{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":9593,\\\"categoryId\\\":33}\"":{"body":{"Id":9593,"FriendlyId":"","ArticleTypeId":0,"Title":"Installing an SSL certificate on Amazon Web Services (AWS)","ArticleName":"Installing an SSL certificate on Amazon Web Services (AWS)","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"QW1hem9uIFdlYiBTZXJ2aWNlcyBwcm92aWRlcyBob3N0aW5nIGluc3RhbmNlcyB0aGF0IGNhbiBiZSB1c2VkIHRvIGhvc3QgYm90aCBjb21tb24gc2VydmVycyBhbmQgYXBwbGljYXRpb25zLCBhcyB3ZWxsIGFzIHNvbWUgc3BlY2lmaWMgYWRkaXRpb25hbCBzZXJ2aWNlcy4gQmVjYXVzZSBvZiB0aGlzLCB0aGVyZSBhcmUgbXVsdGlwbGUgb3B0aW9ucyBmb3IgaW5zdGFsbGluZyBhbiBTU0wgY2VydGlmaWNhdGUgb24gQVdTLg0KPGJyIC8+PGJyIC8+PGRpdj5UaGlzIGFydGljbGUgZGVzY3JpYmVzIGhvdyB0byBpbnN0YWxsIHlvdXIgU1NMIGNlcnRpZmljYXRlIG9uIHNldmVyYWwgc3BlY2lmaWMgQW1hem9uLXJlbGF0ZWQgYXBwbGljYXRpb25zIG9yIHNlcnZpY2VzLiBCZWxvdyBpcyB0aGUgbWFpbiBjb250ZW50IG9mIHRoZSBhcnRpY2xlOjxiciAvPjxiciAvPjwvZGl2Pjx1bD48bGk+PGEgaHJlZj0iIzEiPlNvbWUgcHJlcmVxdWlzaXRlIGluZm9ybWF0aW9uPC9hPjwvbGk+PGxpPjxhIGhyZWY9IiMyIj5FbGFzdGljIENvbXB1dGUgQ2xvdWQgKEVDMik8L2E+PC9saT48bGk+PGEgaHJlZj0iIzMiPkVsYXN0aWMgTG9hZCBCYWxhbmNlciAoRUxCKTwvYT48L2xpPjxsaT48YSBocmVmPSIjNCI+QVdTIEFQSSBHYXRld2F5PC9hPjwvbGk+PGxpPjxhIGhyZWY9IiM1Ij5BbWF6b24gQ2xvdWRGcm9udDwvYT48L2xpPjwvdWw+PGJyIC8+PHVsPjwvdWw+PGgyIGlkPSIxIj5Tb21lIHByZXJlcXVpc2l0ZSBpbmZvcm1hdGlvbjwvaDI+Rm9yIFNTTCBpbnN0YWxsYXRpb24geW91IGdlbmVyYWxseSBuZWVkIHRocmVlIGNvbXBvbmVudHM6IGEgY2VydGlmaWNhdGUsIGFuIGludGVybWVkaWF0ZSBjZXJ0aWZpY2F0ZSBjaGFpbiAoQ0EtYnVuZGxlKSBhbmQgYSBQcml2YXRlIGtleS48ZGl2PjxiciAvPjwvZGl2Pjx1bD48bGk+PGI+U1NMIENlcnRpZmljYXRlczwvYj4gYXJlIHNlbnQgYXMgYSBQRU0tZm9ybWF0dGVkIGZpbGUgd2l0aCBhIDxpPi5jcnQ8L2k+IGV4dGVuc2lvbi4gSWYgdGhlIGV4dGVuc2lvbnMgYXJlIG5vdCBzaG93biBpbiB5b3VyIHN5c3RlbSBieSBkZWZhdWx0IGZvciBhbGwgZmlsZXMsIGFuIFNTTCB3aWxsIGhhdmUgPGk+IlNlY3VyaXR5IGNlcnRpZmljYXRlPC9pPiIgaW4gdGhlIGZpbGUgZGVzY3JpcHRpb24uIFRoZSBzYW1lIGZpbGUgY2FuIGJlIGFsc28gZG93bmxvYWRlZCA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTQ2NC82OS9jYW4taS1kb3dubG9hZC1hbi1pc3N1ZWQtY2VydGlmaWNhdGUtb24teW91ci1zaXRlIiBsaW5rdGV4dD0idGhpcyB3YXkiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj50aGlzIHdheTwvYT4uPGJyIC8+PGJyIC8+SW5zaWRlIHRoZSBmaWxlIHRoZXJlIGlzIGEgY29kZSBsaWtlIHRoaXM6PGJyIC8+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2F3c18xLnBuZyIgLz48L2xpPjxsaT5BbiA8Yj5JbnRlcm1lZGlhdGUgY2VydGlmaWNhdGUgY2hhaW4gKENBLWJ1bmRsZSk8L2I+IGlzIGFsc28gc2VudCBpbiBhIFBFTS1mb3JtYXQgZmlsZSwgYnV0IHRoaXMgZmlsZSBoYXMgYSA8aT4uY2EtYnVuZGxlPC9pPiBleHRlbnNpb24uIEluc2lkZSB0aGUgZmlsZSwgdGhlcmUgYXJlIG5vcm1hbGx5IG9uZSBvciB0d28gY29kZXMgc2ltaWxhciB0byB0aGUgY2VydGlmaWNhdGUuIFRoZSBDQS1idW5kbGUsIGFzIHdpdGggdGhlIGNlcnRpZmljYXRlLCBpcyB1c3VhbGx5IGluIHRoZSBTU0wgYXJjaGl2ZSB5b3UgcmVjZWl2ZSBhZnRlciBTU0wgYWN0aXZhdGlvbi4gSXQgY2FuIGFsc28gYmUgZG93bmxvYWRlZCA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLzkzOTMvNjkvd2hlcmUtZG8taS1maW5kLXNzbC1jYS1idW5kbGUvIiBsaW5rdGV4dD0iaGVyZSIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPmhlcmU8L2E+LjxiciAvPjxiciAvPjwvbGk+PGxpPkEgPGI+UHJpdmF0ZSBrZXkgPC9iPmlzIGdlbmVyYXRlZCBhbG9uZyB3aXRoIHRoZSBjZXJ0aWZpY2F0ZSBzaWduaW5nIHJlcXVlc3QgKENTUikgdXNlZCB0byBhY3RpdmF0ZSB5b3VyIFNTTC4gSWYgeW91IGdlbmVyYXRlZCB0aGUgQ1NSIG9uIHlvdXIgc2VydmVyLCB0aGUga2V5IGlzIHNhdmVkIGluIHRoZSBzYW1lIHBsYWNlLiBJdCBoYXMgLjxpPmtleSA8L2k+ZXh0ZW5zaW9uLjxiciAvPjxiciAvPkl0IGNvbnRhaW5zIGEgY29kZSBsaWtlIHRoaXM6PGJyIC8+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2F3c18yLnBuZyIgLz48L2xpPjwvdWw+PGRpdj5PbiB5b3VyIHNlcnZlciwgdGhlIGNvbnRlbnQgb2YgdGhlIGZpbGVzIGNhbiBiZSBjaGVja2VkIHVzaW5nIHRoZSBjYXQgY29tbWFuZCAoc3BlY2lmeSB0aGUgYWN0dWFsIGZpbGUgbmFtZSBpbiB5b3VyIGNvbW1hbmQpOjxiciAvPjxiciAvPjwvZGl2PjxkaXY+PGNvZGU+PGI+Y2F0IGV4YW1wbGUuY3J0PC9iPjwvY29kZT48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+T24gYSBsb2NhbCBtYWNoaW5lLCB5b3UgY2FuIHJpZ2h0LWNsaWNrIG9uIHRoZSBmaWxlLCBzZWxlY3QgPGI+T3BlbiB3aXRoPC9iPiwgYW5kIGNob29zZSBhbnkgcGxhaW4gdGV4dCBlZGl0b3IuPGJyIC8+PGJyIC8+PC9kaXY+PGRpdj5UaGUgYWZvcmVtZW50aW9uZWQgU1NMIGNvbXBvbmVudHMgd2lsbCBzb21ldGltZXMgbmVlZCB0byBiZSB1cGxvYWRlZCBhcyBmaWxlcyBvciB1cGxvYWRlZCBhcyBjb2RlcywgZGVwZW5kaW5nIG9uIHRoZSBwYXJ0aWN1bGFyIEFtYXpvbiBzZXJ2aWNlIHlvdSB1c2UuPGJyIC8+PGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