW5lbCBhY2NvdW50LjwvdGQ+PHRkPkVuc3VyZSB0aGF0IHlvdXIgaW5zdGFsbGF0aW9ucyBhcmUgdXAgdG8gZGF0ZS48L3RkPjwvdHI+PHRyPjx0ZD4jIFdvcmxkIHdyaXRlYWJsZSBkaXJlY3Rvcnk8L3RkPjx0ZD5QZXJtaXNzaW9ucyBmb3IgYSBkaXJlY3RvcnkgYXJlIHNldCB0byA3NzcuPGJyIC8+PGJyIC8+SXQgaXMgcmVjb21tZW5kZWQgdG8gaGF2ZSBkZWZhdWx0IHBlcm1pc3Npb25zIGFzc2lnbmVkIHRvIHdlYnNpdGUgZmlsZXMgYW5kIGZvbGRlcnMuPGJyIC8+VGhleSBhcmUgNjQ0IGZvciBmaWxlcyBhbmQgNzU1IGZvciBmb2xkZXJzLiA8YnIgLz48YnIgLz5Ib3dldmVyLCBpdCBpcyBzYWZlIHRvIGhhdmUgcGVybWlzc2lvbnMgc2V0IHRvIDc3NyBmb3IgZGVmYXVsdCBjUGFuZWwgZm9sZGVyczo8YnIgLz48YnIgLz48aT4vaG9tZS9jUGFuZWxfdXNlci8uY2FnZWZzL3Zhci9jYWNoZTxiciAvPi9ob21lL2NQYW5lbF91c2VyLy5jYWdlZnMvdmFyL3BocDxiciAvPi9ob21lL2NQYW5lbF91c2VyLy5jYWdlZnMvdmFyL3J1bjwvaT48L3RkPjx0ZD5VcGRhdGUgcGVybWlzc2lvbnMgZm9yIHRoZSBpbmRpY2F0ZWQgZGlyZWN0b3J5LjwvdGQ+PC90cj48dHI+PHRkPiMgU2NhbiBUaW1lb3V0ICgzMCBzZWNvbmRzKSB3aGlsZSBwcm9jZXNzaW5nPC90ZD48dGQ+VGhlIHNjYW4gcHJvY2VzcyBoYXMgYmVlbiBpbnRlcnJ1cHRlZC48L3RkPjx0ZD5Zb3UgY2FuIHB1dCBpbiBhIHJlcXVlc3QgdG8gb3VyIFN1cHBvcnQgVGVhbSB0byBzY2FuIGl0IGFkZGl0aW9uYWxseS48L3RkPjwvdHI+PHRyPjx0ZD4jIENsYW1kIEVycm9yIGZvcjwvdGQ+PHRkPkFudGl2aXJ1cyBzb2Z0d2FyZSBjb25zaWRlcnMgdGhhdCB0aGUgZmlsZSBpcyBsb2NhdGVkIGluc2lkZSB0aGUgc2VydmljZSBkaXJlY3RvcnksIHRoZXJlZm9yZSwgaXQgc2hvdWxkIG5vdCBiZSBzY2FubmVkLjwvdGQ+PHRkPlRoZSBmaWxlIGNhbiBiZSBpZ25vcmVkLjwvdGQ+PC90cj48L3Rib2R5PjwvdGFibGU+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+T25jZSBhbGwgbWVhc3VyZXMgYXJlIHRha2VuLCBpdOKAmXMgdGltZSB0byBjcmVhdGUgYW4gdXAtdG8tZGF0ZSBiYWNrdXAgb2YgeW91ciBhY2NvdW50LiBUaGlzIGNhbiBlYXNpbHkgYmUgZG9uZSB3aXRoIHRoZSBidWlsdC1pbiBiYWNrdXAgdG9vbCBsb2NhdGVkIGluIHlvdXIgY1BhbmVsLiBGb3IgbW9yZSBkZXRhaWxzLCBjaGVjayBvdXQgdGhlIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85MzY1LzIxOTkvaG93LXRvLWNyZWF0ZS1hbmQtcmVzdG9yZS1iYWNrdXBzLWluLWNwYW5lbCIgdGFyZ2V0PSJfcGFyZW50Ij5mb2xsb3dpbmcgYXJ0aWNsZTwvYT4uIDwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PlRoYXTigJlzIGl0ISA8L2Rpdj4=","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2024-03-11T14:41:29.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2020-05-29T14:51:17.0000000","ApprovalDatetime":"2020-06-12T14:08:33.0000000","RequestCount":36802,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":0,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2194,"CategoryName":"Tips & Tricks"}],"AssociatedCategories":[{"CategoryId":2194,"CategoryName":"Tips & Tricks","CategoryDisplayName":"HostingTips & Tricks"}],"AssociatedTags":[{"TagId":26572,"Tag":" file manager"},{"TagId":67199,"Tag":" hacked"},{"TagId":81789,"Tag":"scan"},{"TagId":81790,"Tag":" virus"}],"RelatedArticles":[{"ArticleId":10123,"PreferedCategoryId":89,"ArticleTypeId":0,"ArticleName":"Using CXS scan via SSH","ArticleTypeName":null,"Title":"Using CXS scan via SSH","LiveDateTime":null,"ModifiedDateTime":"05/13/2026","MarkedAsNew":false,"MarkedAsFeatured":false},{"ArticleId":9242,"PreferedCategoryId":2194,"ArticleTypeId":3,"ArticleName":"How to prevent your hosting account from being hacked","ArticleTypeName":"How_To","Title":"How to prevent your hosting account from being hacked","LiveDateTime":null,"ModifiedDateTime":"02/07/2025","MarkedAsNew":false,"MarkedAsFeatured":false}],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":2194}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","ParentCategoryId":12,"Parent_Category_Name":"Hosting","FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":false,"CreatedDateTime":"06/13/2013 08:34:05","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2194,"CategoryName":"Tips & Tricks"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":9207,"Title":"How to clear cache in different browsers (Mac OS)","ArticleName":"How to clear cache in different browsers (Mac OS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/06/2025"},{"ArticleId":9366,"Title":"Errors 