{"/api/v1/ncpl/simplekb/getarticle:\"{\\\"articleId\\\":10314,\\\"categoryId\\\":33}\"":{"body":{"Id":10314,"FriendlyId":"","ArticleTypeId":0,"Title":"SSL Certificate installation on apache2 (Debian, Ubuntu)","ArticleName":"SSL Certificate installation on apache2 (Debian, Ubuntu)","ArticleSummary":null,"PreponedSummary":false,"Approved":true,"Body":"DQoJCTxzdHlsZT48IVtDREFUQVsNCnRhYmxlIHsNCiAgZm9udC1mYW1pbHk6IGFyaWFsLCBzYW5zLXNlcmlmOw0KICBib3JkZXItY29sbGFwc2U6IGNvbGxhcHNlOw0KICB3aWR0aDogMTAwJTsNCn0NCg0KdGQsIHRoIHsNCiAgYm9yZGVyOiAxcHggc29saWQgI2RkZGRkZDsNCiAgdGV4dC1hbGlnbjogbGVmdDsNCiAgcGFkZGluZzogOHB4Ow0KfQ0KDQp0cjpudGgtY2hpbGQoZXZlbikgew0KICBiYWNrZ3JvdW5kLWNvbG9yOiAjZGRkZGRkOw0KfQ0KXV0+PC9zdHlsZT4NCgkJPHRhYmxlPg0KCQkJCTx0Ym9keT4NCgkJCQkJCTx0cj4NCgkJCQkJCQkJPHRkIGJnY29sb3I9IiNmN2ViZWIiPg0KCQkJCQkJCQkJCTxiPk5vdGU8L2I+OiBCZWZvcmUgeW91IGJlZ2luLCBlbnN1cmUgeW914oCZcmUgYWxsIHNldCB3aXRoIHRoZSA8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTQyMy8zMy9pbnN0YWxsaW5nLWFuLXNzbC1jZXJ0aWZpY2F0ZS1vbi1hcGFjaGUiIGxpbmt0ZXh0PSJwcmVyZXF1aXNpdGVzIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+cHJlcmVxdWlzaXRlczwvYT4uPC90ZD4NCgkJCQkJCTwvdHI+DQoJCQkJPC90Ym9keT4NCgkJPC90YWJsZT4NCgkJPHN0eWxlPjwhW0NEQVRBWw0KdGFibGUgew0KICBmb250LWZhbWlseTogYXJpYWwsIHNhbnMtc2VyaWY7DQogIGJvcmRlci1jb2xsYXBzZTogY29sbGFwc2U7DQogIHdpZHRoOiAxMDAlOw0KfQ0KDQp0ZCwgdGggew0KICBib3JkZXI6IDFweCBzb2xpZCAjZGRkZGRkOw0KICB0ZXh0LWFsaWduOiBsZWZ0Ow0KICBwYWRkaW5nOiA4cHg7DQp9DQoNCnRyOm50aC1jaGlsZChldmVuKSB7DQogIGJhY2tncm91bmQtY29sb3I6ICNkZGRkZGQ7DQp9DQpdXT48L3N0eWxlPg0KCQk8dGFibGU+DQoJCQkJPHRib2R5Pg0KCQkJCQkJPHRyPg0KCQkJCQkJCQk8dGQgYmdjb2xvcj0iI2JkZjBhMCI+DQoJCQkJCQkJCQkJPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzEwMzEzLzMzL3NzbC1jZXJ0aWZpY2F0ZS1pbnN0YWxsYXRpb24tb24taHR0cGQtY2VudG9zLyIgbGlua3RleHQ9IlNTTCBpbnN0YWxsYXRpb24gaW5zdHJ1Y3Rpb25zIGZvciBDZW50T1MiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj5TU0wgaW5zdGFsbGF0aW9uIGluc3RydWN