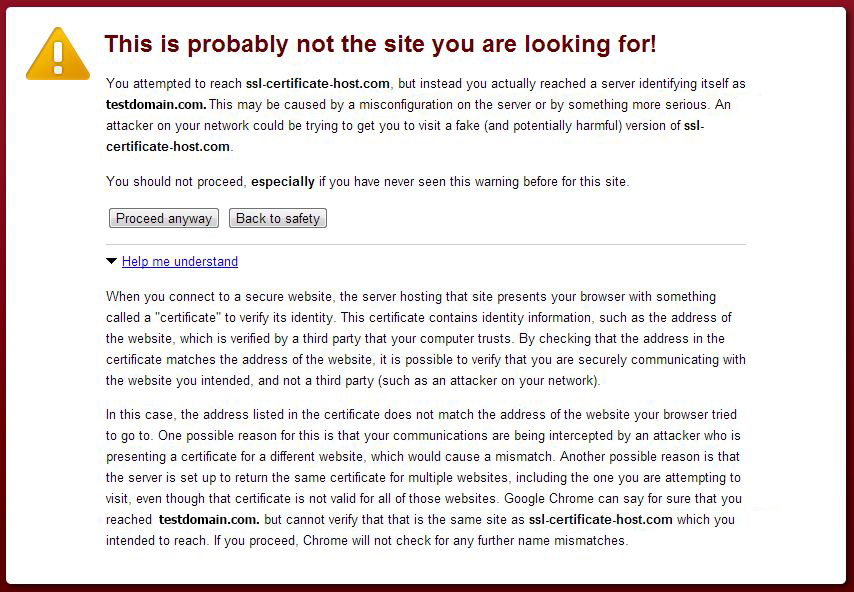
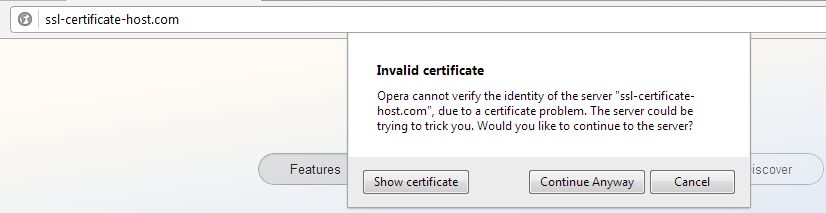
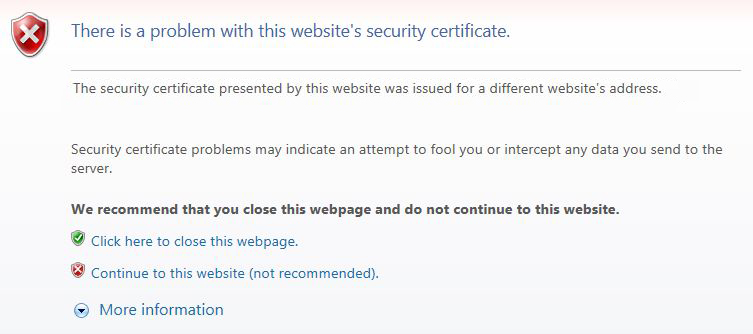
{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":9468,\\\"categoryId\\\":2223}\"":{"body":{"Id":9468,"FriendlyId":"","ArticleTypeId":0,"Title":"Why do I get \"Common name mismatch\" error in my browser?","ArticleName":"Why do I get \"Common name mismatch\" error in my browser?","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"DQoJCTxwPlRoZSBlcnJvciBtZXNzYWdlIGRpZmZlcnMgZGVwZW5kaW5nIG9uIGJyb3dzZXJzLiBUaGUgbW9zdCBwb3B1bGFyIG9uZXMgYXJlIGxpc3RlZCBiZWxvdzo8L3A+DQoJCTxwPg0KCQkJCTxiPkZpcmVmb3g6PC9iPg0KCQkJCTxiciAvPg0KCQk8L3A+DQoJCTxwPg0KCQkJCTxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9DZXJ0X21pc21hdGNoXzEuanBnIiBhbHQ9IkNlcnRfbWlzbWF0Y2hfMS5qcGciIHdpZHRoPSI1MDQiIGhlaWdodD0iMzAyIiBib3JkZXI9IjAiIC8+DQoJCTwvcD4NCgkJPGI+R29vZ2xlIENocm9tZTo8L2I+DQoJCTxwPg0KCQkJCTxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9DZXJ0X21pc21hdGNoXzIuanBnIiBhbHQ9IkNlcnRfbWlzbWF0Y2hfMi5qcGciIHdpZHRoPSI1MzAiIGhlaWdodD0iMzk0IiBib3JkZXI9IjAiIC8+DQoJCTwvcD4NCgkJPGI+T3BlcmE6PC9iPg0KCQk8cD4NCgkJCQk8aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF8zLmpwZyIgYWx0PSJDZXJ0X21pc21hdGNoXzMuanBnIiB3aWR0aD0iNTcyIiBoZWlnaHQ9IjE1OSIgYm9yZGVyPSIwIiAvPg0KCQk8L3A+DQoJCTxiPkludGVybmV0IEV4cGxvcmVyOjwvYj4NCgkJPHA+DQoJCQkJPGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL0NlcnRfbWlzbWF0Y2hfNC5qcGciIGFsdD0iQ2VydF9taXNtYXRjaF80LmpwZyIgd2lkdGg9IjQ5MCIgaGVpZ2h0PSIyMzAiIGJvcmRlcj0iMCIgLz4NCgkJPC9wPg0KCQk8Yj5TYWZhcmk6PC9iPg0KCQk8cD4NCgkJCQk8aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF81LmpwZyIgYWx0PSJDZXJ0X21pc21hdGNoXzUuanBnIiB3aWR0aD0iMzg5IiBoZWlnaHQ9IjE3MSIgYm9yZGVyPSIwIiAvPg0KCQk8L3A+DQoJCTxiPk5ldHNjYXBlIE5hdmlnYXRvcjo8L2I+DQoJCTxwPg0KCQkJCTxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9DZXJ0X21pc21hdGNoXzYuanBnIiBhbHQ9IkNlcnRfbWlzbWF0Y2hfNi5qcGciIHdpZHRoPSIzOTEiIGhlaWdodD0iMjUzIiBib3JkZXI9IjAiIC8+DQoJCTwvcD4NCgkJPGRpdj4NCkluIGZhY3QsIHRoZSBDb21tb24gTmFtZSBtaXNtYXRjaCBpcyBub3QgYW4gZXJyb3IsIGJ1dCBhIHdhcm5pbmcgdGhhdCBvY2N1cnMgb25jZSBhIGhvc3RuYW1lIHlvdSBhcmUgdHJ5aW5nIHRvIGFjY2VzcyBpbiB0aGUgYnJvd3NlciBkb2VzIG5vdCBtYXRjaCB0aGUgQ29tbW9uIE5hbWUgb2YgYSBjZXJ0aWZpY2F0ZSB0aGF0IGlzIHBpY2tlZCB1cCBmcm9tIHRoZSBzZXJ2ZXIgZHVyaW5nIHRoZSBlc3RhYmxpc2htZW50IG9mIGFuIGh0dHBzIHNlc3Npb24uIDxiciAvPjwvZGl2Pg0KCQk8ZGl2Pg0KCQkJCTxiciAvPg0KCQk8L2Rpdj4NCgkJPGRpdj5UaGlzIHdhcm5pbmcgY2FuIGFwcGVhciBkdWUgdG8gYSBudW1iZXIgb2YgPGI+cmVhc29uczwvYj47IHdlIGhhdmUgZGVzY3JpYmVkIHRoZSBtb3N0IHdpZGVzcHJlYWQgb2YgdGhlbSBiZWxvdzoNCjwvZGl2Pg0KCQk8b2w+DQoJCQkJPGxpPlRoZSBDZXJ0aWZpY2F0ZSBpcyBpbnN0YWxsZWQsIGJ1dCB0aGUgZG9tYWluIGlzIHBvaW50ZWQgdG8gYSBzaGFyZWQgSVAgYWRkcmVzc2VzLiANCjxwPlVzdWFsbHkgYSBkZWRpY2F0ZWQgSVAgaXMgcmVxdWlyZWQgaW4gb3JkZXIgdG8gaW5zdGFsbCB0aGUgU1NMIGNlcnRpZmljYXRlLiBJZiB0aGVyZSBpcyBhbHJlYWR5IGEgY2VydGlmaWNhdGUgaW5zdGFsbGVkIHdpdGhpbiB0aGUgc2FtZSBJUCBhZGRyZXNzLCB0aGUgYnJvd3NlciB3aWxsIGVzdGFibGlzaCBhIGNvbm5lY3Rpb24gdG8gdGhlIG9yaWdpbmFsIGNlcnRpZmljYXRlIGluc3RhbGxlZCB3aXRoaW4gdGhlIElQIGFkZHJlc3MuPC9wPjxwPkR1cmluZyB0aGUgZXN0YWJsaXNobWVudCBvZiBhbiBTU0wvVExTIHNlc3Npb24sIHRoZSBjbGllbnQncyBicm93c2VyIGNvbXBhcmVzIHRoZSBDb21tb24gTmFtZSB0aGUgcHJpbWFyeSBjZXJ0aWZpY2F0ZSBpcyBpc3N1ZWQgZm9yLCB3aXRoIHRoZSBkb21haW4gbmFtZSB0aGUgYnJvd3NlciB0cmllcyB0byByZXNvbHZlLiBJZiB0aGUgQ29tbW9uIE5hbWUgZGlmZmVycyBmcm9tIHRoZSBkb21haW4gbmFtZSB0aGUgcmVxdWVzdCB3YXMgc2VudCB0bywgdGhlIENvbW1vbiBOYW1lIG1pc21hdGNoIHdhcm5pbmcgb2NjdXJzLjwvcD48cD48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF83LmpwZyIgYWx0PSJDZXJ0X21pc21hdGNoXzcuanBnIiB3aWR0aD0iNDk4IiBoZWlnaHQ9IjM1NyIgYm9yZGVyPSIwIiAvPjwvcD48cD5UaGUgd2FybmluZyBjbGFpbXMgdGhhdCB0aGUgY2VydGlmaWNhdGUgdGhhdCBoYXMgYmVlbiBwaWNrZWQgdXAgYnkgcmVxdWVzdCBpcyBpc3N1ZWQgZm9yIGRvbWFpbnRlc3QuY29tLiBUaGlzIG9jY3VycmVkIGJlY2F1c2UgdGhlIGRvbWFpbiBuYW1lIGluIHRoZSByZXF1ZXN0IGRpZCBub3QgbWF0Y2ggdGhlIGRvbWFpbiBuYW1lIHRoZSBjZXJ0aWZpY2F0ZSBpcyBpc3N1ZWQgZm9yLiBJZiB5b3VyIHdlYiBob3N0LCBhcyB3ZWxsIGFzIHdlIGRvLCBwcm92aWRlcyA8YSBocmVmPSJodHRwOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85MjU5Ij5TTkk8L2E+IChTZXJ2ZXIgTmFtZSBpbmRpY2F0aW9uKSB0aGF0IGFsbG93cyB0byBob3N0IHNldmVyYWwgY2VydGlmaWNhdGVzIG9uIHRoZSBzYW1lIElQIGFkZHJlc3MsIHlvdSB3aWxsIG5vdCBuZWVkIGFuIGFkZGl0aW9uYWwgSVAgYWRkcmVzcy4gVGhlIHNhbWUgd2FybmluZyBjYW4gYXBwZWFyIGlmIHRoZSBjZXJ0aWZpY2F0ZSBmb3IgdGhlIGhvc3RuYW1lIHlvdSBhcmUgdHJ5aW5nIHRvIHJlYWNoIChpbiBvdXIgY2FzZSBzc2wtY2VydGlmaWNhdGUtaG9zdC5jb20pIGlzIG5vdCBpbnN0YWxsZWQgb24gdGhlIHNlcnZlciBldmVuIHdpdGggU05JIGVuYWJsZWQuPC9wPjxwPlRoZSBFcnJvciBDb2RlIGlzIG5vdCBhbHdheXMgdGhlIHNhbWU7IGl0IGNhbiBhbHNvIGJlIHNlY19lcnJvcl91bnRydXN0ZWRfaXNzdWVyIGluIEZpcmVmb3gsIGxpa2Ugb24gdGhlIHNjcmVlbnNob3QgYmVsb3c6IDwvcD48cD48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF84LmpwZyIgYWx0PSJDZXJ0X21pc21hdGNoXzguanBnIiB3aWR0aD0iNDk5IiBoZWlnaHQ9IjQxMSIgYm9yZGVyPSIwIiAvPjwvcD48cD5UaGUgZXJyb3IgY29kZSBzZWNfZXJyb3JfdW50cnVzdGVkX2lzc3VlciBpbnN0ZWFkIG9mIHNzbF9lcnJvcl9iYWRfY2VydF9kb21haW4gaW4gdGhpcyBjYXNlIG1lYW5zIHRoYXQgdGhlIHByaW1hcnkgY2VydGlmaWNhdGUgZm9yIHRoaXMgSVAgYWRkcmVzcyAoY2VydCBmb3IgdGVzdGRvbWFpbi5jb20pIGlzIG5vdCBpc3N1ZWQgYnkgYSB0cnVzdGVkIENlcnRpZmljYXRlIEF1dGhvcml0eSAoaS5lLiBpdOKAmXMgc2VsZi1zaWduZWQpLiA8L3A+PHA+PGI+U29sdXRpb246PC9iPjwvcD48cD5JZiB5b3UgZmFjZSBzdWNoIGFuIGVycm9yLCBwbGVhc2UgY29udGFjdCB5b3VyIGhvc3RpbmcgcHJvdmlkZXIgaW4gb3JkZXIgdG8gb2J0YWluIGEgZGVkaWNhdGVkIElQIGZvciB5b3VyIHdlYnNpdGUuIE9uY2UgeW91IGdldCBhIGRlZGljYXRlZCBJUCwgeW91IGNhbiBpbnN0YWxsIHRoZSBjZXJ0aWZpY2F0ZSB3aXRoaW4gdGhpcyBJUC4gQmVmb3JlIHJlcXVlc3RpbmcgYSBkZWRpY2F0ZWQgSVAgeW91IG1heSB2ZXJpZnkgd2l0aCB5b3VyIHdlYiBob3N0IGlmIHRoZXkgc3VwcG9ydCBTTkkgdGVjaG5vbG9neS4gPC9wPjwvbGk+DQoJCQkJPGxpPlRoZSBDZXJ0aWZpY2F0ZSBpcyBub3QgaW5zdGFsbGVkDQo8cD5NYWtlIHN1cmUgeW91ciBjZXJ0aWZpY2F0ZSBpcyBpbnN0YWxsZWQgcHJvcGVybHkgb24geW91ciBzZXJ2ZXIuIFlvdSBzaG91bGQgbm90ZSB0aGF0IG1vc3Qgb2YgdGhlIGluc3RhbGxhdGlvbiBjaGVja2VycyB3b3VsZCBub3QgYmUgYWJsZSB0byBzaG93IGFuIGluc3RhbGxlZCBjZXJ0aWZpY2F0ZSBjb3JyZWN0bHkgdW5sZXNzIGl0IGhhcyBhIGRlZGljYXRlZCBJUCBvciBTTkkgdGVjaG5vbG9neSBpcyBzZXQgZm9yIGl0IGNvcnJlY3RseS48L3A+PC9saT4NCgkJCQk8bGk+QSBXaWxkY2FyZCBjZXJ0aWZpY2F0ZSBpcyBpbnN0YWxsZWQgdmlhIGNQYW5lbCBvciBXSE0NCjxwPlRoZSBDb21tb24gTmFtZSBtaXNtYXRjaCB3YXJuaW5nIG1heSBvY2N1ciBpZiBhIHdpbGRjYXJkIGNlcnRpZmljYXRlIGlzIGluc3RhbGxlZCB2aWEgPGI+Y1BhbmVsPC9iPiBvciA8Yj5XSE08L2I+IGZvciB0aGUgYmFyZSBkb21haW4gb25seSwgd2hpbGUgb25lIHRyaWVzIHRvIGVzdGFibGlzaCBhbiBodHRwcyBjb25uZWN0aW9uIHRvIGEgc3ViZG9tYWluIG9mIHRoZSBkb21haW4gdGhlIHdpbGRjYXJkIGNlcnRpZmljYXRlIGlzIGlzc3VlZCBmb3IuIFdpbGRjYXJkIGNlcnRpZmljYXRlcyBhcmUgc3VwcG9zZWQgdG8gY292ZXIgdGhlIG5ha2VkIGRvbWFpbiBuYW1lIGFuZCBzdWJkb21haW5zIG9mIHRoZSBzYW1lIGxldmVsLiBIb3dldmVyLCBpZiBhIHdpbGRjYXJkIGNlcnRpZmljYXRlIGlzIGluc3RhbGxlZCBmb3IgYSBiYXJlIGRvbWFpbiB2aWEgY1BhbmVsIG9yIFdITSwgc3ViZG9tYWlucyB3aWxsIG5vdCBiZSBzZWN1cmVkIGF1dG9tYXRpY2FsbHkuIElmIGEgc2hhcmVkIElQIHdhcyB1c2VkIChldmVuIHdpdGggU05JIHRlY2hub2xvZ3kpIHRoZSByZXF1ZXN0IGNhbm5vdCBmaW5kIHRoZSBjZXJ0aWZpY2F0ZSB3aXRoIGEgbWF0Y2hpbmcgQ29tbW9uIE5hbWUgdGhlcmVmb3JlLCByZXF1ZXN0IHBpY2tzIHVwIGEgcHJpbWFyeSBjZXJ0aWZpY2F0ZSB0aGF0IHJlc29sdmVzIHVuZGVyIHRoZSBJUCBhZGRyZXNzIHRoZSBkb21haW4gbmFtZSBpbiByZXF1ZXN0IHJlc29sdmVzIHRvLiA8L3A+PHA+SW4gY2FzZSBvZiBhIGRlZGljYXRlZCBJUCB0aGUgZGV0YWlscyBvZiBhIG1pc21hdGNoIHdhcm5pbmcgbWF5IGJlIGNvbmZ1c2luZyBhIGxpdHRsZSBiaXQsIGJ1dCB0aGUgcHJvY2VzcyBpcyB0aGUgc2FtZSAtIHRoZSByZXF1ZXN0IHdpbGwgZmluZCB5