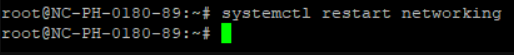
{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":10221,\\\"categoryId\\\":2188}\"":{"body":{"Id":10221,"FriendlyId":"","ArticleTypeId":0,"Title":"Private Network on Dedicated servers","ArticleName":"Private Network on Dedicated servers","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"SW4gdGhpcyBhcnRpY2xlIHlvdSB3aWxsIGZpbmQgYWxsIHRoZSBuZWNlc3NhcnkgaW5mb3JtYXRpb24gcmVnYXJkaW5nIHRoZSBQcml2YXRlIE5ldHdvcmssIFZMQU4uPGJyIC8+PGJyIC8+PHA+PGEgaHJlZj0iI3ZsYW4iPldoYXQgaXMgVkxBTj88L2E+PC9wPjxwPjxhIGhyZWY9IiNiZW5lZml0cyI+VGhlIGJlbmVmaXRzPC9hPjwvcD48cD48YSBocmVmPSIjc2V0dXBfdmxhbiI+SG93IHRvIHNldCB1cCBWTEFOPC9hPjwvcD48cD48YSBocmVmPSIjY29uZmlndXJlX3ZsYW4iPkhvdyB0byBjb25maWd1cmUgeW91ciBzZXJ2ZXIgZm9yIFZMQU48L2E+PC9wPjxwPjxhIGhyZWY9IiNhdmFpbGFibGVfaG9zdHMiPkhvdyB0byBjaGVjayBmb3IgYXZhaWxhYmxlIGhvc3RzPC9hPjwvcD48cD48YSBuYW1lPSJ2bGFuIj48Yj48YnIgLz48L2I+PC9hPjwvcD48cD48YSBuYW1lPSJ2bGFuIj48Yj5XaGF0IGlzIFZMQU4/PC9iPjwvYT48L3A+PGJyIC8+QSBWaXJ0dWFsIExvY2FsIEFyZWEgTmV0d29yayAoVkxBTikgb3IgYSBQcml2YXRlIE5ldHdvcmssIGlzIGEgZ3JvdXAgb2Ygc2VydmVycyB0aGF0IGFsbG93cyBmb3IgY29tbXVuaWNhdGlvbiBiZXR3ZWVuIG90aGVyIHNlcnZlcnMgd2l0aGluIHRoZSBzYW1lIGVudmlyb25tZW50LiBIZXJlLCBkYXRhIGlzIG5vdCBzZW50IHZpYSB0aGUgcHVibGljIG5ldHdvcms7IGluc3RlYWQsIGl0IGlzIHRyYW5zZmVycmVkIHNhZmVseSBhbW9uZyB2aXJ0dWFsIHNlcnZlcnMuIFRoZSB0cmFmZmljIGFtb25nIGRldmljZXMgaXMgc3BsaXQgYWNyb3NzIHR3byBvciBtb3JlIHBoeXNpY2FsIG5ldHdvcmtzIGFuZCB3aXRoIFZMQU4sIHRoYXQgdHJhZmZpYyBpcyBoYW5kbGVkIG1vcmUgZWZmaWNpZW50bHkuPGJyIC8+PGJyIC8+VGhyb3VnaCB2aXJ0dWFsaXphdGlvbiwgeW914oCZcmUgYWJsZSB0byBlZmZlY3RpdmVseSB0dXJuIGEgc2luZ2xlIHBoeXNpY2FsIHNlcnZlciBpbnRvIG11bHRpcGxlIHZpcnR1YWwgc2VydmVycywgZWFjaCBhdmFpbGFibGUgZm9yIHNlcGFyYXRlIHRhc2tzIGFuZCB1c2Vycy48YnIgLz48YnIgLz5UaGUgcmVzdWx0PyBBIFZMQU4gdGhhdCBjYW4gYmUgYWRtaW5pc3RlcmVkIGp1c3QgbGlrZSBhIGxvY2FsIHBoeXNpY2FsIG5ldHdvcmsuPGJyIC8+PGJyIC8+PGJyIC8+PHA+PGEgbmFtZT0iYmVuZWZpdHMiPjxiPlRoZSBiZW5lZml0czwvYj48L2E+PC9wPjxiciAvPkEgUHJpdmF0ZSBOZXR3b3JrIGhhcyBhIHdpZGUgcmFuZ2Ugb2YgYmVuZWZpdHMsIHN1Y2ggYXMgdGhlIGZvbGxvd2luZzo8YnIgLz48YnIgLz48dWw+PGxpPjxiPlNlY3VyaXR5PC9iPi4gVkxBTnMgZW5oYW5jZSBuZXR3b3JrIHNlY3VyaXR5LiBBIHNlcGFyYXRlIHN5c3RlbSB0aGF0IHRyYW5zZmVycyBhbGwgdGhlIHNlbnNpdGl2ZSBkYXRhIHdpdGhpbiB0aGUgaW50ZXJuYWwgbmV0d29yayBjb25uZWN0aW9uIGRlY3JlYXNlcyB0aGUgY2hhbmNlcyB0aGF0IHBlb3BsZSB3aWxsIGdhaW4gYWNjZXNzIHRvIGluZm9ybWF0aW9uIHRoZXkgYXJlIG5vdCBhdXRob3JpemVkIHRvIHNlZS48L2xpPjxsaT48Yj5GYXN0IGRhdGEgdHJhbnNmZXJzPC9iPi4gVkxBTiBhbGxvd3MgeW91IHRvIHRyYW5zZmVyIGRhdGEgZmFzdCBhbmQgc2VjdXJlbHkgd2hlbiB5b3UgdXNlIHlvdXIgb3duIG5ldHdvcmsuIFRoaXMgaW1wcm92ZXMgcGVyZm9ybWFuY2UgYW5kIHJlZHVjZXMgbGF0ZW5jeS48L2xpPjxsaT48Yj5VbmxpbWl0ZWQgY29ubmVjdGlvbnM8L2I+LiBZb3UgY2FuIGNvbm5lY3QgYXMgbWFueSBEZWRpY2F0ZWQgU2VydmVycyBhcyB5b3XigJlkIGxpa2UsIHdpdGhvdXQgYW55IGltcGFjdCBvbiBpdHMgbGV2ZWwgb2Ygc3BlZWQgYW5kIGRhdGEgdHJhZmZpYy48L2xpPjxsaT48Yj5CYW5kd2lkdGggdXNhZ2U8L2I+LiBWTEFOcyBmcmVlIHVwIGJhbmR3aWR0aCBieSBsaW1pdGluZyBub2RlLXRvLW5vZGUgYW5kIGJyb2FkY2FzdCB0cmFmZmljIHRocm91Z2hvdXQgdGhlIG5ldHdvcmsuPC9saT48bGk+PGI+SGlnaCBwZXJmb3JtYW5jZTwvYj4uIEluIG5ldHdvcmtzIHdoZXJlIHRyYWZmaWMgY29uc2lzdHMgb2YgYSBoaWdoIHBlcmNlbnRhZ2Ugb2YgYnJvYWRjYXN0cyBhbmQgbXVsdGljYXN0cywgVkxBTnMgY2FuIHJlZHVjZSB0aGUgbmVlZCB0byBzZW5kIHRoaXMgdHlwZSBvZiB0cmFmZmljIHRvIHVubmVjZXNzYXJ5IGRlc3RpbmF0aW9ucy4gPC9saT48bGk+PGI+VmlydHVhbCBuZXR3b3JrPC9iPi4gU2V0dGluZyB1cCB5b3VyIG93biBuZXR3b3JrIGFsbG93cyB5b3UgdG8gcGxhY2UgbWVtYmVycyBvZiBhIHdvcmtncm91cCB0b2dldGhlciBlYXNpbHkuPC9saT48bGk+PGI+RWFzeSBtYW5hZ2VtZW50PC9iPi4gVXNpbmcgYSBwcml2YXRlIG5ldHdvcmssIGEgZGV2aWNlIGNhbiBiZSBsb2NhdGVkIGFueXdoZXJlIGluIHRoZSA8YSBocmVmPSJodHRwczovL2VuLndpa2lwZWRpYS5vcmcvd2lraS9GdWxseV9zd2l0Y2hlZF9uZXR3b3JrIiBsaW5rdGV4dD0ic3dpdGNoZWQgbmV0d29yayIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfcGFyZW50Ij5zd2l0Y2hlZCBuZXR3b3JrPC9hPiBhbmQgc3RpbGwgYmVsb25nIHRvIHRoZSBzYW1lIGJyb2FkY2FzdCBkb21haW4uIFlvdSBjYW4gbW92ZSBhIHVzZXIgZnJvbSBvbmUgc3dpdGNoIHRvIGFub3RoZXIgc3dpdGNoIGluIHRoZSBzYW1lIG5ldHdvcmsgd2hpbGUga2VlcGluZyB0aGVpciBvcmlnaW5hbCBWTEFOLjwvbGk+PC91bD48ZGl2PjxiciAvPjwvZGl2PjxwPjxhIG5hbWU9InNldHVwX3ZsYW4iPjxiPkhvdyB0byBzZXQgdXAgVkxBTjwvYj48L2E+PC9wPjxiciAvPkR1ZSB0byB0ZWNobmljYWwgcmVzdHJpY3Rpb25zLCBhIFZMQU4gY2Fubm90IGJlIGluc3RhbGxlZCBmcm9tIHlvdXIgc2lkZS4gPGJyIC8+PGJyIC8+SWYgeW91IHdvdWxkIGxpa2UgdG8gc2V0IHVwIGEgUHJpdmF0ZSBOZXR3b3JrIGZvciB5b3VyIERlZGljYXRlZCBTZXJ2ZXIsIHBsZWFzZSByZWFjaCBvdXQgdG8gb3VyIDxiPkhvc3Rpbmc8L2I+IGRlcGFydG1lbnQgdmlhIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vaGVscC1jZW50ZXIvbGl2ZS1jaGF0LyI+TGl2ZSBDaGF0PC9hPiBvciA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvMjI3LzUvaG93LWNhbi1pLXJlcXVlc3Qtc3VwcG9ydC12aWEtZW1haWwvIj5lbWFpbDwvYT4uIE91ciBTdXBwb3J0IFRlYW0gd2lsbCBnbGFkbHkgaGVscCB5b3UgaW5zdGFsbCBWTEFOIGZvciB5b3VyIHNlcnZlcnMgdG8gbWFuYWdlIHlvdXIgb3duIFByaXZhdGUgTmV0d29yay48YnIgLz48YnIgLz48Yj5OT1RFPC9iPjogVkxBTiBjYW4gb25seSBiZSBpbnN0YWxsZWQgaWYgeW91IGhhdmUgPGI+dHdvIG9yIG1vcmU8L2I+IERlZGljYXRlZCBTZXJ2ZXJzIGFuZCBvbmx5IHdpdGggdGhlIDxiPlVzZXItUmVzcG9uc2libGU8L2I+IGFuZCA8Yj5CYXNpYyA8L2I+PGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzkyMTMvMjE4OC93aGF0LWRlZGljYXRlZC1zZXJ2ZXItbWFuYWdlbWVudC1vcHRpb25zLWRvLXlvdS1wcm92aWRlLyIgbGlua3RleHQ9IlNlcnZlciBNYW5hZ2VtZW50IFR5cGVzIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9wYXJlbnQiPlNlcnZlciBNYW5hZ2VtZW50IFR5cGVzPC9hPi48YnIgLz48YnIgLz48YnIgLz48cD48YSBuYW1lPSJjb25maWd1cmVfdmxhbiI+PGI+SG93IHRvIGNvbmZpZ3VyZSB5b3VyIHNlcnZlciBmb3IgVkxBTjwvYj48L2E+PC9wPjxiciAvPkluIG9yZGVyIHRvIGFzc2lnbiBhIHByaXZhdGUgSVAgYWRkcmVzcyB0byB0aGUgVkxBTiBpbnRlcmZhY2UgZXRoMCBvbiBvdXIgZGV2aWNlcywgZm9sbG93IHRoZXNlIHN0ZXBzIGZvciB0aGUgZm9sbG93aW5nIG9wZXJhdGluZyBzeXN0ZW1zIChPUyk6IDxiciAvPjxiciAvPjx1bD48bGk+PGEgaHJlZj0iI1VidW50dV92bGFuIj5VYnVudHU8L2E+PC9saT48bGk+PGEgaHJlZj0iI0RlYmlhbl92bGFuIj5EZWJpYW48L2E+PC9saT48L3VsPjxiciAvPjxkaXY+PHA+PC9wPjxwPjxhIG5hbWU9IlVidW50dV92bGFuIj48Yj5VYnVudHU8YnIgLz48L2I+PC9hPjwvcD4NCjEuIENoZWNrIHRoZSBjb250ZW50cyBvZiB0aGUgZXRoMSBpbnRlcmZhY2U6IDxiciAvPjxiciAvPjxpPmNhdCAvZXRjL25ldHBsYW4vMDEtbmV0Y2ZnLnlhbWwgPC9pPjxiciAvPjxiciAvPjxwPjwvcD48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuNC5wbmciIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PlRoZSBmb2xsb3dpbmcgY29udGVudCBvZiB0aGUgWUFNTCBmaWxlIHNob3VsZCBiZSBwcmVzZW50IHRoZXJlOiANCg0KPHByZT48aT5uZXR3b3JrOg0KICB2ZXJzaW9uOiAyDQogIHJlbmRlcmVyOiBuZXR3b3JrZA0KICBldGhlcm5ldHM6DQogICAgZXRoMToNCiAgICAgIGRoY3A0OiBubw0KICAgICAgZGhjcDY6IG5vDQogICAgICBhZGRyZXNzZXM6IFsyMDkuMTg4LjIxLjI1MC8yNl0NCiAgICAgIGdhdGV3YXk0OiAyMDkuMTg4LjIxLjE5Mw0KICAgICAgbmFtZXNlcnZlcnM6DQogICAgICAgIGFkZHJlc3NlczogWzguOC44LjhdPC9pPjwvcHJlPjwvZGl2PjxwPjwvcD4yLiBGb3Igb3VyIHByaXZhdGUgaW50ZXJmYWNlIGV0aDAsIHdlIHdpbGwgY29weSA8aT4vZXRjL25ldHBsYW4vMDEtbmV0Y2ZnLnlhbWw8L2k+IHRvIDxpPi9ldGMvbmV0cGxhbi8wMi1uZXRjZmcueWFtbDwvaT4gZmlsZSB3aXRoIHRoZSBmb2xsb3dpbmcgY29tbWFuZDogPGJyIC8+PGJyIC8+PGk+Y3AgL2V0Yy9uZXRwbGFuLzAxLW5ldGNmZy55YW1swqAgL2V0Yy9uZXRwbGFuLzAyLW5ldGNmZy55YW1sIDwvaT48YnIgLz48YnIgLz48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuNS5wbmciIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjMuIEFmdGVyIHRoYXQsIG9wZW4gdGhlIFlBTUwgZmlsZSBmb3IgZXRoMCAoL2V0Yy9uZXRwbGFuLzAyLW5ldGNmZy55YW1sKSB3aXRoIHRoZSBlZGl0b3Igb2YgeW91ciBjaG9pY2UgKG1ha2Ugc3VyZSB0byBmb2xsb3cgdGhlIHJ1bGVzIG9mIGhvdyB0byA8YSBocmVmPSJodHRwOi8vZXNzLmtoaHEubmV0L3dpa2kvWUFNTF9UdXRvcmlhbCIgbGlua3RleHQ9ImVkaXQgWUFNTCBkb2N1bWVudHMiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX3BhcmVudCI+ZWRpdCBZQU1MIGRvY3VtZW50czwvYT4pLjxiciAvPjxiciAvPjxiPk5PVEU8L2I+OiBZQU1MIGlzIHZlcnkgc3RyaWN0IHdpdGggaW5kZW50YXRpb24gYW5kIGlzIGNhc2Utc2Vuc2l0aXZlLCBzbyBwbGVhc2UgYmUgYXR0ZW50aXZlIHRvIHRoZSBZQU1MIHN5bnRheC48YnIgLz48YnIgLz48aT5uYW5vIC9ldGMvbmV0cGxhbi8wMi1uZXRjZmcueWFtbDogPC9pPjxiciAvPjwvZGl2PjxwPjwvcD48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuNi5wbmciIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PlJlcGxhY2UgdGhlIGZvbGxvd2luZyB0ZXh0IGRhdGE6IDxiciAvPjxiciAvPjxpPmV0aDEgJmd0OyZndDsgZXRoMDwvaT48YnIgLz48YnIgLz48aT5hZGRyZXNzZXM6IFsyMDkuMTg4LjIxLjI1MC8yNl0gJmd0OyZndDsgYWRkcmVzc2VzOiBbMTkyLjE2OC4xLjEvMjRdPC9pPjxiciAvPjxiciAvPjQuIFJlbW92ZSB0aGUgbGluZXM6IDxiciAvPjxiciAvPjxpPmdhdGV3YXk0PC9pPjo8aT48L2k+PGJyIC8+PGk+bmFtZXNlcnZlcnM8L2k+IGJsb2NrIChpbmNsdWRpbmcgYWRkcmVzc2VzIHRoYXQgZm9sbG93cykuPGJyIC8+PGJyIC8+VGhlIGNvbmZpZ3VyYXRpb24gZmlsZSBzaG91bGQgbG9vayBhcyBmb2xsb3dzOiA8YnIgLz48L2Rpdj48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjcucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj41LiBBZnRlciB0aGUgY29uZmlndXJhdGlvbiBmaWxlIGZvciBldGgwIGhhcyBiZWVuIGNyZWF0ZWQsIGRpc2FibGUgdGhlIHBvcnQgZXRoMCB3aXRoIHRoZSBjb21tYW5kOiA8YnIgLz48YnIgLz48aT5pcCBsaW5rIHNldCBldGgwIGRvd248L2k+PGJyIC8+PGJyIC8+WW91IGNhbiBjaGVjayB0aGUgc3RhdHVzIG9mIHRoZSBpbnRlcmZhY2Ugd2l0aCB0aGUgZm9sbG93aW5nIGNvbW1hbmQ6IDxiciAvPjxiciAvPjxpPmlwIGxpbmsgc2hvdyBldGgwOjwvaT48YnIgLz48YnIgLz48L2Rpdj48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjgucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj42LiBBZnRlciBmb3JjaW5nIHNodXRkb3duLCBhcHBseSB0aGUgbmV3IGNvbmZpZ3VyYXRpb24gdXNpbmcgdGhlIGNvbW1hbmQ6IDxiciAvPjxiciAvPjxpPm5ldHBsYW4gYXBwbHk8L2k+PGJyIC8+PGJyIC8+Ny4gQ2hlY2sgaWYgdGhlIElQIGFkZHJlc3MgaGFzIGJlZW4gYWRkZWQgdG8gdGhlIGludGVyZmFjZTogPGJyIC8+PGJyIC8+PGk+aXAgYTwvaT46IDxiciAvPjxiciAvPjwvZGl2PjxwPjwvcD48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuXzkucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+WW91IHdpbGwgdGhlbiBuZWVkIHRvIGNoZWNrIGZvciBldGgwIGF0IHRoZSBvdXRwdXQ6PGJyIC8+PHA+PC9wPjxkaXY+