48aDIgaWQ9IjIiPkVsYXN0aWMgQ29tcHV0ZSBDbG91ZCAoRUMyKTwvaDI+PGRpdj5JZiB5b3UgaGF2ZSBFQzIsIGl0IGdlbmVyYWxseSBtZWFucyB0aGF0IGEgc2VwYXJhdGUgd2ViLCBtYWlsIG9yIGFwcGxpY2F0aW9uIHNlcnZlciBpcyBpbnN0YWxsZWQsIGFuZCB0aGUgU1NMIHNob3VsZCBiZSBpbnN0YWxsZWQgb24gdGhhdCBzZXJ2ZXIuIEZvciBtb3JlIGluZm9ybWF0aW9uIG9uIGluc3RhbGxpbmcgU1NMIGNlcnRpZmljYXRlcywgeW91IGNhbiByZWZlciB0byBpbnN0cnVjdGlvbnMgPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4Lzc5NS82OS9ob3ctdG8taW5zdGFsbC1zc2wtY2VydGlmaWNhdGVzIiBsaW5rdGV4dD0iaGVyZSIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPmhlcmU8L2E+LjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5UaGluZ3Mgd2lsbCBkaWZmZXIgc2xpZ2h0bHkgaWYgeW91IHVzZSB0aGUgQW1hem9uIExpbnV4IEFNSS48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+QW1hem9uIExpbnV4IGlzIGEgc3BlY2lmaWMgTGludXggZGlzdHJpYnV0aW9uIHByb3ZpZGVkIGJ5IEFtYXpvbi4gSXQgaXMgbm9ybWFsbHkgYmFzZWQgb24gQ2VudE9TIExpbnV4IHdpdGggdGhlIEFwYWNoZSBzZXJ2ZXIgaW5zdGFsbGVkICh0aG91Z2ggYSBEZWJpYW4tYmFzZWQgdmVyc2lvbiBhbHNvIGV4aXN0cykuPC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2Pk9uIEFtYXpvbiBMaW51eCAyLCB0aGUgaW5zdGFsbGF0aW9uIHByb2Nlc3MgaXMgZXhhY3RseSB0aGUgc2FtZSBhcyBub3JtYWwgU1NMIGluc3RhbGxhdGlvbiA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTQyMy8zMy9pbnN0YWxsaW5nLWFuLXNzbC1jZXJ0aWZpY2F0ZS1vbi1hcGFjaGUiIGxpbmt0ZXh0PSJvbiB0aGUgQXBhY2hlIHNlcnZlciBvbiBDZW50T1MiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj5vbiB0aGUgQXBhY2hlIHNlcnZlciBvbiBDZW50T1M8L2E+LjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5Gb3Igb3RoZXIgdmVyc2lvbnMgb2YgQW1hem9uIExpbnV4LCB0aGVyZSBpcyBvbmUgcGVjdWxpYXJpdHkuIFRvIHJ1biBhbiBlbmNyeXB0ZWQgSFRUUFMgY29ubmVjdGlvbiBvbiBhbiBBcGFjaGUgd2ViIHNlcnZlciwgPGk+bW9kX3NzbDwvaT4gbmVlZHMgdG8gYmUgaW5zdGFsbGVkIHdpdGggdGhlIGhlbHAgb2YgYSBzbGlnaHRseSBkaWZmZXJlbnQgY29tbWFuZCB0byB0aGUgb25lIHVzdWFsbHkgdXNlZCBvbiBBcGFjaGU6PGJyIC8+PGJyIC8+PC9kaXY+PGRpdj48Y29kZT48Yj5zdWRvIHl1bSBpbnN0YWxsIC15IG1vZDI0X3NzbDwvYj48L2NvZGU+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PlRoZSBkZWZhdWx0IFNTTCBjb25maWd1cmF0aW9uIGZpbGUgbG9jYXRpb24gb24gTGludXggQU1JIGlzIDxiPi9ldGMvaHR0cGQvY29uZi5kL3NzbC5jb25mPC9iPi4gQWxsIHRoZSBjaGFuZ2VzIHJlcXVpcmVkIHRvIGluc3RhbGwgYW4gU1NMIGNhbiBiZSBtYWRlIHdpdGhpbiB0aGlzIGZpbGUuPGJyIC8+PGJyIC8+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48aDIgaWQ9IjMiPkVsYXN0aWMgTG9hZCBCYWxhbmNlciAoRUxCKTwvaDI+PGRpdj5BIGxvYWQgYmFsYW5jZXIgaXMgYSBzcGVjaWZpYyBzZXJ2aWNlIHRoYXQgYWxsb3dzIHRoZSBtYW5hZ2luZyBvZiB0cmFmZmljIGFjcm9zcyBzZXZlcmFsIGhvc3RpbmcgaW5zdGFuY2VzLiBBbWF6b24gcHJvdmlkZXMgYSBsb2FkIGJhbGFuY2VyIHNlcnZpY2UgdGhhdCBjYW4gYmUgc2VjdXJlZCB3aXRoIGFuIFNTTCBjZXJ0aWZpY2F0ZS48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+WW91IGNhbiBlaXRoZXIgPGI+dXBsb2FkIHRoZSBTU0wgZGlyZWN0bHkgdGhyb3VnaCB0aGUgZ3JhcGhpYyBpbnRlcmZhY2UgdG8gQVdTIGNlcnRpZmljYXRlIG1hbmFnZXIgKEFDTSkgKDEpPC9iPiBvciBkbyBpdCA8Yj50aHJvdWdoIHRoZSBjb21tYW5kIGxpbmUgaW4gdGhlIEFXUyBJZGVudGl0eSAmYW1wOyBBY2Nlc3MgTWFuYWdlbWVudCAoSUFNKSAoMik8L2I+LjxiciAvPjxiciAvPjwvZGl2Pjx1bD48bGk+VGhlIGZpcnN0IG9wdGlvbiBpcyBwcmV0dHkgc2ltcGxlLiBEdXJpbmcgdGhlIExvYWQgYmFsYW5jZXIgY3JlYXRpb24geW91IGNhbiBpbXBvcnQgdGhlIG5ldyBjZXJ0aWZpY2F0ZSBpbiB0aGUgc2Vjb25kIHN0ZXAgb2YgdGhlIHNldHVwOjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hd3NfMy5wbmciIC8+PGJyIC8+PC9saT48L3VsPg0KU2ltcGx5IGNob29zZSB0byB1cGxvYWQgdGhlIGNlcnRpZmljYXRlIHRvIEFDTSAodGhpcyBvcHRpb24gc2V0cyBhIGRlZmF1bHQgU1NMIGZvciBhbGwgdW5hc3NpZ25lZCBjYXNlcykgb3IgSUFNICh0aGlzIG9uZSBhbGxvd3MgeW91IHRvIGFkZCBtdWx0aXBsZSBTU0xzKSBhbmQgcGFzdGUgYWxsIDMgU1NMIGNvbXBvbmVudHMgYXMgY29kZXM6PGJyIC8+PGJyIC8+PG9sPjxsaT5UaGUgPGI+Q2VydGlmaWNhdGU8L2I+IGluIHRoZSAiQ2VydGlmaWNhdGUgYm9keSIgZm9ybTs8L2xpPjxsaT48Yj5DQS1idW5kbGU8L2I+IGluIHRoZSAiQ2VydGlmaWNhdGUgY2hhaW4iIGZvcm07PC9saT48bGk+QW5kIHRoZSA8Yj5Qcml2YXRlIGtleTwvYj4gaW4gdGhlICJQcml2YXRlIGtleSIgZm9ybS48L2xpPjwvb2w+PGRpdj5DaG9vc2UgdGhlIHNlY3VyaXR5IHBvbGljeSBmcm9tIHRoZSBkcm9wLWRvd24gbGlzdCAodGhlIGRlZmF1bHQgb25lIHdpbGwgd29yayBqdXN0IGZpbmUpIGFuZCBwcm9jZWVkIHdpdGggdGhlIGxvYWQgYmFsYW5jZXIgc2V0dXAuIDxiciAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5UaGUgU1NMIGNhbiBiZSBhbHNvIGFkZGVkIGxhdGVyIGJ5IGdvaW5nIHRvIHRoZSA8Yj5Mb2FkIEJhbGFuY2VyczwvYj4gbWVudSAmZ3Q7Jmd0OyA8Yj5MaXN0ZW5lcnM8L2I+ICZndDsmZ3Q7IDxiPlZpZXcvZWRpdCBjZXJ0aWZpY2F0ZXM8L2I+LjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXdzXzQucG5nIiAvPjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5DbGljayBvbiB0aGUgKyAocGx1cykgYnV0dG9uIHRvIGFkZCBhIG5ldyBjZXJ0aWZpY2F0ZSBhbmQgb3BlbiB0aGUgPGI+SW1wb3J0IGNlcnRpZmljYXRlPC9iPiBwYW5lbC48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+VGhlIGZvcm0gZm9yIFNTTCB1cGxvYWQgd2lsbCBzaG93OjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXdzXzUucG5nIiAvPjwvZGl2Pjx1bD48bGk+Rm9yIHRoZSA8Yj5zZWNvbmQgb3B0aW9uPC9iPiwgdXBsb2FkIHRoZSBjZXJ0aWZpY2F0ZSwgUHJpdmF0ZSBrZXkgYW5kIENBIEJ1bmRsZSB0byB5b3VyIHNlcnZlciBhbmQgb3BlbiB0aGUgY29tbWFuZCBsaW5lLiBBbGwgdGhyZWUgZmlsZXMgY2FuIGJlIGluc3RhbGxlZCB1c2luZyBhIHNpbmdsZSBjb21tYW5kOjwvbGk+PC91bD48ZGl2Pjxjb2RlPjxiPmF3cyBpYW0gdXBsb2FkLXNlcnZlci1jZXJ0aWZpY2F0ZSAtLXNlcnZlci1jZXJ0aWZpY2F0ZS1uYW1lIGNlcnRpZmljYXRlX29iamVjdF9uYW1lIC0tY2VydGlmaWNhdGUtYm9keSBmaWxlOi8vKnBhdGggdG8geW91ciBjZXJ0aWZpY2F0ZSBmaWxlKiAtLXByaXZhdGUta2V5IGZpbGU6Ly8qcGF0aCB0byB5b3VyIHByaXZhdGUga2V5IGZpbGUqIC0tY2VydGlmaWNhdGUtY2hhaW4gZmlsZTovLypwYXRoIHRvIHlvdXIgQ0EtYnVuZGxlIGZpbGUqPC9iPjwvY29kZT48L2Rpdj48YnIgLz48ZGl2PjxpPjxiPk5vdGU6PC9iPiBXaGVuIHlvdSBzcGVjaWZ5IGEgZmlsZSBhcyBhIHBhcmFtZXRlciAoZm9yIGV4YW1wbGUsIGZvciB0aGUgPGNvZGU+Y2VydGlmaWNhdGUtYm9keTwvY29kZT4gYW5kIDxjb2RlPnByaXZhdGUta2V5PC9jb2RlPiBwYXJhbWV0ZXJzKSwgZmlsZTovLyBzaG91bGQgYmUgaW5jbHVkZWQgYXMgYSBwYXJ0IG9mIHRoZSBmaWxlIG5hbWUuPC9pPjwvZGl2PjxkaXY+PGk+PGJyIC8+PC9pPjwvZGl2PjxkaXY+PGk+PGI+Tm90ZTo8L2I+IFRoZSA8Y29kZT5jZXJ0aWZpY2F0ZV9vYmplY3RfbmFtZTwvY29kZT4gcGFyYW1ldGVyIGlzIHVzZWQgdG8gYXNzaWduIHlvdXIgb3duIG5hbWUgdG8gdGhlIGNlcnRpZmljYXRlIHNvIHRoYXQgeW91IGNhbiBpZGVudGlmeSBpdCBmdXJ0aGVyLjwvaT48L2Rpdj48ZGl2PjxpPjxiciAvPjwvaT48L2Rpdj48ZGl2PldoZW4geW91IHVwbG9hZCB5b3VyIGNlcnRpZmljYXRlIGZpbGVzLCBJQU0gd2lsbCB2YWxpZGF0ZSB0aGUgZmlsZXMgaWYgdGhlIGZvbGxvd2luZyBjcml0ZXJpYSBhcmUgbWV0OjwvZGl2PjxvbD48bGk+Q2VydGlmaWNhdGVzIHNob3VsZCBiZSBpbiBYLjUwOSBQRU0gZm9ybWF0LjwvbGk+PGxpPlRoZSBjdXJyZW50IGRhdGUgc2hvdWxkIGJlIGJldHdlZW4gdGhlIGNlcnRpZmljYXRl4oCZcyBpc3N1YW5jZSBhbmQgZXhwaXJhdGlvbiBkYXRlLjwvbGk+PGxpPlRoZSBjZXJ0aWZpY2F0ZSBhbmQgUHJpdmF0ZSBrZXkgZmlsZXMgc2hvdWxkIGNvbnRhaW4gb25seSBhIHNpbmdsZSBpdGVtLCBtZWFuaW5nIG9uZSBjZXJ0aWZpY2F0ZSBmaWxlIGFuZCBvbmUgY29ycmVzcG9uZGluZyBrZXkuPC9saT48bGk+VGhlIFByaXZhdGUga2V5IHNob3VsZCBtYXRjaCB0aGUgY2VydGlmaWNhdGUuPC9saT48bGk+VGhlIFByaXZhdGUga2V5IHNob3VsZCBiZSBpbiBQRU0gZm9ybWF0LCBqdXN0IGxpa2UgdGhlIGNlcnRpZmljYXRlIGlzLiBUaGUgY29ycmVjdCBmb3JtYXQgb2YgdGhlIHRleHQgd2l0aGluIHRoZSBrZXkgZmlsZSBzaG91bGQgYmVnaW4gd2l0aCAtLS0tLUJFR0lOIFJTQSBQUklWQVRFIEtFWS0tLS0tIGFuZCBlbmRzIHdpdGggLS0tLS1FTkQgUlNBIFBSSVZBVEUgS0VZLS0tLS0uPC9saT48bGk+VGhlIFByaXZhdGUga2V5IHNob3VsZCBub3QgYmUgZW5jcnlwdGVkIHdpdGggYSBwYXNzd29yZC48L2xpPjwvb2w+PGRpdj5PbmNlIHRoZSBmaWxlcyBhcmUgdXBsb2FkZWQsIHlvdSBjYW4gPGI+dmVyaWZ5IHRoZSBjZXJ0aWZpY2F0ZSBpbmZvcm1hdGlvbjwvYj4gaW4gdGhlIElBTSBzdG9yZSBieSB1c2luZyB0aGUgZm9sbG93aW5nIGNvbW1hbmQ6PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2Pjxjb2RlPjxiPmF3cyBpYW0gZ2V0LXNlcnZlci1jZXJ0aWZpY2F0ZSAtLXNlcnZlci1jZXJ0aWZpY2F0ZS1uYW1lIGNlcnRpZmljYXRlX29iamVjdF9uYW1lPC9iPjwvY29kZT48L2Rpdj48ZGl2Pjxjb2RlPjxiPjxiciAvPjwvYj48L2NvZGU+PC9kaXY+PGRpdj5UaGUgb3V0cHV0IHNob3VsZCBsb29rIGxpa2UgdGhpczo8L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+PGNvZGU+YXJuOmF3czppYW06OllvdXJfQVdTX0FjY291bnRfSUQ6c2VydmVyLWNlcnRpZmljYXRlL1lvdXJfQ2VydGlmaWNhdGVfT2JqZWN0X05hbWUgQ2VydGlmaWNhdGVfT2JqZWN0X0dVSUQ8L2NvZGU+PGRpdj48Y29kZT5Zb3VyX0FXU19BY2NvdW50X0lEPC9jb2RlPiBpcyBhIHVuaXF1ZSBBbWF6b24gUmVzb3VyY2UgTmFtZSAoQVJOKSBhbmQgPGNvZGU+Q2VydGlmaWNhdGVfT2JqZWN0X0dVSUQ8L2NvZGU+IGlzIHRoZSBJRCBvZiB0aGUgY2VydGlmaWNhdGUuPC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PkhlcmXigJlzIGFuIGV4YW1wbGU6PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2Pjxjb2RlPmFybjphd3M6aWFtOjoxMjM0NTY3ODkwMTI6c2VydmVyLWNlcnRpZmljYXRlL2NlcnRpZmljYXRlX29iamVjdF9uYW1lIEFER1RIZXhhbXBsZUxLQkFTQUg8L2NvZGU+PC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PkRpZ2l0cyBpbiB0aGUgZmlyc3QgbGluZSBhcmUgdGhlIEFSTiwgYW5kIHRoZSBzZWNvbmQgbGluZSBpcyB0aGUgY2VydGlmaWNhdGUgSUQuPGJyIC8+PGJyIC8+PC9kaXY+PHVsPjxsaT5JZiB5b3UgbmVlZCB0byA8Yj51cGRhdGU8L2I+IHRoZSBjZXJ0aWZpY2F0ZSBmb3IgYSA8Yj5IVFRQUyBsb2FkIGJhbGFuY2VyPC