b3VyIHdpbGRjYXJkIGNlcnRpZmljYXRlIGFzIGEgcHJpbWFyeSBvbmUgYW5kIGNvbnNpZGVyIGl0IGFzIGEgbm90IG1hdGNoaW5nIG9uZSwgYXMgdGhlIHN1YmRvbWFpbiBuYW1lIGlzIG5vdCBlbmNvZGVkIGluIHRoZSBjZXJ0aWZpY2F0ZeKAmXMgYm9keS4NCjwvcD48cD48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF8xMC5qcGciIGFsdD0iQ2VydF9taXNtYXRjaF8xMC5qcGciIHdpZHRoPSI0ODgiIGhlaWdodD0iMzc0IiBib3JkZXI9IjAiIC8+PC9wPjxwPjxiPlNvbHV0aW9uOjwvYj4gVGhpcyBpc3N1ZSBvY2N1cnMgZHVlIHRvIHRlY2huaWNhbCB3aXRoZHJhd2FscyBvZiBjUGFuZWwgYW5kIFdITSwgdGhlcmUgYXJlIHNldmVyYWwgd2F5cyB0byBzb2x2ZSBpdDogPC9wPjxwPmEpIGluc3RhbGwgdGhlIGNlcnRpZmljYXRlIGZvciBlYWNoIHN1YmRvbWFpbiB2aWEgV0hNL2NQYW5lbDwvcD48cD5iKSBpZiB5b3UgaGF2ZSByb290IGFjY2VzcyB0byB0aGUgc2VydmVyLCBwbGVhc2UgaW5zdGFsbCBpdCBkaXJlY3RseSBvbiB0aGUgc2VydmVyIGVkaXRpbmcgYSBWaXJ0dWFsSG9zdCBmaWxlLiBZb3UgY2FuIGZpbmQgbW9yZSBpbmZvcm1hdGlvbiByZWdhcmRpbmcgdGhpcyBxdWVzdGlvbiA8YSBocmVmPSJodHRwOi8vd3d3LnRoZWNwYW5lbGFkbWluLmNvbS9pbnN0YWxsaW5nLXdpbGRjYXJkLXNzbC1jZXJ0aWZpY2F0ZS8iPmhlcmUuPC9hPjwvcD48L2xpPg0KCQkJCTxsaT5Zb3UgYXJlIHRyeWluZyB0byBhY2Nlc3MgYW4gSVAgYWRkcmVzcw0KPHA+VGhlIGVycm9yIG9jY3VycyBpZiBvbmUgdHJpZXMgdG8gZXN0YWJsaXNoIGFuIGh0dHBzIGNvbm5lY3Rpb24gZm9yIGFuIElQIGFkZHJlc3MuIFJlZ3VsYXIgU1NMIGNlcnRpZmljYXRlcyBjYW4gYmUgaXNzdWVkIG9ubHkgZm9yIGEgRlFETiAoRnVsbHkgUXVhbGlmaWVkIERvbWFpbiBOYW1lKS4gRXZlbiBpZiB5b3UgaGF2ZSBhIGRlZGljYXRlZCBJUCBhZGRyZXNzLCB0aGUgY29tbW9uIG5hbWUgbWlzbWF0Y2ggd2lsbCBiZSBzaG93biBiZWNhdXNlIHRoZSBodHRwcyByZXF1ZXN0IHZpYSBhbiBJUCBhZGRyZXNzIGRvZXMgbm90IGNvbnRhaW4gdGhlIHNlcnZlciBuYW1lIChkb21haW4vc3ViZG9tYWluIG5hbWUpIGl0c2VsZiwgdGhlcmVmb3JlIHRoZXJlIGlzIG5vIHdheSB0byBhdm9pZCB0aGUgd2FybmluZyB0cnlpbmcgdG8gYWNjZXNzIHRoZSBzaXRlIHZpYSBhbiBJUCBhZGRyZXNzLCBhcyBhIHJlZ3VsYXIgY2VydGlmaWNhdGUgaXMgaXNzdWVkIGZvciBhIGRvbWFpbi9zdWJkb21haW4gbmFtZS48L3A+PHA+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL0NlcnRfbWlzbWF0Y2hfMTEuanBnIiBhbHQ9IkNlcnRfbWlzbWF0Y2hfMTEuanBnIiB3aWR0aD0iNTE0IiBoZWlnaHQ9IjQxMyIgYm9yZGVyPSIwIiAvPjwvcD48cD48Yj5Tb2x1dGlvbjo8L2I+IFBsZWFzZSBhY2Nlc3MgeW91ciB3ZWIgcGFnZSB1c2luZyB0aGUgaG9zdG5hbWUsIG5vdCBhbiBJUCBhZGRyZXNzLjwvcD48L2xpPg0KCQkJCTxsaT5EaWZmZXJlbnQgbGV2ZWxzIG9mIHN1YmRvbWFpbnMgZm9yIFdpbGRjYXJkIGNlcnRpZmljYXRlcw0KPHA+VGhlIGVycm9yIGNhbiBhcHBlYXIgYWxzbyB3aXRoIGEgd2lsZGNhcmQgY2VydGlmaWNhdGUsIGlmIHlvdSBhcmUgdHJ5aW5nIHRvIGFjY2VzcyBhIHN1YmRvbWFpbiBvZiB0aGUgZm91cnRoIG9yIGEgaGlnaGVyIGxldmVsLCB3aGlsZSBhIHdpbGRjYXJkIGNlcnRpZmljYXRlIGlzIHZhbGlkIGZvciB0aGUgbWFpbiBkb21haW4gYW5kIHN1YmRvbWFpbnMgb2YgdGhlIHRoaXJkIGxldmVsLjwvcD48cD5JZiBhIHdpbGRjYXJkIGNlcnRpZmljYXRlIHdhcyBpc3N1ZWQgZm9yIDxiPiouc3NsLWNlcnRpZmljYXRlLWhvc3QuY29tPC9iPiwgaXQgaXMgdmFsaWQgZm9yIDxiPnNzbC1jZXJ0aWZpY2F0ZS1ob3N0LmNvbTwvYj4gYW5kIGFsbCB0aGUgc3ViZG9tYWlucyBvZiB0aGUgdGhpcmQgbGV2ZWwsIGxpa2UgPGI+c3ViMS5zc2wtY2VydGlmaWNhdGUtaG9zdC5jb208L2I+LCA8Yj5zdWIyLnNzbC1jZXJ0aWZpY2F0ZS1ob3N0LmNvbTwvYj4sIDxiPnN1YjMuc3NsLWNlcnRpZmljYXRlLWhvc3QuY29tPC9iPiBldGMuLCBidXQgaXQgZG9lcyBub3QgY292ZXIgc3ViZG9tYWlucyBvZiB0aGUgZm91cnRoIG9yIGhpZ2hlciBsZXZlbHMgKGxpa2UgPGI+c3ViMi5zdWIxLnNzbC1jZXJ0aWZpY2F0ZS1ob3N0LmNvbTwvYj4gb3IgPGI+c3ViMy5zdWIyLnN1YjEuZXhhbXBsZS5jb208L2I+KTwvcD48cD48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvQ2VydF9taXNtYXRjaF8xMi5qcGciIGFsdD0iQ2VydF9taXNtYXRjaF8xMi5qcGciIHdpZHRoPSI1MTQiIGhlaWdodD0iMzkxIiBib3JkZXI9IjAiIC8+PC9wPjxwPjxiPlNvbHV0aW9uOjwvYj4gVG8gY292ZXIgc2V2ZXJhbCBsZXZlbHMgb2Ygc3ViZG9tYWlucyB5b3UgbWF5IGVpdGhlciBpc3N1ZSBzZXZlcmFsIGRpZmZlcmVudCBXaWxkY2FyZCBjZXJ0aWZpY2F0ZXMgb3IgYSBVQ0MgY2VydGlmaWNhdGUuPC9wPjwvbGk+DQoJCQkJPGxpPkROUyByZWNvcmRzIGZvciB0aGUgZG9tYWluIGhhdmUgcmVjZW50bHkgYmVlbiBjaGFuZ2VkDQo8cD4NClRoZSBDb21tb24gTmFtZSBtaXNtYXRjaCBtYXkgb2NjdXIgaWYgdGhlIElQIGFkZHJlc3MgeW91ciBkb21haW4gbmFtZSBpcyBwb2ludGVkIHRvIGhhcyBiZWVuIHJlY2VudGx5IGNoYW5nZWQuIElmIHlvdSBvcmRlcmVkIGEgZGVkaWNhdGVkIElQIGFuZCB0aGUgY2VydGlmaWNhdGUgaGFzIGJlZW4gaW5zdGFsbGVkIHNob3J0bHkgYWZ0ZXIgdGhhdCwgdGhlcmUgaXMgYSBoaWdoIHBvc3NpYmlsaXR5IHRoYXQgdGhlcmUgaXMgRE5TIHByb3BhZ2F0aW9uIGFuZCB0aGUgZG9tYWluIHN0aWxsIHJlc29sdmVzIHRvIHRoZSBwcmV2aW91cyBJUCBhZGRyZXNzLCB3aGlsZSB0aGUgY2VydGlmaWNhdGUgaXMgdW5kZXIgdGhlIG5ldyBvbmUuICBUaGVyZSBtYXkgYmUgYSBjZXJ0aWZpY2F0ZSBmb3IgYW5vdGhlciBkb21haW4gaW5zdGFsbGVkIG9uIHRoZSBwcmV2aW91cyBJUCBhZGRyZXNzLCB3aGljaCBpcyB3aHkgdGhlIGVycm9yIG9jY3Vycy48L3A+PHA+PGI+U29sdXRpb246PC9iPiBObyBhY3Rpb25zIGFyZSByZXF1aXJlZDsgcGxlYXNlIGFsbG93IHNvbWUgdGltZSBmb3IgdGhlIEROUyByZWNvcmRzIHRvIGJlIHVwZGF0ZWQuIDwvcD48cD7CoMKgwqDCoMKgwqANCklmIHlvdSBoYXZlIG5vdCBmb3VuZCBhIHNvbHV0aW9uIGZvciB5b3VyIGlzc3VlIGluIHRoaXMgYXJ0aWNsZSBvciBzdGlsbCBoYXZlIGFueSBxdWVzdGlvbnMsIHBsZWFzZSBjb250YWN0IG91ciA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL2hlbHAtY2VudGVyLyI+U1NMIFN1cHBvcnQgVGVhbTwvYT4uDQo8L3A+PC9saT4NCgkJPC9vbD4NCg==","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2022-11-17T16:15:03.