0aW9ucyBmb3IgQ2VudE9TPC9hPg0KCQkJCQkJCQk8L3RkPg0KCQkJCQkJPC90cj4NCgkJCQk8L3Rib2R5Pg0KCQk8L3RhYmxlPg0KCQk8YnIgLz4NCgkJPGJyIC8+DQoJCTx1bD4NCgkJCQk8bGk+DQoJCQkJCQk8YSBocmVmPSIjMSI+SW5zdGFsbGF0aW9uIHN0ZXBzDQo8L2E+DQoJCQkJPC9saT4NCgkJCQk8bGk+DQoJCQkJCQk8YSBocmVmPSIjMiI+VGlwcyBhbmQgdHJvdWJsZXNob290ZXJzPC9hPg0KCQkJCTwvbGk+DQoJCTwvdWw+DQoJCTxiciAvPg0KCQk8aDIgaWQ9IjEiPkluc3RhbGxhdGlvbiBzdGVwczwvaDI+DQoJCTxvbD4NCgkJCQk8bGk+DQoJCQkJCQk8Yj5JbnN0YWxsYXRpb24gY2hlY2s8L2I+DQoJCQkJCQk8YnIgLz4NCgkJCQkJCTxiciAvPkZpcnN0LCB3ZSB3aWxsIGNoZWNrIHRoZSBleGFjdCBsb2NhdGlvbiBvZiB0aGUgY3VycmVudCBjb25maWd1cmF0aW9uIGZpbGUgZm9yIEhUVFAgd2Vic2l0ZXMuIEZvciB0aGF0LCBydW4gdGhlIGZvbGxvd2luZyBjb21tYW5kOjxiciAvPjxiciAvPjxjb2RlPnN1ZG8gYXBhY2hlY3RsIC1TPC9jb2RlPjxiciAvPjxiciAvPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hcGFjaGVfMTYucG5nIiAvPjxiciAvPjxiciAvPldlIGNhbiBzZWUgdGhlIHdlYnNpdGUgY29uZmlndXJhdGlvbiBmaWxlICh0aGUgb25lIGZvciBub24tc2VjdXJlZCBIVFRQIGNvbm5lY3Rpb25zIHZpYSBwb3J0IDgwKSBpbiB0aGUgb3V0cHV0LiBJdCBpcyB1c3VhbGx5IGNhbGxlZCAiPGNvZGU+MDAwLWRlZmF1bHQuY29uZjwvY29kZT4iLjxiciAvPjxiciAvPlRoZSBkZWZhdWx0IGZvbGRlciBmb3Igc3VjaCBhIGZpbGUgbG9jYXRpb24gaXMgPGNvZGU+L2V0Yy9hcGFjaGUyL3NpdGVzLWVuYWJsZWQ8L2NvZGU+LjxiciAvPjxiciAvPkluIHRoaXMgZ3VpZGUsIHdlIHdpbGwgc2hvdyBpbiBkZXRhaWwgaG93IHRvIGFkZCB0aGUgc2V0dGluZ3MgZm9yIEhUVFBTIHBvcnQgNDQzIGludG8gdGhlIHNhbWUgY29uZmlndXJhdGlvbiBmaWxlLiBIb3dldmVyLCB3ZSBhbHNvIHJlY29tbWVuZCByZXZpZXdpbmcgYWxsIHBvc3NpYmxlIHdheXMgdG8gcHJvY2VlZCAtIGxpa2Ugc2VwYXJhdGUgY29uZmlndXJhdGlvbiBmaWxlIGNyZWF0aW9uIGluIHRoZSA8Y29kZT4vZXRjL2FwYWNoZTIvc2l0ZXMtYXZhaWxhYmxlPC9jb2RlPiBvciA8Y29kZT4vZXRjL2FwYWNoZTIvc2l0ZXMtZW5hYmxlZDwvY29kZT4gZm9sZGVyIC0gPGEgaHJlZj0iIzMiPmhlcmU8L2E+DQogaW4gdGhlICdUaXBzIGFuZCB0cm91Ymxlc2hvb3RpbmdzJyBwYXJ0IG9mIHRoaXMgZ3VpZGUuPGJyIC8+PGJyIC8+PGJyIC8+PC9saT4NCgkJCQk8bGk+DQoJCQkJCQk8Yj5FbmFibGluZyBTU0wvVExTIHN1cHBvcnQgb24gQXBhY2hlPC9iPg0KCQkJCQkJPGJyIC8+DQoJCQkJCQk8YnIgLz5CZWZvcmUgd2UgcHJvY2VlZCBhbnkgZnVydGhlciwgd2