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL3ZsYW5fMTAucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5BcyBsb25nIGFzIHRoZSBzdGF0ZSBpcyAiVVAiIGFuZCBzZXQgaW50ZXJuYWwgSVAgYWRkcmVzcyBpcyBwcmVzZW50LCB5b3UgYXJlIGdvb2QgdG8gZ28uIDxiciAvPjxiciAvPjguIE9uIHRoZSBob3N0IDIsIHBlcmZvcm0gdGhlIHNhbWUgb3BlcmF0aW9ucywgb25seSBzZXQgdGhlIGludGVybmFsIElQIGFkZHJlc3MgdG8gYW5vdGhlciB2YWx1ZSwgZGlmZmVyZW50IGZyb20gdGhlIGV4aXN0aW5nIGhvc3RzIHdpdGhpbiB0aGUgc2FtZSBzdWJuZXR3b3JrIC8yNC48YnIgLz48YnIgLz45LiBBZnRlciB0aGUgY29uZmlndXJhdGlvbiBoYXMgYmVlbiBwZXJmb3JtZWQgb24gdGhlIGJvdGggc2VydmVycywgZW5zdXJlIHRoYXQgdGhlIGhvc3RzIGFyZSBhdmFpbGFibGUgZm9yIGVhY2ggb3RoZXIgKGxpbmsgdG8gdGhlIGxhc3Qgc2VjdGlvbikuPGJyIC8+PGJyIC8+PGJyIC8+PHA+PGEgbmFtZT0iRGViaWFuX3ZsYW4iPjxiPkRlYmlhbjwvYj48L2E+PC9wPjxiciAvPjEuIENoZWNrIHRoZSBjb250ZW50cyBvZiB0aGUgaW50ZXJmYWNl4oCZcyBjb25maWd1cmF0aW9uIGZpbGU6IDxiciAvPjxiciAvPjxpPmNhdCAvZXRjL25ldHdvcmsvaW50ZXJmYWNlczwvaT48YnIgLz48YnIgLz5UaGUgaW5pdGlhbCBmaWxlIHNob3VsZCBjb250YWluIHRoZSBmb2xsb3dpbmcgaW5mb3JtYXRpb246IDxiciAvPsKgPGJyIC8+PC9kaXY+PHA+PC9wPjxkaXY+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL3ZsYW4xMS5wbmciIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjIuIE9wZW4gdGhlIGZpbGUgd2l0aCB5b3VyIGZhdm9yaXRlIHRleHQgZWRpdG9yIGFuZCBhbWVuZCB0aGUgZm9sbG93aW5nIGxpbmVzIHRvIHRoZSBlbmQgb2YgdGhlIGZpbGU6IDxiciAvPjxiciAvPjxpPm5hbm8gL2V0Yy9uZXR3b3JrL2ludGVyZmFjZXMgPC9pPjxiciAvPjxiciAvPjMuIEFkZCB0aGUgbmVjZXNzYXJ5IGRhdGEgYW5kIHNhdmUgdGhlIGNoYW5nZXM6wqA8L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxwPjwvcD48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuMTIucG5nIiAvPjxiciAvPjwvZGl2PjxkaXY+PHByZT48aT4jZXRoMA0KYXV0byBldGgwDQppZmFjZSBldGgwIGluZXQgc3RhdGljDQpuYW1lIFZMQU4NCmFkZHJlc3MgMTkyLjE2OC4xLjINCm5ldG1hc2sgMjU1LjI1NS4yNTUuMA0KYWxsb3ctaG90cGx1ZzwvaT48L3ByZT48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxwIGRpcj0ibHRyIiBzdHlsZT0ibGluZS1oZWlnaHQ6MS4zODttYXJnaW4tdG9wOjBwdDttYXJnaW4tYm90dG9tOjBwdDsiIGlkPSJkb2NzLWludGVybmFsLWd1aWQtZmE3N2M1YzMtN2ZmZi1jM2RkLWM4YTUtYWQ1YTBhYWRiYTQ2Ij48c3BhbiBzdHlsZT0iZm9udC1zaXplOjExcHQ7Zm9udC1mYW1pbHk6QXJpYWw7Y29sb3I6IzAwMDAwMDtiYWNrZ3JvdW5kLWNvbG9yOnRyYW5zcGFyZW50O2ZvbnQtd2VpZ2h0OjQwMDtmb250LXN0eWxlOm5vcm1hbDtmb250LXZhcmlhbnQ6bm9ybWFsO3RleHQtZGVjb3JhdGlvbjpub25lO3ZlcnRpY2FsLWFsaWduOmJhc2VsaW5lO3doaXRlLXNwYWNlOnByZTt3aGl0ZS1zcGFjZTpwcmUtd3JhcDsiPlRoZSBmaWxlIHNob3VsZCBsb29rIGFzIGZvbGxvd3M6IDxiciAvPjwvc3Bhbj48L3A+PHA+PC9wPjxkaXY+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL3ZsYW4xMy5wbmciIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjQuIEFmdGVyIHRoYXQsIHJlc3RhcnQgdGhlIG5ldHdvcmtpbmcgd2l0aCB0aGUgZm9sbG93aW5nIGNvbW1hbmQ6IDxiciAvPjxiciAvPjxpPnN5c3RlbWN0bCByZXN0YXJ0IG5ldHdvcmtpbmc8L2k+OiA8YnIgLz48YnIgLz48L2Rpdj48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjE0LnBuZyIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+NS4gT25jZSByZXN0YXJ0ZWQsIGNoZWNrIHRoZSBpbnRlcmZhY2UgcGFyYW1ldGVyczogPGJyIC8+PGJyIC8+PGk+aXAgYTwvaT46IDxiciAvPjwvZGl2PjxiciAvPjxwPjwvcD48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuMTUucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj42LiBZb3Ugd2lsbCBuZWVkIHRvIGNoZWNrIGZvciBldGgwIGF0IHRoZSBvdXRwdXQ6PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjE2LnBuZyIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PkFzIGxvbmcgYXMgdGhlIHN0YXRlIGlzICJVUCIgYW5kIHRoZSBzZXQgaW50ZXJuYWwgSVAgYWRkcmVzcyBpcyBwcmVzZW50LCB5b3UgYXJlIGdvb2QgdG8gZ28uPGJyIC8+PGJyIC8+PGJyIC8+PHA+PGEgbmFtZT0iYXZhaWxhYmxlX2hvc3RzIj48Yj5Ib3cgdG8gY2hlY2sgZm9yIGF2YWlsYWJsZSBob3N0czwvYj48L2E+PC9wPjxiciAvPkFmdGVyIHRoZSBjb25maWd1cmF0aW9uIGhhcyBiZWVuIHBlcmZvcm1lZCBvbiBib3RoIHNlcnZlcnMsIGVuc3VyZSB0aGF0IHRoZSBob3N0cyBhcmUgYXZhaWxhYmxlIHRvIGVhY2ggb3RoZXIgYnkgdXRpbGl6aW5nIDxiPnBpbmc8L2I+IGNvbW1hbmQgYW5kIDxiPnRjcGR1bXA8L2I+OiA8YnIgLz48YnIgLz7CoFNlcnZlcjE6IDxpPnBpbmcgSVAgYWRkcmVzczwvaT48YnIgLz48YnIgLz48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjE3LnBuZyIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+U2VydmVyMjogPGk+dGNwZHVtcCAtaSBldGgwIGljbXA8L2k+PGJyIC8+PC9kaXY+PGJyIC8+PHA+PC9wPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuMTgucG5nIiAvPjxwPjwvcD5BbmQgdmljZSB2ZXJzYTo8YnIgLz48YnIgLz7CoFNlcnZlcjI6IDxpPnBpbmcgSVAgYWRkcmVzczwvaT48YnIgLz48YnIgLz48ZGl2PjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS92bGFuMTkucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5TZXJ2ZXIxOiA8aT50Y3BkdW1wIC1pIGV0aDAgaWNtcDwvaT48YnIgLz48L2Rpdj48cD48L3A+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvdmxhbjIwLnBuZyIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PlRoaXMgd3JhcHMgdXAgdGhlIFZMQU4gaW50ZXJmYWNlIHNldHVwIGZvciB5b3VyIE9TLCB3aGljaCBpcyBiYXNlZCBvbiB0d28gbmV0d29yayBob3N0cy4gRm9yIG1vcmUgdGhhbiB0d28gbmV0d29yayBob3N0cywgd2UgcmVjb21tZW5kIHVzaW5nIHRoZSBhdmFpbGFibGUgSVAgYWRkcmVzcyBmcm9tIGEgcHJpdmF0ZSBzdWJuZXQgdGhhdCBpcyBub3QgYXNzaWduZWQgdG8gdGhlIGV4aXN0aW5nIGhvc3RzLjxiciAvPjxiciAvPldlbGwgZG9uZSEgPGJyIC8+PHA+PC9wPjwvZGl2Pg==","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2025-02-07T13:03:21.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2020-04-29T10:08:45.0000000","ApprovalDatetime":"2020-04-29T12:14:01.0000000","RequestCount":23207,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":0,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2188,"CategoryName":"Dedicated Server"}],"AssociatedCategories":[{"CategoryId":2188,"CategoryName":"Dedicated Server","CategoryDisplayName":"HostingDedicated Server"}],"AssociatedTags":[{"TagId":82690,"Tag":"dedicated servers vlan setup p"}],"RelatedArticles":[],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":2188}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","ParentCategoryId":12,"Parent_Category_Name":"Hosting","FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":false,"CreatedDateTime":"04/25/2013 17:59:30","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2188,"CategoryName":"Dedicated Server"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":9979,"Title":"What operating systems are available with a VPS/Dedicated Server","ArticleName":"What operating systems are available with a VPS/Dedicated Server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/17/2025"},{"ArticleId":9989,"Title":"What is the difference between Shared Hosting and Dedicated server","ArticleName":"What is the difference between Shared Hosting and Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/24/2024"},{"ArticleId":10054,"Title":"What is an Outlet (Clearance) Dedicated server?","ArticleName":"What is an Outlet (Clearance) Dedicated server?