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2015-02-04T22:12:38.0000000","ApprovalDatetime":"2015-02-04T22:16:40.0000000","RequestCount":98818,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":2,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":14,"CategoryName":"SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2223,"CategoryName":"Browser errors"}],"AssociatedCategories":[{"CategoryId":2223,"CategoryName":"Browser errors","CategoryDisplayName":"SSL CertificatesBrowser errors"}],"AssociatedTags":[],"RelatedArticles":[{"ArticleId":795,"PreferedCategoryId":14,"ArticleTypeId":0,"ArticleName":"How to install SSL certificates","ArticleTypeName":null,"Title":"How to install SSL certificates","LiveDateTime":null,"ModifiedDateTime":"09/07/2022","MarkedAsNew":false,"MarkedAsFeatured":false}],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":2223}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","ParentCategoryId":14,"Parent_Category_Name":"SSL Certificates","FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":false,"CreatedDateTime":"02/09/2015 18:27:51","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":14,"CategoryName":"SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":2223,"CategoryName":"Browser errors"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":9459,"Title":"I get \"Certificate is not trusted because it is self-signed\" error message when I visit my site","ArticleName":"I get \"Certificate is not trusted because it is self-signed\" error message when I visit my site","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/06/2022"},{"ArticleId":9468,"Title":"Why do I get \"Common name mismatch\" error in my browser?","ArticleName":"Why do I get \"Common name mismatch\" error in my browser?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/17/2022"},{"ArticleId":9577,"Title":"SSL notifications in Chrome and their meaning","ArticleName":"SSL notifications in Chrome and their meaning","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/07/2023"},{"ArticleId":901,"Title":"My SSL is installed, why do I get the warning ‘Not secure’ in browsers?","ArticleName":"My SSL is installed, why do I get the warning ‘Not secure’ in browsers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/25/2024"},{"ArticleId":807,"Title":"Firefox error code: ssl_error_rx_record_too_long","ArticleName":"Firefox error code: ssl_error_rx_record_too_long","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/17/2019"}],"AssociatedTags":[],"CategoryId":2223,"CategoryName":"Browser errors"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}The error message differs depending on browsers. The most popular ones are listed below:
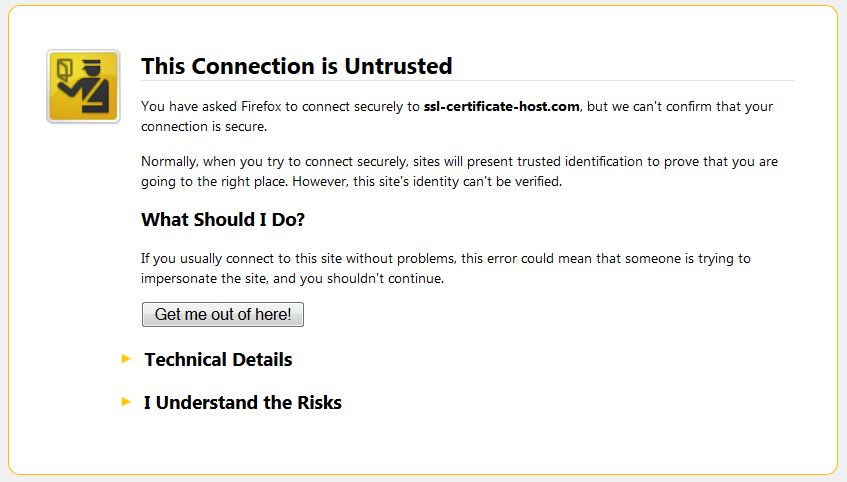
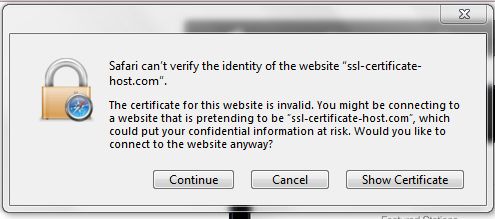
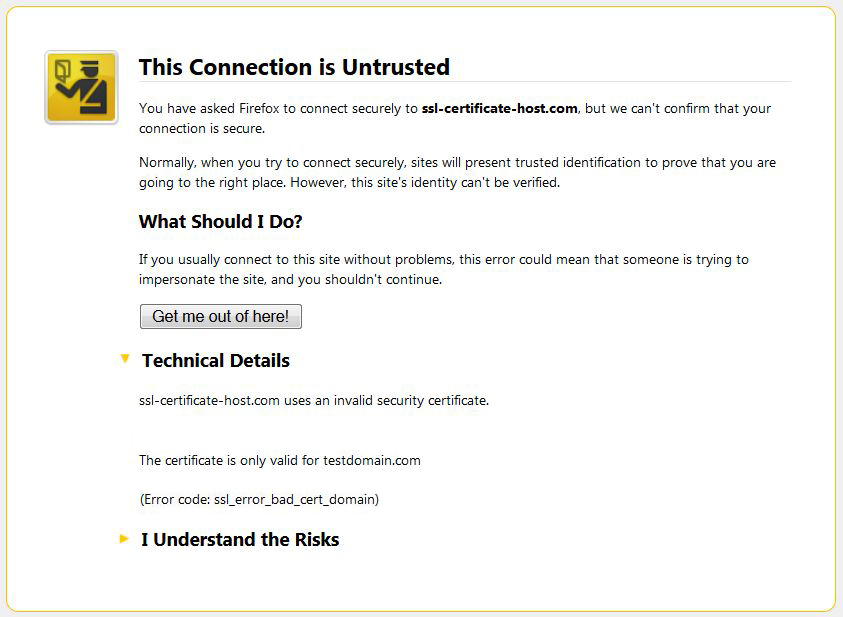
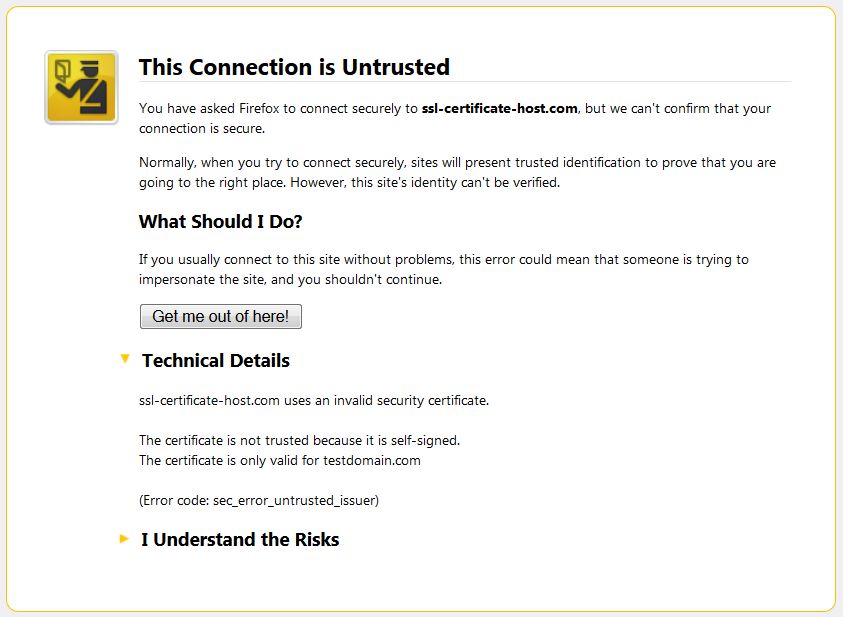
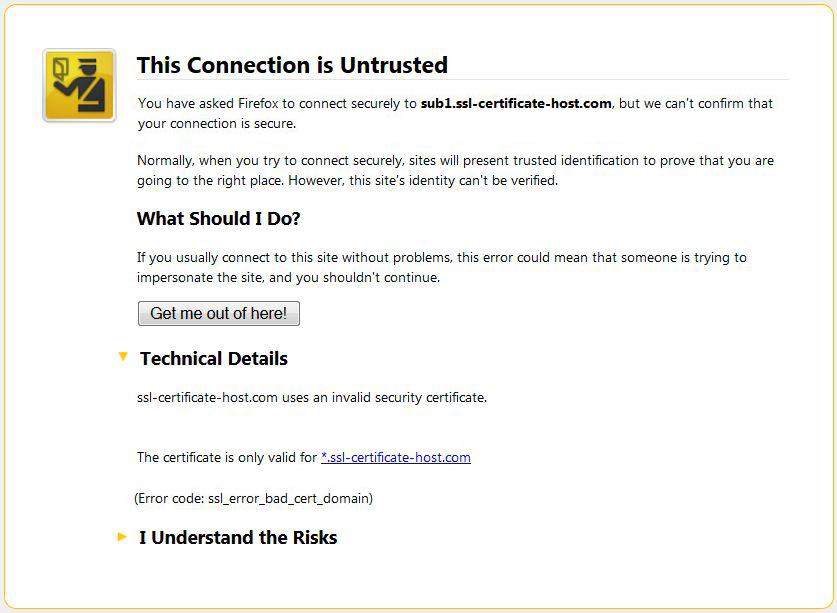
Firefox:
Usually a dedicated IP is required in order to install the SSL certificate. If there is already a certificate installed within the same IP address, the browser will establish a connection to the original certificate installed within the IP address.
During the establishment of an SSL/TLS session, the client's browser compares the Common Name the primary certificate is issued for, with the domain name the browser tries to resolve. If the Common Name differs from the domain name the request was sent to, the Common Name mismatch warning occurs.
The warning claims that the certificate that has been picked up by request is issued for domaintest.com. This occurred because the domain name in the request did not match the domain name the certificate is issued for. If your web host, as well as we do, provides SNI (Server Name indication) that allows to host several certificates on the same IP address, you will not need an additional IP address. The same warning can appear if the certificate for the hostname you are trying to reach (in our case ssl-certificate-host.com) is not installed on the server even with SNI enabled.
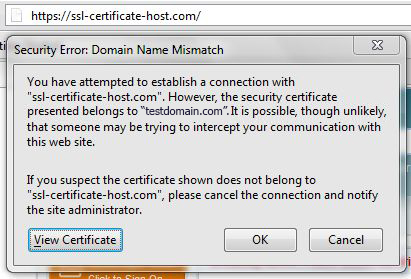
The Error Code is not always the same; it can also be sec_error_untrusted_issuer in Firefox, like on the screenshot below:
The error code sec_error_untrusted_issuer instead of ssl_error_bad_cert_domain in this case means that the primary certificate for this IP address (cert for testdomain.com) is not issued by a trusted Certificate Authority (i.e. it’s self-signed).
Solution:
If you face such an error, please contact your hosting provider in order to obtain a dedicated IP for your website. Once you get a dedicated IP, you can install the certificate within this IP. Before requesting a dedicated IP you may verify with your web host if they support SNI technology.
Make sure your certificate is installed properly on your server. You should note that most of the installation checkers would not be able to show an installed certificate correctly unless it has a dedicated IP or SNI technology is set for it correctly.