500, 502, 503, 504 and 508. Reasons and ways of fixing","ArticleName":"Errors 500, 502, 503, 504 and 508. Reasons and ways of fixing","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/19/2024"},{"ArticleId":9777,"Title":"How to use TCP traceroute","ArticleName":"How to use TCP traceroute","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/20/2023"},{"ArticleId":9997,"Title":"What is hotlinking and how to prevent it","ArticleName":"What is hotlinking and how to prevent it","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/09/2021"},{"ArticleId":10078,"Title":"How to do a hard refresh in Chrome, Firefox and IE?","ArticleName":"How to do a hard refresh in Chrome, Firefox and IE?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/29/2018"},{"ArticleId":10094,"Title":"How to create and download website backup automatically","ArticleName":"How to create and download website backup automatically","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/27/2025"},{"ArticleId":10222,"Title":"How to configure a dedicated IP address to show the website","ArticleName":"How to configure a dedicated IP address to show the website","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/15/2024"},{"ArticleId":10227,"Title":"How to work with a scan report","ArticleName":"How to work with a scan report","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/11/2024"},{"ArticleId":10266,"Title":"How to connect to remote storage on CentOS server","ArticleName":"How to connect to remote storage on CentOS server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/23/2020"},{"ArticleId":10329,"Title":"How to enable Under attack mode for the domain in Cloudflare account","ArticleName":"How to enable Under attack mode for the domain in Cloudflare account","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":10345,"Title":"How to install CAPTCHA on your website","ArticleName":"How to install CAPTCHA on your website","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/25/2020"},{"ArticleId":10591,"Title":"How to fix the \"DNS server not responding\" error","ArticleName":"How to fix the \"DNS server not responding\" error","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/11/2023"},{"ArticleId":10647,"Title":"How to Fix Error 524","ArticleName":"How to Fix Error 524","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/12/2023"},{"ArticleId":9206,"Title":"How to clear cache in different browsers","ArticleName":"How to clear cache in different browsers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"08/03/2022"},{"ArticleId":9208,"Title":"How to clear cache in different browsers (Mobile OS)","ArticleName":"How to clear cache in different browsers (Mobile OS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"08/03/2022"},{"ArticleId":9209,"Title":"How to clear cache in different browsers (Windows)","ArticleName":"How to clear cache in different browsers (Windows)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/05/2025"},{"ArticleId":9658,"Title":"How to use the Browser Console","ArticleName":"How to use the Browser Console","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/14/2021"},{"ArticleId":397,"Title":"How to clear local DNS cache","ArticleName":"How to clear local DNS cache","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/28/2026"},{"ArticleId":858,"Title":"How to get email headers","ArticleName":"How to get email headers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/31/2026"},{"ArticleId":9242,"Title":"How to prevent your hosting account from being hacked","ArticleName":"How to prevent your hosting account from being hacked","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":9696,"Title":"How to protect your content from being copied","ArticleName":"How to protect your content from being copied","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/09/2021"},{"ArticleId":9541,"Title":"How to optimize hosting account space","ArticleName":"How to optimize hosting account space","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/16/2024"},{"ArticleId":9667,"Title":"What are Traceroute, Ping, Telnet and Nslookup commands?","ArticleName":"What are Traceroute, Ping, Telnet and Nslookup commands?