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/19/2019"},{"ArticleId":10084,"Title":"Resetting Dedicated server root password via Virtual Console","ArticleName":"Resetting Dedicated server root password via Virtual Console","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/17/2025"},{"ArticleId":10085,"Title":"How to set up automated backups for VPS and Dedicated server","ArticleName":"How to set up automated backups for VPS and Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/18/2022"},{"ArticleId":10107,"Title":"How to set up a DNS zone on a server without cPanel","ArticleName":"How to set up a DNS zone on a server without cPanel","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":10108,"Title":"Resolving Disk Space issues on a VPS/Dedicated server","ArticleName":"Resolving Disk Space issues on a VPS/Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/04/2019"},{"ArticleId":10202,"Title":"How to install Node.js on a VPS or a Dedicated server","ArticleName":"How to install Node.js on a VPS or a Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/20/2024"},{"ArticleId":10220,"Title":"What is a Dedicated Server?","ArticleName":"What is a Dedicated Server?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/29/2020"},{"ArticleId":10221,"Title":"Private Network on Dedicated servers","ArticleName":"Private Network on Dedicated servers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":10231,"Title":"Is there any downtime when I change between Shared Hosting plans and/or Reseller Hosting plans?","ArticleName":"Is there any downtime when I change between Shared Hosting plans and/or Reseller Hosting plans?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"},{"ArticleId":10232,"Title":"How can I change the operating system on my VPS/Dedicated Server","ArticleName":"How can I change the operating system on my VPS/Dedicated Server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/19/2024"},{"ArticleId":10295,"Title":"SATA 3 vs M.2 vs NVMe SSD - Faster future for everyone","ArticleName":"SATA 3 vs M.2 vs NVMe SSD - Faster future for everyone","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"08/28/2020"},{"ArticleId":10319,"Title":"How to install VestaCP on a VPS/Dedicated Server","ArticleName":"How to install VestaCP on a VPS/Dedicated Server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":10328,"Title":"How to install Linux, Apache, MariaDB, PHP stack (LAMP) on AlmaLinux and host a website","ArticleName":"How to install Linux, Apache, MariaDB, PHP stack (LAMP) on AlmaLinux and host a website","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/21/2025"},{"ArticleId":10330,"Title":"How to install Linux, Apache, MariaDB, PHP stack (LAMP) on Ubuntu and host a website","ArticleName":"How to install Linux, Apache, MariaDB, PHP stack (LAMP) on Ubuntu and host a website","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/09/2020"},{"ArticleId":10596,"Title":"How does a dedicated server work?","ArticleName":"How does a dedicated server work?