9iPiwgeW91IHdpbGwgbmVlZCB0byB1c2UgdGhlIEFSTiBvZiB0aGUgY2VydGlmaWNhdGUuIFRoZSBmb2xsb3dpbmcgY29tbWFuZCBpcyB1c2VkIGluIHN1Y2ggYSBjYXNlIHRvIHNldCB0aGUgY2VydGlmaWNhdGUgZm9yIHRoZSBsb2FkIGJhbGFuY2VyOjwvbGk+PC91bD48ZGl2Pjxjb2RlPjxiPmF3cyBlbGIgc2V0LWxvYWQtYmFsYW5jZXItbGlzdGVuZXItc3NsLWNlcnRpZmljYXRlIC0tbG9hZC1iYWxhbmNlci1uYW1lIG15LWxvYWRiYWxhbmNlciAtLWxvYWQtYmFsYW5jZXItcG9ydCA0NDMgLS1zc2wtY2VydGlmaWNhdGUtaWQgYXJuOmF3czppYW06OjEyMzQ1Njc4OTAxMjpzZXJ2ZXItY2VydGlmaWNhdGUvY2VydGlmaWNhdGVfb2JqZWN0X25hbWU8L2I+PC9jb2RlPjwvZGl2PjxiciAvPjxkaXY+UGFyYW1ldGVyIDxjb2RlPm15LWxvYWRiYWxhbmNlcjwvY29kZT4gaXMgdGhlIG5hbWUgb2YgeW91ciBsb2FkIGJhbGFuY2VyLjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5Gb3IgbW9yZSBkZXRhaWxzIGFib3V0IGNyZWF0aW5nIGEgSFRUUFMgbG9hZCBiYWxhbmNlciBhbmQgc2V0dGluZyBpdHMgbmFtZSwgcGxlYXNlIGNoZWNrIHRoZSA8YSBocmVmPSJodHRwczovL2RvY3MuYXdzLmFtYXpvbi5jb20vZWxhc3RpY2xvYWRiYWxhbmNpbmcvbGF0ZXN0L2NsYXNzaWMvZWxiLWNyZWF0ZS1odHRwcy1zc2wtbG9hZC1iYWxhbmNlci5odG1sI2NvbmZpZ3VyZS1odHRwcy1saXN0ZW5lciIgbGlua3RleHQ9ImZvbGxvd2luZyBndWlkZSIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPmZvbGxvd2luZyBndWlkZTwvYT4uPC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxoMiBpZD0iNCI+QVdTIEFQSSBHYXRld2F5PC9oMj48ZGl2PkJ5IGRlZmF1bHQsIEFtYXpvbiBBUEkgdXNlcyBhIDxiPmRlZmF1bHQgYWNjZXNzIGxpbms8L2I+IHRoYXQgbG9va3MgbGlrZSB0aGlzOjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj48Y29kZT5odHRwczovL2FwaS1pZC5leGVjdXRlLWFwaS5yZWdpb24uYW1hem9uYXdzLmNvbS9zdGFnZTwvY29kZT48L2Rpdj48YnIgLz48ZGl2PkluIHNvbWUgY2FzZXMsIGl04oCZcyBtb3JlIGNvbnZlbmllbnQgdG8gc2V0IHVwIGEgY3VzdG9tIGhvc3RuYW1lIGZvciBpdCBpbnN0ZWFkLiBUaGUgY3VzdG9tIGxpbmsgY2FuIGJlIGFsc28gc2VjdXJlZCB3aXRoIGFuIFNTTCBjZXJ0aWZpY2F0ZS48L2Rpdj48ZGl2PjxiciAvPjwvZGl2PjxkaXY+VGhlIHByb2Nlc3MgaXMgc2ltaWxhciB0byB0aGUgbG9hZCBiYWxhbmNlciBzZWN1cmluZy48L2Rpdj48b2w+PGxpPkxvZyBpbiB0byB0aGUgQVdTIENlcnRpZmljYXRlIE1hbmFnZXIgY29uc29sZS48L2xpPjxsaT5DaG9vc2UgdGhlIEltcG9ydCBhIGNlcnRpZmljYXRlIG9wdGlvbi48L2xpPjxsaT5BIHNpbWlsYXIgZm9ybSBmb3IgdGhlIFNTTCB1cGxvYWQgd2lsbCBvcGVuLjxiciAvPjxiciAvPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hd3NfNi5wbmciIC8+PGJyIC8+PC9saT48bGk+UGFzdGUgdGhlIGNlcnRpZmljYXRlIGZpbGUgY29kZSBhcyB0aGUgIkNlcnRpZmljYXRlIGJvZHkiLCBDQS1idW5kbGUgY29kZSBhcyB0aGUgIkNlcnRpZmljYXRlIGNoYWluIiBhbmQgUHJpdmF0ZSBrZXkgY29kZSBhcyB0aGUgIkNlcnRpZmljYXRlIHByaXZhdGUga2V5IiBhbmQgY2xpY2sgPGI+TmV4dDwvYj4uPC9saT48bGk+U2F2ZSB0aGUgY2hhbmdlcyBieSBzZWxlY3RpbmcgdGhlIDxiPlJldmlldyBhbmQgaW1wb3J0PC9iPiBvcHRpb24uPC9saT48bGk+Q2hvb3NlIHRoZSA8Yj5DdXN0b20gZG9tYWluIG5hbWVzPC9iPiBvcHRpb24gZnJvbSB0aGUgPGI+QVBJIEdhdGV3YXk8L2I+IG1lbnUuPC9saT48bGk+Q2hvb3NlIHlvdXIgY3VzdG9tIGRvbWFpbiBuYW1lLjwvbGk+PGxpPkNsaWNrIDxiPkVkaXQ8L2I+LjwvbGk+PGxpPkNob29zZSB0aGUgY29ycmVjdCBTU0wgZnJvbSB0aGUgZHJvcC1kb3duIGxpc3QgYW5kIHNhdmUgdGhlIGNoYW5nZXMuPGJyIC8+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2F3c183LnBuZyIgLz48YnIgLz48L2xpPjwvb2w+PGRpdj5LZWVwIGluIG1pbmQhIFRoZSBjZXJ0aWZpY2F0ZSBtYXkgdGFrZSB1cCB0byA0MCBtaW51dGVzIHRvIGFwcGx5LjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5BbHRlcm5hdGl2ZWx5LCB5b3UgY2FuIGFsc28gaW5zdGFsbCBhbiBTU0wgdGhyb3VnaCB0aGUgPGNvZGU+ZG9tYWlubmFtZTp1cGRhdGU8L2NvZGU+IEFQSS1jYWxsIHZpYSB0aGUgY29tbWFuZCBsaW5lLjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5UaGUgcmVxdWVzdCBpdHNlbGYgd2lsbCBsb29rIGxpa2UgdGhpczo8L2Rpdj48YnIgLz48Y29kZT5QQVRDSCAvZG9tYWlubmFtZXMvKllvdXIgQVBJIGRvbWFpbiBuYW1lKg0KPGJyIC8+PGJyIC8+PC9jb2RlPjxkaXY+PGNvZGU+DQp7PC9jb2RlPjwvZGl2PjxkaXY+PGNvZGU+wqAgInBhdGNoT3BlcmF0aW9ucyIgOiBbIHs8L2NvZGU+PC9kaXY+PGRpdj48Y29kZT7CoCAib3AiIDogcmVwbGFjZSw8YnIgLz48L2NvZGU+PC9kaXY+PGRpdj48Y29kZT7CoCAicGF0aCIgOiAqcGFyYW1ldGVyIHVzZWQgdG8gaWRlbnRpZnkgdGhlIFNTTCosPGJyIC8+PC9jb2RlPjwvZGl2PjxkaXY+PGNvZGU+wqAgInZhbHVlIiA6ICpwYXJhbWV0ZXIgdmFsdWUqLDxiciAvPjwvY29kZT48L2Rpdj48ZGl2Pjxjb2RlPsKgICJmcm9tIiA6IC8vIG9wdGlvbmFsIHBhcmFtZXRlciB3aGVyZSB5b3UgY2FuIHNwZWNpZnkgd2hhdCBzcGVjaWZpYyBwYXJ0IG9mIHRoZSBhcHBsaWNhdGlvbiBzaG91bGQgdXNlIHRoZSBTU0wuPC9jb2RlPjwvZGl2PjxkaXY+PGNvZGU+wqAgfSBdPC9jb2RlPjwvZGl2PjxkaXY+PGNvZGU+fTwvY29kZT48L2Rpdj48YnIgLz48ZGl2Pk1vcmUgZGV0YWlscyBhYm91dCB0aGUgY29tbWFuZCBjYW4gYmUgZm91bmQgPGEgaHJlZj0iaHR0cHM6Ly9kb2NzLmF3cy5hbWF6b24uY29tL2FwaWdhdGV3YXkvYXBpLXJlZmVyZW5jZS9saW5rLXJlbGF0aW9uL2RvbWFpbm5hbWUtdXBkYXRlLyIgbGlua3RleHQ9ImhlcmUiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj5oZXJlPC9hPi48L2Rpdj48ZGl2PjxiciAvPjxiciAvPjwvZGl2PjxoMiBpZD0iNSI+QW1hem9uIENsb3VkRnJvbnQ8L2gyPjxkaXY+QW1hem9uIENsb3VkRnJvbnQgaXMgYSB3ZWIgc2VydmljZSB0aGF0IGFsbG93cyB5b3UgdG8gc3BlZWQgdXAgY29udGVudCBkaXN0cmlidXRpb24gaW4gZGlmZmVyZW50IGxvY2F0aW9ucyBieSBjYWNoaW5nIHNvbWUgb2YgaXQgaW4gYSBzcGVjaWFsIHN0b3JhZ2UuPC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PllvdSBjYW4gZWl0aGVyIHVwbG9hZCBhbiBTU0wgY2VydGlmaWNhdGUgdGhyb3VnaCBTU0wgbWFuYWdlciBvciB0aHJvdWdoIHRoZSBjb21tYW5kIGxpbmUsIGFzIGRlc2NyaWJlZCA8YSBocmVmPSIjNCI+YWJvdmU8L2E+LjwvZGl2PjxkaXY+PGJyIC8+PC9kaXY+PGRpdj5BZnRlciBhZGRpbmcgdGhlIFNTTCwgQ2xvdWRGcm9udCBzZXR0aW5ncyBuZWVkIHRvIGJlIHVwZGF0ZWQgYXMgZm9sbG93czo8YnIgLz48YnIgLz48L2Rpdj48b2w+PGxpPk9wZW4geW91ciBBV1MgY29uc29sZSBhbmQgZ28gdG8gdGhlIDxhIGhyZWY9Imh0dHBzOi8vY29uc29sZS5hd3MuYW1hem9uLmNvbS9jbG91ZGZyb250LyIgbGlua3RleHQ9IkNsb3VkRnJvbnQgY29uc29sZSIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPkNsb3VkRnJvbnQgY29uc29sZTwvYT4uPC9saT48bGk+Q2hvb3NlIHRoZSBJRCBvZiB0aGUgQ2xvdWRGcm9udCBlbnRpdHkgdGhhdCBuZWVkcyB0byBiZSB1cGRhdGVkLjwvbGk+PGxpPkdvIHRvIHRoZSA8Yj5HZW5lcmFsPC9iPiB0YWIgYW5kIGNob29zZSA8Yj5FZGl0PC9iPi48YnIgLz48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXdzXzgucG5nIiAvPjxiciAvPjwvbGk+PGxpPlVwZGF0ZSA8Yj5BbHRlcm5hdGUgRG9tYWluIE5hbWVzIChDTkFNRXMpPC9iPiB3aXRoIHlvdXIgU1NMIGRvbWFpbiBuYW1lKHMpIGFuZCBjaG9vc2UgdGhlIGNvcnJlY3QgU1NMIGZyb20gdGhlIGxpc3QuPGJyIC8+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2F3c185LnBuZyIgLz48YnIgLz48L2xpPjxsaT5DbGljayA8Yj5ZZXMsIEVkaXQ8L2I+LjwvbGk+PGxpPkFmdGVyIHRoaXMsIHlvdSBjYW4gZ28gdG8gdGhlIDxiPkJlaGF2aW9yczwvYj4gdGFiIGFuZCBlaXRoZXIgc2V0IGEgcmVkaXJlY3QgZnJvbSBIVFRQIHRvIEhUVFBTIG9yIHNldCB0aGUgQ2xvdWRmcm9udCB0byBIVFRQUyBvbmx5LjxiciAvPjxiciAvPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hd3NfMTAucG5nIiAvPjxiciAvPjwvbGk+PC9vbD48ZGl2PlRoZSBTU0wgY2FuIGJlIHNldCB1cCBkdXJpbmcgdGhlIENsb3VkRnJvbnQgZW50aXR5IGNyZWF0aW9uIGFsc28uPC9kaXY+PGRpdj48YnIgLz48L2Rpdj48ZGl2PjxpPjxiPk5vdGU8L2I+OiBJZiB5b3Ugd2FudCB0byB1c2UgYW4gQUNNIGNlcnRpZmljYXRlIHdpdGggQW1hem9uIENsb3VkRnJvbnQsIG1ha2Ugc3VyZSB5b3UgaW1wb3J0IGEgY2VydGlmaWNhdGUgc3RvcmVkIGluIHRoZSBVUyBFYXN0IChOLiBWaXJnaW5pYSkgcmVnaW9uLiBPdGhlcndpc2UsIHVzZSB0aGUgY2VydGlmaWNhdGUgaW1wb3J0ZWQgdG8gSUFNLjwvaT48L2Rpdj48ZGl2PjxpPjxiciAvPjwvaT48L2Rpdj48ZGl2PllvdSBjYW4gdmVyaWZ5IHRoYXQgYSBjZXJ0aWZpY2F0ZSBoYXMgYmVlbiBpbnN0YWxsZWQgY29ycmVjdGx5IGJ5IGNoZWNraW5nIGRpcmVjdGx5IG9yIHVzaW5nIGFuIG9ubGluZSBjaGVja2VyLCBzdWNoIGFzIDxhIGhyZWY9Imh0dHBzOi8vZGVjb2Rlci5saW5rLyIgbGlua3RleHQ9InRoaXMgb25lIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+dGhpcyBvbmU8L2E+LjwvZGl2PjwvZGl2Pg==","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2020-09-02T12:10:40.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2015-08-13T15:44:38.0000000","ApprovalDatetime":"2015-08-13T15:44:42.0000000","RequestCount":104630,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":2,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":33,"CategoryName":"SSL Installation"}],"AssociatedCategories":[{"CategoryId":33,"CategoryName":"SSL Installation","CategoryDisplayName":"HostingSSL Installation"}],"AssociatedTags":[],"RelatedArticles":[{"ArticleId":9592,"PreferedCategoryId":2290,"ArticleTypeId":0,"ArticleName":"Generating a CSR on Amazon Web Services (AWS)","ArticleTypeName":null,"Title":"Generating a CSR on Amazon Web Services (AWS)","LiveDateTime":null,"ModifiedDateTime":"09/13/2022","MarkedAsNew":false,"MarkedAsFeatured":false}],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":33}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","ParentCategoryId":12,"Parent_Category_Name":"Hosting","FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":false,"CreatedDateTime":"07/21/2008 16:07:56","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":33,"CategoryName":"SSL Installation"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":9593,"Title":"Installing an SSL certificate on Amazon Web Services (AWS)","ArticleName":"Installing an SSL certificate on Amazon Web Services (AWS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/02/2020"},{"ArticleId":9595,"Title":"HTTP to HTTPS redirection on IIS","ArticleName":"HTTP to HTTPS redirection on IIS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/25/2019"},{"ArticleId":9635,"Title":"Installing an SSL certificate on Synology NAS","ArticleName":"Installing an SSL certificate on Synology NAS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9681,"Title":"Installing an SSL Certificate in Vesta CP","ArticleName":"Installing an SSL Certificate in Vesta CP","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9686,"Title":"Installing an SSL Certificate on Sun Java System Web Server 7.x","ArticleName":"Installing an SSL Certificate on Sun Java System Web Server 7.x","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9702,"Title":"Installing an SSL certificate on Webmin","ArticleName":"Installing an SSL certificate on Webmin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9705,"Title":"Installing an SSL certificate on Node.js","ArticleName":"Installing an SSL certificate on Node.js","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9746,"Title":"Installing an SSL certificate in Exchange 2013 EAC","ArticleName":"Installing an SSL certificate in Exchange 2013 EAC","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/28/2024"},{"ArticleId":9749,"Title":"Installing an SSL certificate in Exchange 2013 Shell","ArticleName":"Installing an SSL certificate in Exchange 2013 Shell","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9750,"Title":"How to export/import certificates on Exchange 2013 Shell","ArticleName":"How to export/import certificates on Exchange 2013 Shell","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/12/2020"},{"ArticleId":9754,"Title":"Installing an SSL certificate on IIS 8&10","ArticleName":"Installing an SSL certificate on IIS 8&10","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9823,"Title":"Installing an SSL certificate on Microsoft Azure Web App","ArticleName":"Installing an SSL certificate on Microsoft Azure Web App","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/04/2024"},{"ArticleId":9825,"Title":"Installing an SSL certificate on a GlassFish application server","ArticleName":"Installing an SSL certificate on a GlassFish application server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/28/2019"},{"ArticleId":9842,"Title":"Installing an SSL certificate on Zimbra","ArticleName":"Installing an SSL certificate on Zimbra","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/12/2023"},{"ArticleId":9853,"Title":"Installing an SSL certificate on Google App Engine","ArticleName":"Installing an SSL certificate on Google App Engine","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9865,"Title":"Installing an SSL certificate on Exchange 2010","ArticleName":"Installing an SSL certificate on Exchange 2010","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9899,"Title":"Installing an SSL certificate on Mac OS X/Yosemite/El Capitan","ArticleName":"Installing an SSL certificate on Mac OS X/Yosemite/El Capitan","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9919,"Title":"Installing an SSL certificate on SonicWall","ArticleName":"Installing an SSL certificate on SonicWall","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9956,"Title":"Installing an SSL certificate on Plesk Onyx","ArticleName":"Installing an SSL certificate on Plesk Onyx","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9958,"Title":"Installing an SSL certificate on Citrix NetScaler VPX","ArticleName":"Installing an SSL certificate on Citrix NetScaler VPX","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/29/2019"},{"ArticleId":9970,"Title":"IIS: multiple certificates installation","ArticleName":"IIS: multiple certificates installation","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/29/2019"},{"ArticleId":10026,"Title":"Installing an SSL certificate on XAMPP","ArticleName":"Installing an SSL certificate on XAMPP","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"08/04/2025"},{"ArticleId":10050,"Title":"Installing an SSL certificate on Heroku SSL","ArticleName":"Installing an SSL certificate on Heroku SSL","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/25/2025"},{"ArticleId":10052,"Title":"Installing