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/05/2024"},{"ArticleId":9568,"Title":"My website is down: what to do?","ArticleName":"My website is down: what to do?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/25/2024"},{"ArticleId":9610,"Title":"What to do when I got an email 'Malicious Attempt to Access Your Hosting Account is Detected'","ArticleName":"What to do when I got an email 'Malicious Attempt to Access Your Hosting Account is Detected'","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":9351,"Title":"\"Deceptive site ahead\" warning - what to do","ArticleName":"\"Deceptive site ahead\" warning - what to do","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/11/2024"}],"AssociatedTags":[],"CategoryId":2194,"CategoryName":"Tips & Tricks"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}How to locate your scan report
----------- SCAN REPORT ----------- TimeStamp: Wed, 26 Feb 2020 01:31:39 -0500 Scanning /home/cPanel_username: '/home/cPanel_username/.bcwfgi.php' # ClamAV detected virus = [YARA.php_malware_hexinject.UNOFFICIAL] '/home/cPanel_username/old/wp-admin/cfgs.php' # Known exploit = [Fingerprint Match] [PHP Exploit] '/home/cPanel_username/old/wp-admin/images/align-lefts.png' # Suspicious image file (hidden script file) '/home/cPanel_username/public_html/assets/asset/js/plugins/editors/codemirror/mode/clike/index.html' # Suspicious file type [application/x-c] '/home/cPanel_username/public_html/assets/asset/js/plugins/uploaders/plupload/files/Moxie.xap' # (compressed file: Moxie.dll [depth: 1]) MS Windows Binary/Executable [application/x-winexec] '/home/cPanel_username/public_html/vendor/laravel/framework/src/Illuminate/Filesystem/Filesystem.php' # Regular expression match = [symlink\s*\(] '/home/cPanel_username/example.com/wp-content/plugins/contact-form-7/wp-contact-form-7.php' # Script version check [OLD] [Contact Form 7 v5.0.5 < v5.1.3] '/home/cPanel_username/example.com/wp-content/themes/weddingvero/auto-install/uploads/espresso/tickets' # World writeable directory ----------- SCAN SUMMARY ----------- Scanned directories: 8221 Scanned files: 77818 Ignored items: 217 Suspicious matches: 893 Viruses found: 743 Fingerprint matches: 85 Data scanned: 5245.76 MB Scan time/item: 0.013 sec Scan time: 1149.580 sec
| Result | Description | Action to take |
|---|---|---|
| # ClamAV detected virus | Antivirus software has found a potentially dangerous file with malware. | Remove the file. |
| # Suspicious file type [application/x-c] # MS Windows Binary/Executable [application/x-winexec] # (compressed file: Moxie.dll [depth: 1]) MS Windows # Binary/Executable [application/x-winexec] # MS-DOS Binary/Executable [application/x-dosexec] | Antivirus software has found Windows binary or executable files. Such files cannot be executed on a Linux-based OS. You would not normally expect to find one within a cPanel account . You can discover a Trojan file among them. | Remove the file. |
| # Linux Binary/Executable [application/x-sharedlib] | Antivirus software has found Linux binary or executable files. Such files can be executed on a Linux-based OS. Still, you would not normally expect to find one within a cPanel account. If a Linux binary or executable file is located in a cPanel account, it is most likely an exploit that remains hidden. | Remove the file. |