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/09/2024"},{"ArticleId":10768,"Title":"What is Proxmox VE?","ArticleName":"What is Proxmox VE?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/16/2026"},{"ArticleId":9409,"Title":"How to configure initial WHM settings (VPS and Dedicated server)","ArticleName":"How to configure initial WHM settings (VPS and Dedicated server)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/15/2021"},{"ArticleId":9661,"Title":"How to manage features in WHM","ArticleName":"How to manage features in WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/12/2022"},{"ArticleId":9309,"Title":"How to access IPMI for dedicated servers","ArticleName":"How to access IPMI for dedicated servers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":207,"Title":"How to set up personal nameservers (VPS and Dedicated servers)","ArticleName":"How to set up personal nameservers (VPS and Dedicated servers)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/01/2022"},{"ArticleId":9211,"Title":"How to order cPanel/WHM for a VPS/Dedicated server","ArticleName":"How to order cPanel/WHM for a VPS/Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/13/2026"},{"ArticleId":9212,"Title":"How to order Softaculous for a dedicated server/VPS","ArticleName":"How to order Softaculous for a dedicated server/VPS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"},{"ArticleId":9213,"Title":"What Dedicated Server Management options do you provide?","ArticleName":"What Dedicated Server Management options do you provide?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/30/2025"},{"ArticleId":9215,"Title":"How to upgrade RAM/bandwidth/disk space on a VPS/Dedicated server","ArticleName":"How to upgrade RAM/bandwidth/disk space on a VPS/Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/13/2026"},{"ArticleId":9223,"Title":"How to order additional IP addresses for a Dedicated Server","ArticleName":"How to order additional IP addresses for a Dedicated Server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/06/2025"},{"ArticleId":9227,"Title":"How to increase port speed on a Dedicated server","ArticleName":"How to increase port speed on a Dedicated server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2024"},{"ArticleId":9224,"Title":"How to order additional bandwidth for a Dedicated Server","ArticleName":"How to order additional bandwidth for a Dedicated Server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/06/2025"},{"ArticleId":9221,"Title":"How much does it cost to transfer the content of my account to a Dedicated server?","ArticleName":"How much does it cost to transfer the content of my account to a Dedicated server?