an SSL certificate in CWP 7","ArticleName":"Installing an SSL certificate in CWP 7","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10063,"Title":"Installing an SSL certificate on Windows using Certeq","ArticleName":"Installing an SSL certificate on Windows using Certeq","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/02/2019"},{"ArticleId":10134,"Title":"Installing an SSL certificate on Ubiquiti Unifi","ArticleName":"Installing an SSL certificate on Ubiquiti Unifi","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10154,"Title":"Installing an SSL certificate on ISPConfig","ArticleName":"Installing an SSL certificate on ISPConfig","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10175,"Title":"Can I install an SSL Certificate on a Parked Domain in cPanel?","ArticleName":"Can I install an SSL Certificate on a Parked Domain in cPanel?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/27/2026"},{"ArticleId":10252,"Title":"How to set up an SSL certificate in SiteWorx account","ArticleName":"How to set up an SSL certificate in SiteWorx account","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/20/2020"},{"ArticleId":10313,"Title":"SSL Certificate installation on httpd (CentOS)","ArticleName":"SSL Certificate installation on httpd (CentOS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/23/2022"},{"ArticleId":10314,"Title":"SSL Certificate installation on apache2 (Debian, Ubuntu)","ArticleName":"SSL Certificate installation on apache2 (Debian, Ubuntu)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/23/2022"},{"ArticleId":10332,"Title":"Importing/Exporting certificates on Mac OS via Keychain","ArticleName":"Importing/Exporting certificates on Mac OS via Keychain","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/06/2022"},{"ArticleId":633,"Title":"IIS","ArticleName":"IIS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/22/2020"},{"ArticleId":9418,"Title":"Installing an SSL certificate on your server, using cPanel","ArticleName":"Installing an SSL certificate on your server, using cPanel","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/02/2025"},{"ArticleId":9419,"Title":"Installing an SSL certificate on Nginx","ArticleName":"Installing an SSL certificate on Nginx","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9423,"Title":"Installing an SSL certificate on Apache","ArticleName":"Installing an SSL certificate on Apache","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9424,"Title":"Installing an SSL Certificate on IIS 7","ArticleName":"Installing an SSL Certificate on IIS 7","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/29/2024"},{"ArticleId":9425,"Title":"Installing an SSL Certificate using DirectAdmin","ArticleName":"Installing an SSL Certificate using DirectAdmin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9439,"Title":"Installing an SSL Certificate using WHM","ArticleName":"Installing an SSL Certificate using WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9441,"Title":"Installing an SSL certificate on Tomcat","ArticleName":"Installing an SSL certificate on Tomcat","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9443,"Title":"Installing an SSL Certificate on Exchange 2007 (PowerShell)","ArticleName":"Installing an SSL Certificate on Exchange 2007 (PowerShell)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9448,"Title":"Installing an SSL certificate in Plesk 12","ArticleName":"Installing an SSL certificate in Plesk 12","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":786,"Title":"What is an SSL certificate and what is it used for?","ArticleName":"What is an SSL certificate and what is it used for?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/24/2023"},{"ArticleId":9260,"Title":"Why is it beneficial to have a dedicated IP address?","ArticleName":"Why is it beneficial to have a dedicated IP address?