| # Known exploit = [Fingerprint Match] | Antivirus software considers a file as an exploit. An exploit can be a program, a piece of code, or even just a string of characters. It takes advantage of a program. Then, this program acts in an unexpected way, which results in undesirable behavior. Also, exploits are maliciously used to gain unauthorized access. | Unless you know the purpose of this file, remove it from your cPanel. If
it is related to installed software and you need it, either clean it or
upload again from a trusted source. PLEASE NOTE: It is strongly recommended that you use content only from the official source. |
| # Symlink to | The file is a symbolic link. It consists of a special type of file that serves as a reference to another file or directory. Some default files require symlinks for the proper work of cPanel services: '/home/cPanel_username/.cagefs/opt/alt/phpXX/link/conf' '/home/cPanel_username/access-logs' '/home/cPanel_username/.cagefs/tmp/mysql.sock' But the custom symlinks (e.g. a symlink to files outside of your cPanel account) may cause serious security breaches. | Pay attention to the custom symlinks. Such files should be removed from your account. Symlinks to default cPanel files can be ignored. |
| # Socket | A socket is typically used to transfer data between two separate processes. You would not expect to normally find one within a cPanel account. | Unless you know the purpose of this file or it is related to the
software installed from the trusted source, remove it from your cPanel. |
| # Regular expression match = [symlink\s*\(] | A file contains 'symlink(s)' expression as a comment or variable. | It is a false-positive. The file can be ignored. |
| # Regular expression match = [\n(?!\s*(//|\#|\*)).*/etc/passwd] | A file contains '/etc/passwd' expression as a comment or variable. | It is a false-positive. The file can be ignored. |
| # Regular expression match = [\n(?!\s*(//|\#|\*)).*\.ssh/] | A file contains '/.ssh' expression as a comment or variable. Such files
are potentially harmful to your account as they allow remote access
using SSH keys. | Unless you know the purpose of this file or it is related to the software installed from the trusted source, remove it from your cPanel. |
| # Universal decode regex match | A file contains some string encoded with a common encoder, e.g. base64. They are often used to hide malicious code. | Unless you know the purpose of this file or it is related to the software installed from the trusted source, remove it from your cPanel. |
| # Script version check [OLD] | The installation, plugin or theme version is outdated. Software updates are important because they check for the bugs and vulnerabilities found in the previous versions. A ‘hole’ in one can affect your entire installation as well as your cPanel account. | Ensure that your installations are up to date. |
| # World writeable directory | Permissions for a directory are set to 777. It is recommended to have default permissions assigned to website files and folders. They are 644 for files and 755 for folders. However, it is safe to have permissions set to 777 for default cPanel folders: /home/cPanel_user/.cagefs/var/cache /home/cPanel_user/.cagefs/var/php /home/cPanel_user/.cagefs/var/run | Update permissions for the indicated directory. |
| # Scan Timeout (30 seconds) while processing | The scan process has been interrupted. | You can put in a request to our Support Team to scan it additionally. |
| # Clamd Error for | Antivirus software considers that the file is located inside the service directory, therefore, it should not be scanned. | The file can be ignored. |
Need help? We're always here for you.