The Common Name mismatch warning may occur if a wildcard certificate is installed via cPanel or WHM for the bare domain only, while one tries to establish an https connection to a subdomain of the domain the wildcard certificate is issued for. Wildcard certificates are supposed to cover the naked domain name and subdomains of the same level. However, if a wildcard certificate is installed for a bare domain via cPanel or WHM, subdomains will not be secured automatically. If a shared IP was used (even with SNI technology) the request cannot find the certificate with a matching Common Name therefore, request picks up a primary certificate that resolves under the IP address the domain name in request resolves to.
In case of a dedicated IP the details of a mismatch warning may be confusing a little bit, but the process is the same - the request will find your wildcard certificate as a primary one and consider it as a not matching one, as the subdomain name is not encoded in the certificate’s body.
Solution: This issue occurs due to technical withdrawals of cPanel and WHM, there are several ways to solve it:
a) install the certificate for each subdomain via WHM/cPanel
b) if you have root access to the server, please install it directly on the server editing a VirtualHost file. You can find more information regarding this question here.
The error occurs if one tries to establish an https connection for an IP address. Regular SSL certificates can be issued only for a FQDN (Fully Qualified Domain Name). Even if you have a dedicated IP address, the common name mismatch will be shown because the https request via an IP address does not contain the server name (domain/subdomain name) itself, therefore there is no way to avoid the warning trying to access the site via an IP address, as a regular certificate is issued for a domain/subdomain name.
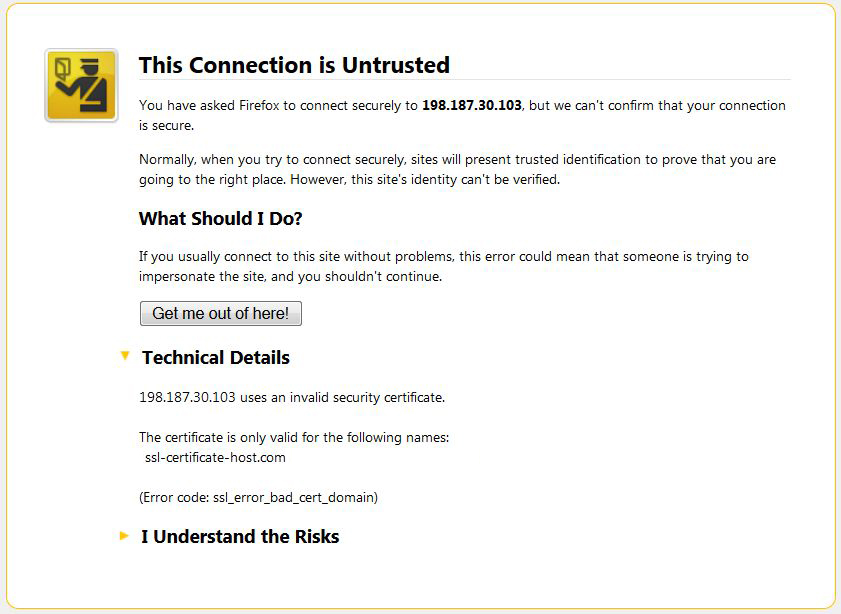
Solution: Please access your web page using the hostname, not an IP address.
The error can appear also with a wildcard certificate, if you are trying to access a subdomain of the fourth or a higher level, while a wildcard certificate is valid for the main domain and subdomains of the third level.
If a wildcard certificate was issued for *.ssl-certificate-host.com, it is valid for ssl-certificate-host.com and all the subdomains of the third level, like sub1.ssl-certificate-host.com, sub2.ssl-certificate-host.com, sub3.ssl-certificate-host.com etc., but it does not cover subdomains of the fourth or higher levels (like sub2.sub1.ssl-certificate-host.com or sub3.sub2.sub1.example.com)
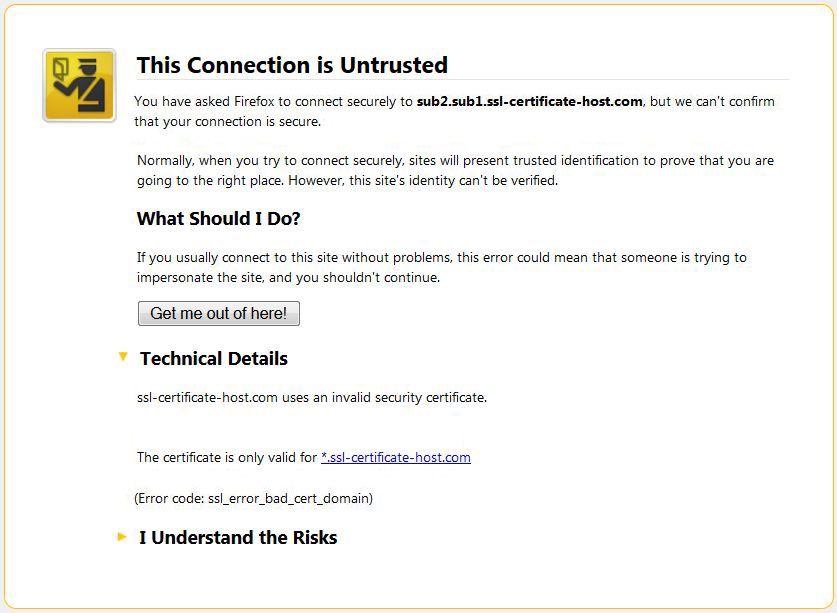
Solution: To cover several levels of subdomains you may either issue several different Wildcard certificates or a UCC certificate.
The Common Name mismatch may occur if the IP address your domain name is pointed to has been recently changed. If you ordered a dedicated IP and the certificate has been installed shortly after that, there is a high possibility that there is DNS propagation and the domain still resolves to the previous IP address, while the certificate is under the new one. There may be a certificate for another domain installed on the previous IP address, which is why the error occurs.
Solution: No actions are required; please allow some time for the DNS records to be updated.
If you have not found a solution for your issue in this article or still have any questions, please contact our SSL Support Team.
Need help? We're always here for you.