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"},{"ArticleId":9225,"Title":"Backups for Dedicated servers with Complete management","ArticleName":"Backups for Dedicated servers with Complete management","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/07/2023"},{"ArticleId":9942,"Title":"How to reboot VPS or dedicated server through WHM","ArticleName":"How to reboot VPS or dedicated server through WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/16/2021"},{"ArticleId":9944,"Title":"How to change the root password via WHM","ArticleName":"How to change the root password via WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/07/2025"},{"ArticleId":9849,"Title":"How to change PHP configuration on a VPS/Dedicated server (for EasyApache 4)","ArticleName":"How to change PHP configuration on a VPS/Dedicated server (for EasyApache 4)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/23/2024"},{"ArticleId":9742,"Title":"What is a CXS License?","ArticleName":"What is a CXS License?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"08/18/2025"},{"ArticleId":9660,"Title":"How to work with cPHulk","ArticleName":"How to work with cPHulk","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/30/2021"},{"ArticleId":9662,"Title":"How to work with the CSF plugin","ArticleName":"How to work with the CSF plugin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/26/2024"},{"ArticleId":9670,"Title":"How to install Softaculous on a VPS/Dedicated server with cPanel/WHM","ArticleName":"How to install Softaculous on a VPS/Dedicated server with cPanel/WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/21/2021"},{"ArticleId":9672,"Title":"How to install the Vade Retro Plugin on VPS/Dedicated server with cPanel/WHM","ArticleName":"How to install the Vade Retro Plugin on VPS/Dedicated server with cPanel/WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/14/2021"},{"ArticleId":9549,"Title":"RAID technology – Explained","ArticleName":"RAID technology – Explained","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/06/2025"}],"AssociatedTags":[{"TagId":27348,"Tag":"cxs"}],"CategoryId":2188,"CategoryName":"Dedicated Server"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}How to configure your server for VLAN
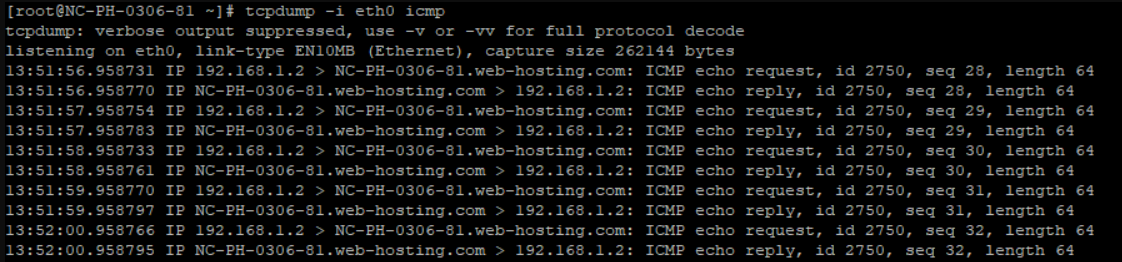
How to check for available hosts
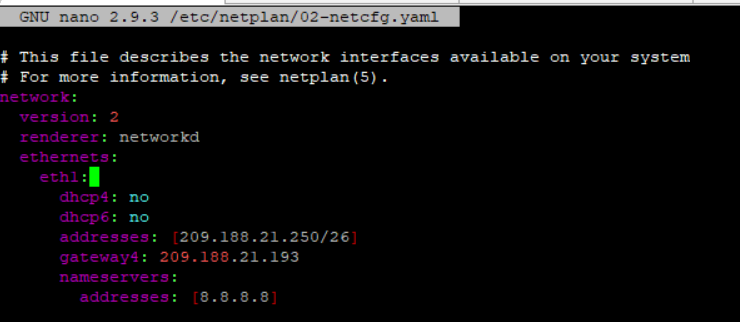
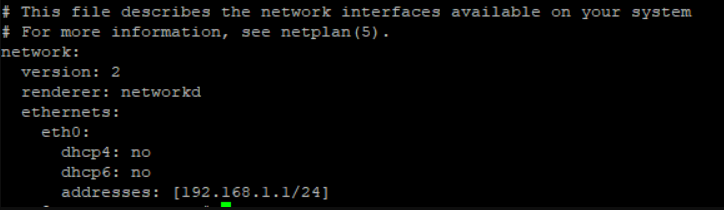
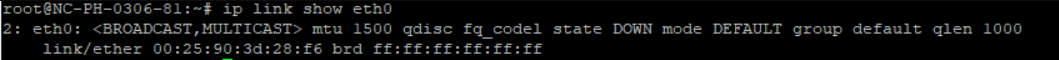
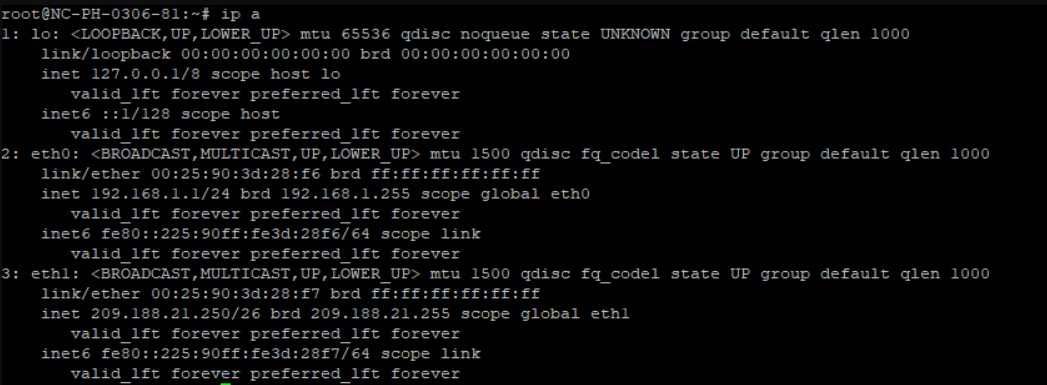
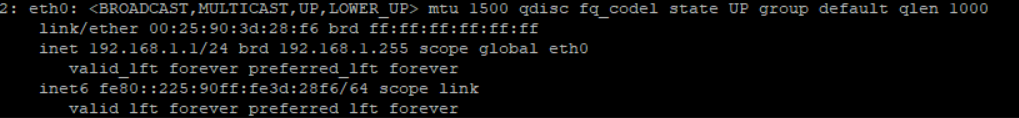
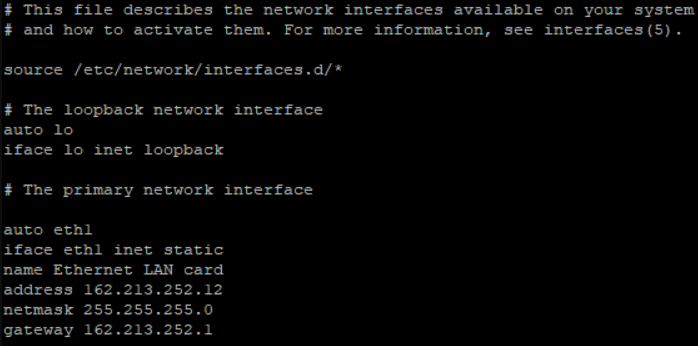
How to configure your server for VLAN
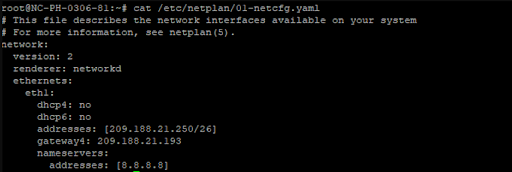
network:
version: 2
renderer: networkd
ethernets:
eth1:
dhcp4: no
dhcp6: no
addresses: [209.188.21.250/26]
gateway4: 209.188.21.193
nameservers:
addresses: [8.8.8.8]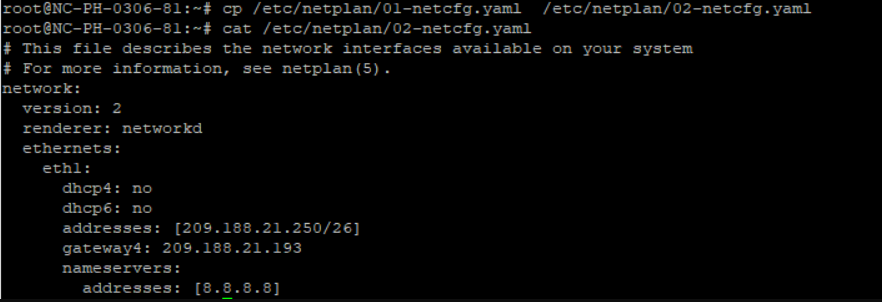
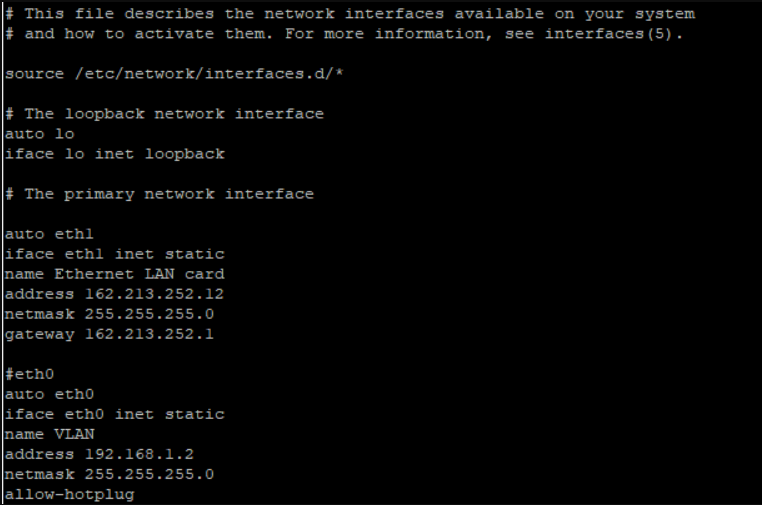
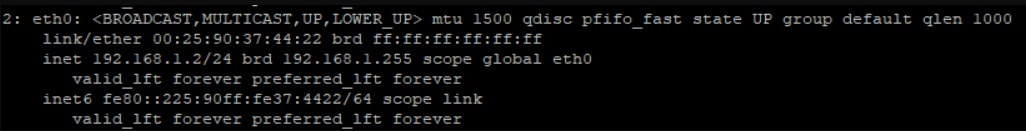
#eth0 auto eth0 iface eth0 inet static name VLAN address 192.168.1.2 netmask 255.255.255.0 allow-hotplug
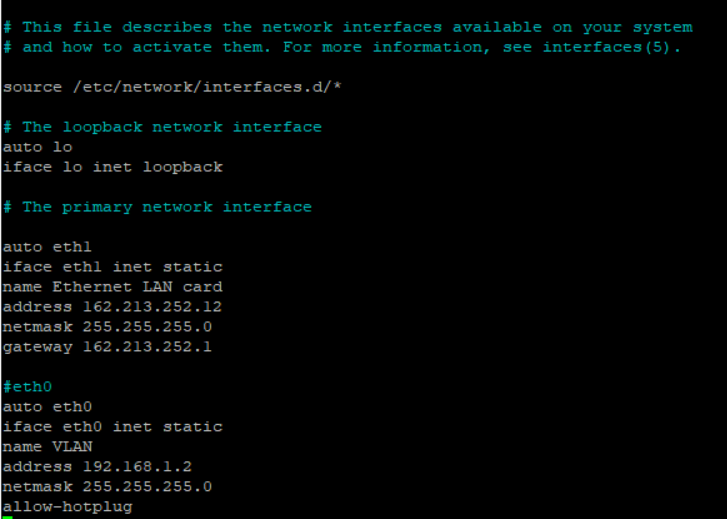
The file should look as follows:
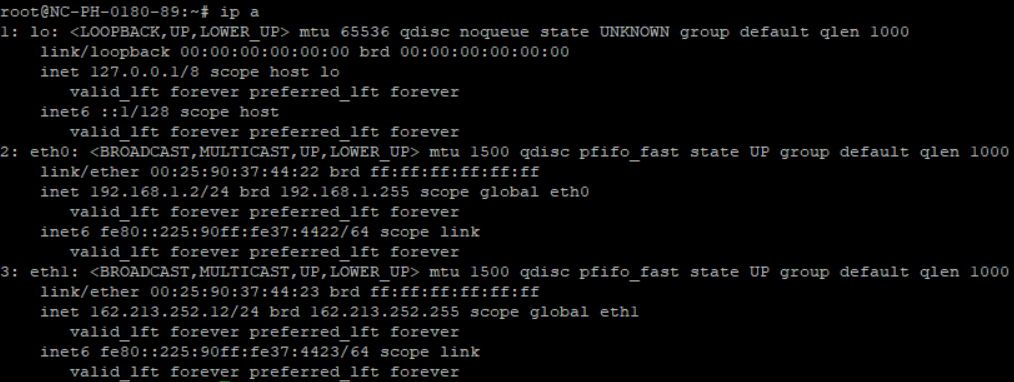
How to check for available hosts
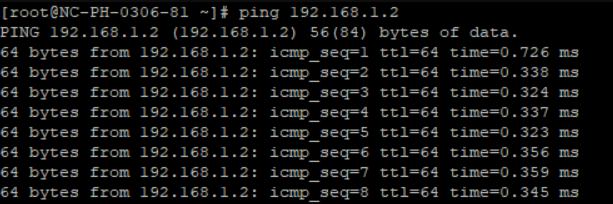
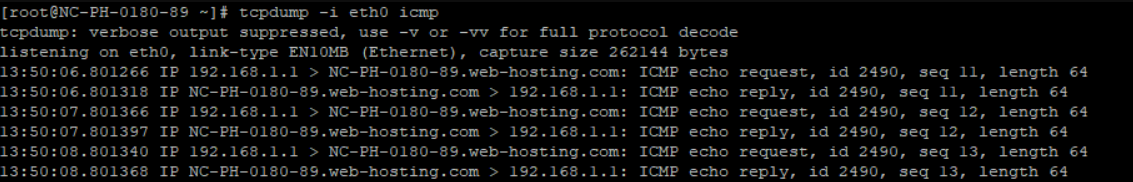 And vice versa:
And vice versa: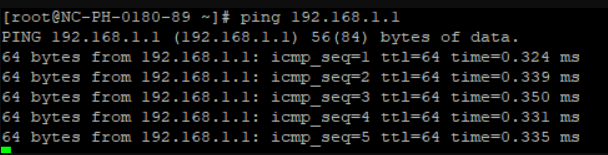
Need help? We're always here for you.