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/03/2021"},{"ArticleId":9259,"Title":"SNI technology","ArticleName":"SNI technology","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/06/2018"},{"ArticleId":214,"Title":"Can I install SSL certificates for a couple of domains at once on Namecheap hosting servers?","ArticleName":"Can I install SSL certificates for a couple of domains at once on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/21/2024"},{"ArticleId":215,"Title":"How many SSL certificates can I install under my Namecheap hosting account?","ArticleName":"How many SSL certificates can I install under my Namecheap hosting account?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/28/2020"},{"ArticleId":804,"Title":"SSL certificate activation and installation for domain(s) hosted on Namecheap hosting servers","ArticleName":"SSL certificate activation and installation for domain(s) hosted on Namecheap hosting servers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"},{"ArticleId":9393,"Title":"Where do I find SSL CA Bundle?","ArticleName":"Where do I find SSL CA Bundle?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/22/2025"},{"ArticleId":211,"Title":"How can I get a CSR code for a domain hosted on Namecheap hosting servers?","ArticleName":"How can I get a CSR code for a domain hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/19/2024"},{"ArticleId":213,"Title":"Do you allow SSL installation on a subdomain of a domain hosted on Namecheap hosting servers?","ArticleName":"Do you allow SSL installation on a subdomain of a domain hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/25/2021"},{"ArticleId":9464,"Title":"Can I download an issued certificate on your site?","ArticleName":"Can I download an issued certificate on your site?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/12/2024"},{"ArticleId":9465,"Title":"How do I export my certificate from Apache?","ArticleName":"How do I export my certificate from Apache?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/21/2024"},{"ArticleId":122,"Title":"Is there a shared SSL certificate for domains hosted on Namecheap hosting servers?","ArticleName":"Is there a shared SSL certificate for domains hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"}],"AssociatedTags":[],"CategoryId":33,"CategoryName":"SSL Installation"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}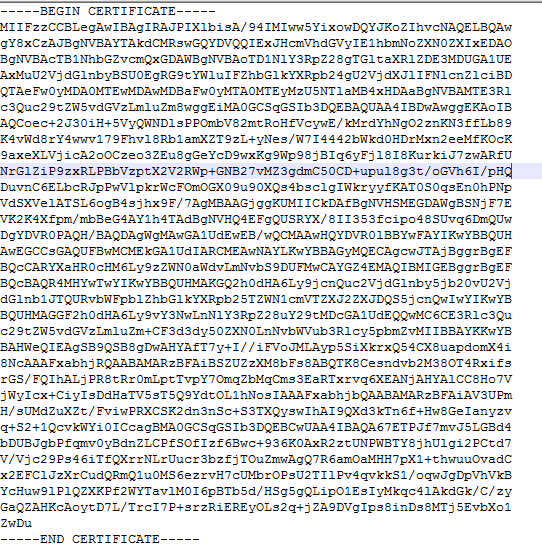
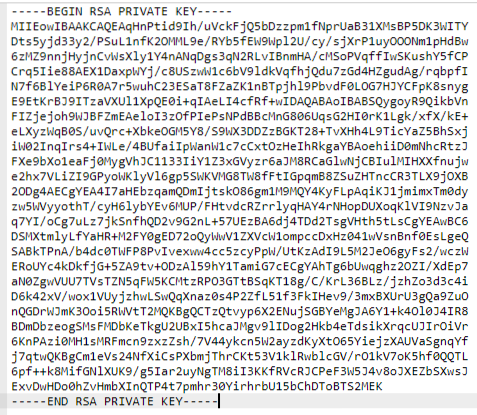
cat example.crtsudo yum install -y mod24_ssl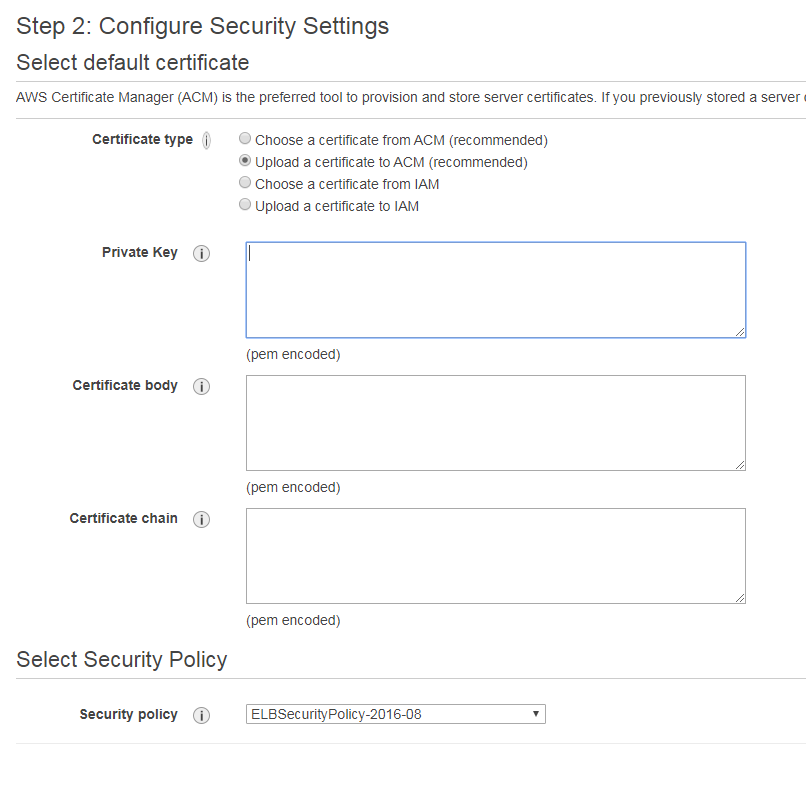
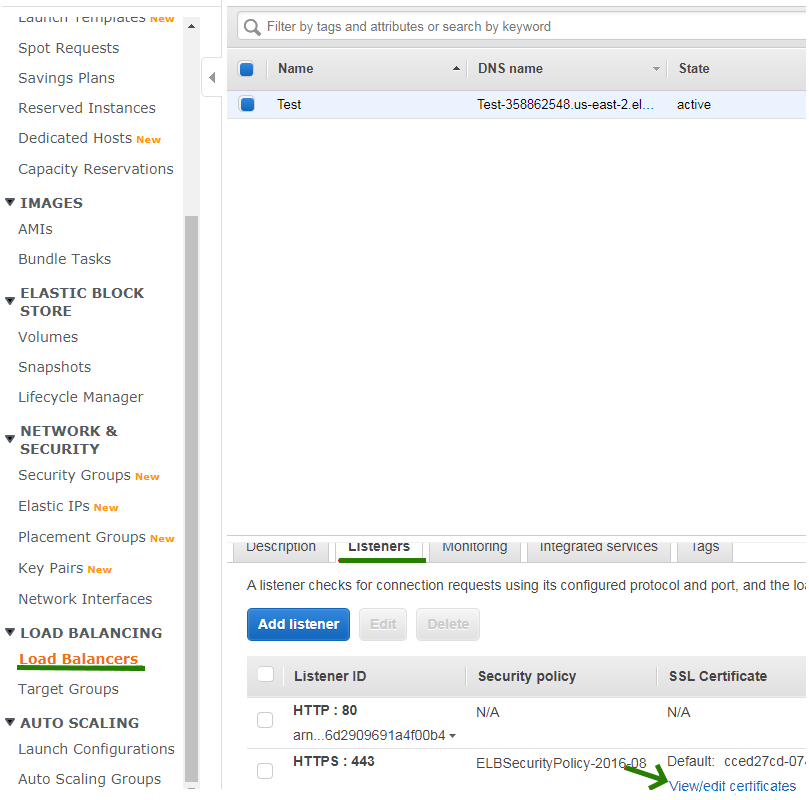
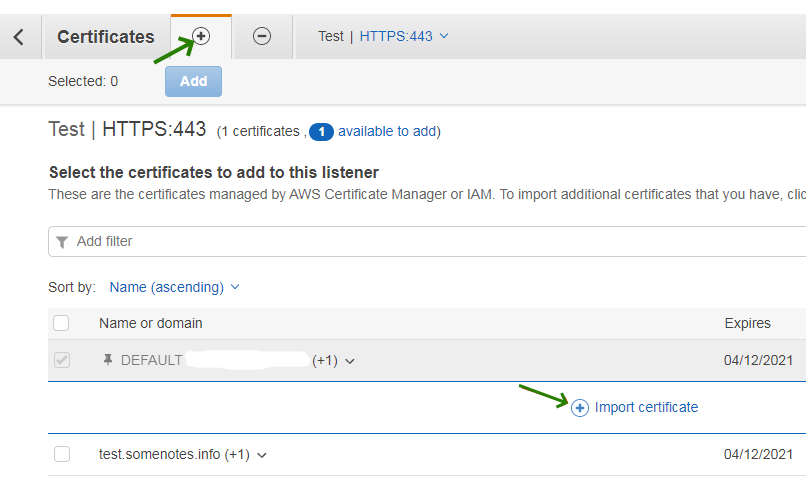
aws iam upload-server-certificate --server-certificate-name certificate_object_name --certificate-body file://*path to your certificate file* --private-key file://*path to your private key file* --certificate-chain file://*path to your CA-bundle file*certificate-body and private-key parameters), file:// should be included as a part of the file name.certificate_object_name parameter is used to assign your own name to the certificate so that you can identify it further.aws iam get-server-certificate --server-certificate-name certificate_object_name
arn:aws:iam::Your_AWS_Account_ID:server-certificate/Your_Certificate_Object_Name Certificate_Object_GUIDYour_AWS_Account_ID is a unique Amazon Resource Name (ARN) and Certificate_Object_GUID is the ID of the certificate.arn:aws:iam::123456789012:server-certificate/certificate_object_name ADGTHexampleLKBASAHaws elb set-load-balancer-listener-ssl-certificate --load-balancer-name my-loadbalancer --load-balancer-port 443 --ssl-certificate-id arn:aws:iam::123456789012:server-certificate/certificate_object_namemy-loadbalancer is the name of your load balancer.https://api-id.execute-api.region.amazonaws.com/stage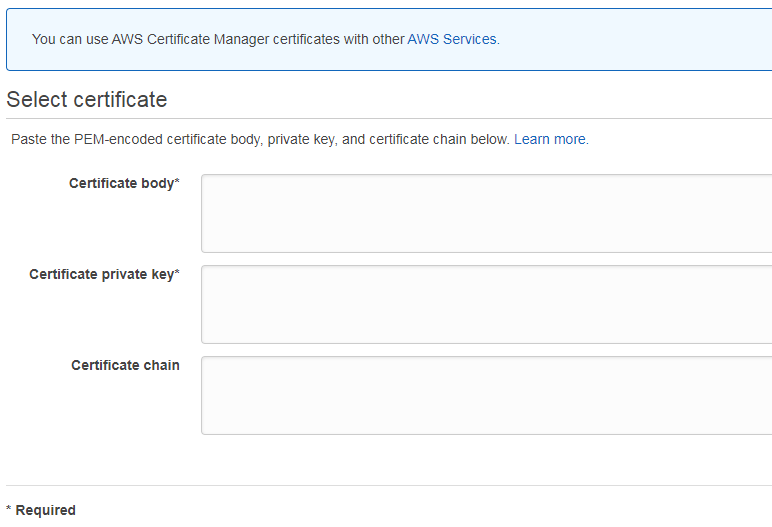
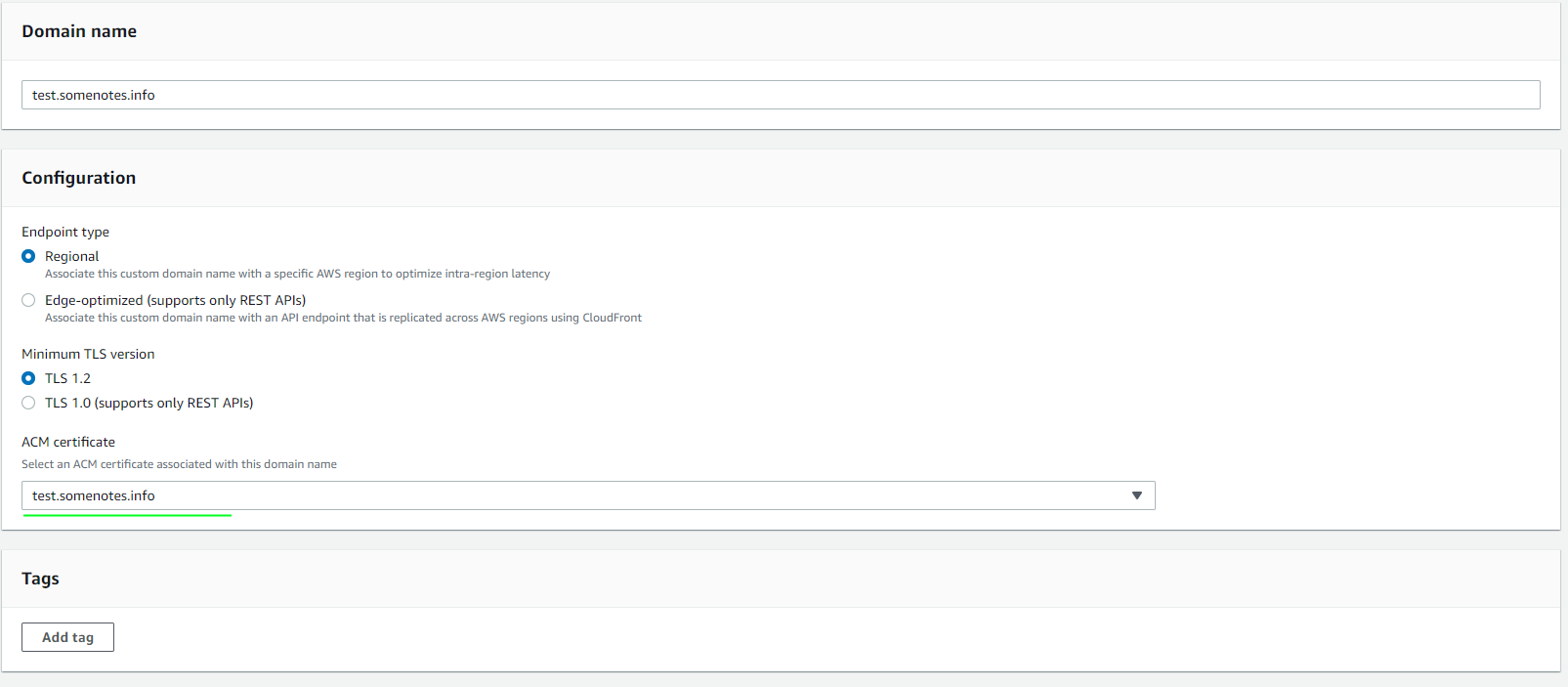
domainname:update API-call via the command line.PATCH /domainnames/*Your API domain name*
{ "patchOperations" : [ { "op" : replace,
"path" : *parameter used to identify the SSL*,
"value" : *parameter value*,
"from" : // optional parameter where you can specify what specific part of the application should use the SSL. } ]}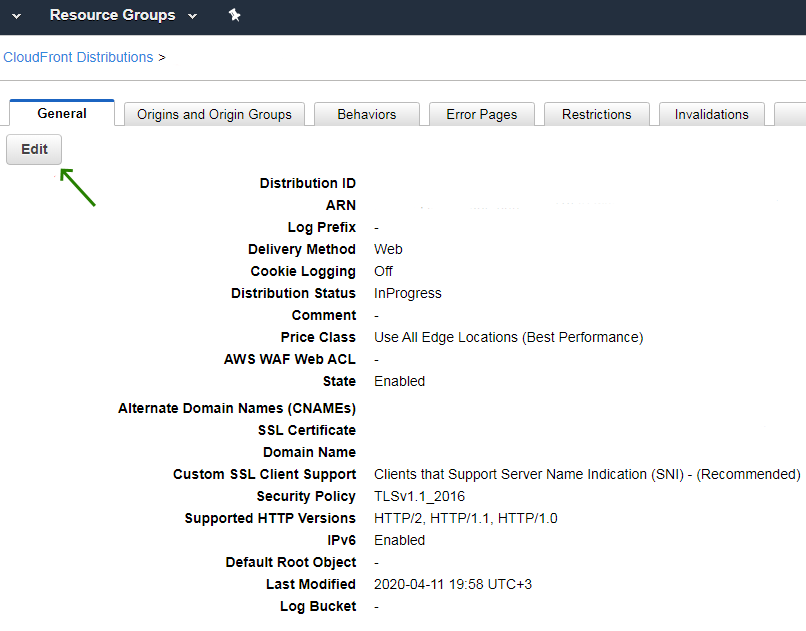
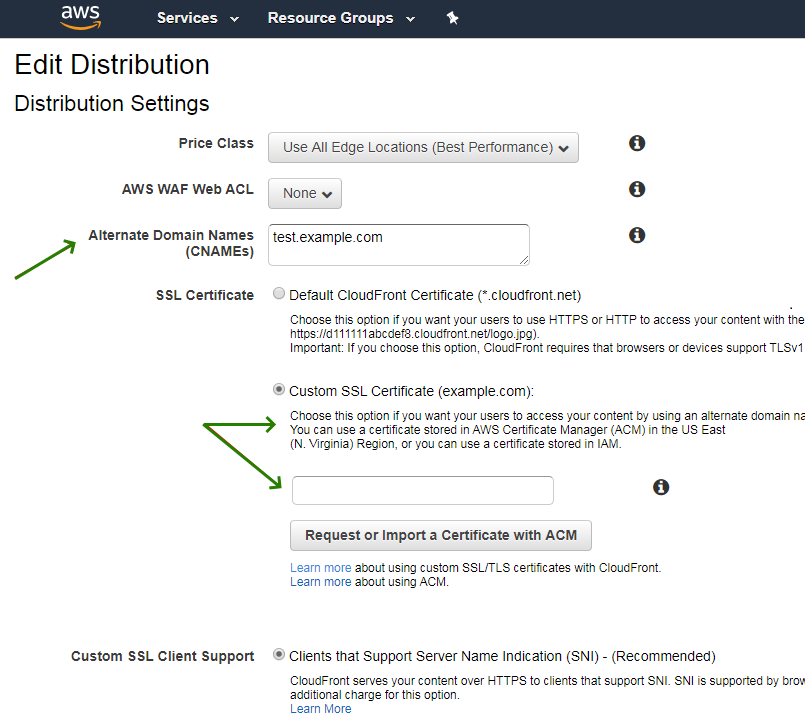
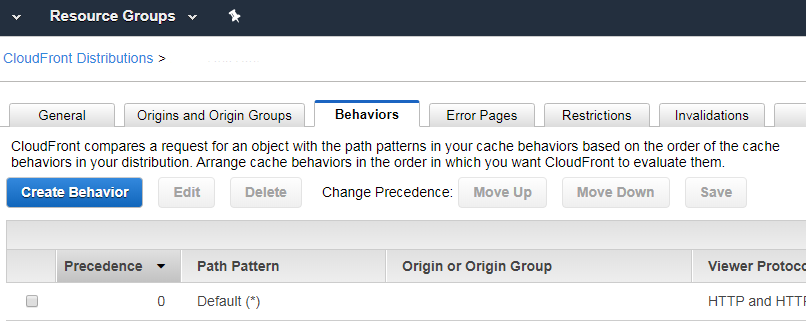
Need help? We're always here for you.