Ugd2lsbCBuZWVkIHRvIG1ha2Ugc3VyZSB0aGF0IFNTTC9UTFMgc3VwcG9ydCBpcyBlbmFibGVkIG9uIHRoZSB3ZWJzZXJ2ZXIuIEZvciB0aGF0LCB3ZSB3aWxsIG5lZWQgdG8gcnVuIHRoZSBmb2xsb3dpbmcgY29tbWFuZDo8YnIgLz48YnIgLz48Y29kZT5zdWRvIGEyZW5tb2Qgc3NsPC9jb2RlPjxiciAvPjxiciAvPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hcGFjaGVfMTcucG5nIiAvPjxiciAvPjxiciAvPklmIHRoZSBjb21tYW5kIHJlc3BvbmRzIHdpdGgg4oCcPGNvZGU+TW9kdWxlIHNzbCBhbHJlYWR5IGVuYWJsZWQ8L2NvZGU+4oCdLCB0aGVuIHRoZSBtb2R1bGUgaGFzIGFscmVhZHkgYmVlbiBlbmFibGVkPGJyIC8+PGJyIC8+SWYgdGhlIG1vZHVsZSB3YXMgbm90IHlldCBlbmFibGVkLCB0aGUgY29tbWFuZCB3aWxsIHJlc3BvbmQgd2l0aCDigJg8Y29kZT5FbmFibGluZyBtb2R1bGUgc3NsPC9jb2RlPuKAmSBhbmQgd2lsbCBjb21wbGV0ZSB0aGUgbW9kdWxlIGVuYWJsaW5nLjxiciAvPjxiciAvPkFmdGVyIHRoYXQsIHJlYm9vdCB0aGUgd2Vic2VydmVyIHNvIHRoYXQgdGhlIG1vZHVsZSBjYW4gYmUgYXBwbGllZCB0byBBcGFjaGUuIFRoZSBzZXJ2aWNlIGNhbiBiZSByZXN0YXJ0ZWQgYnkgZW50ZXJpbmcgdGhlIGZvbGxvd2luZyBjb21tYW5kOjxiciAvPjxiciAvPjxjb2RlPnN1ZG8gc2VydmljZSBhcGFjaGUyIHJlc3RhcnQ8YnIgLz48YnIgLz48L2NvZGU+PC9saT4NCgkJCQk8bGk+DQoJCQkJCQk8Yj5Db25maWd1cmluZyB0aGUgd2Vic2VydmVyPC9iPg0KCQkJCQkJPGJyIC8+DQoJCQkJCQk8YnIgLz5Ob3csIGNvbmZpZ3VyZSB0aGUgd2Vic2l0ZSB0byB3b3JrIHdpdGggdGhlIFNTTCBjZXJ0aWZpY2F0ZS48YnIgLz48YnIgLz48dWw+PGxpPklmIHRoZXJlIHdlcmUgbm8gU1NMcyBpbnN0YWxsZWQgb24gdGhlIHdlYnNlcnZlciBwcmV2aW91c2x5LCBjaGVjayB0aGUgY29uZmlndXJhdGlvbiBmaWxlIG5hbWUgZm9yIHRoZSBIVFRQIHBvcnQgODAgYW5kIG9wZW4gaXQgaW4geW91ciB0ZXh0IGVkaXRvciBvZiBjaG9pY2UgKG5hbm8sIHZpLCBldGMuKS48L2xpPjwvdWw+PGJyIC8+VGhlIGNvbmZpZ3VyYXRpb24gZmlsZSBuYW1lIGNhbiBiZSBjaGVja2VkIHVzaW5nIHRoZSBjb21tYW5kOiA8Y29kZT5hcGFjaGVjdGwgLVM8L2NvZGU+PGJyIC8+PGJyIC8+SXQgaXMgdXN1YWxseSBsb2NhdGVkIGluIHRoZSA8Y29kZT4vZXRjL2FwYWNoZTIvc2l0ZXMtZW5hYmxlZDwvY29kZT4gZm9sZGVyLjxiciAvPjxiciAvPjxpPjxiPk5vdGU8L2I+OiBJZiB5b3UgYXJlIGZvbGxvd2luZyBhbm90aGVyIHdheSBmcm9tIDxhIGhyZWY9IiMzIj50aGVzZSBvbmVzPC9hPiwgdGhlbiBrZWVwIGluIG1pbmQgdGhhdCB5b3VyIGZpbGUgbmFtZSB3aWxsIGJlIGRpZmZlcmVudCwgYW5kIHlvdSBuZWVkIHRvIG9wZW4geW91ciBjb25maWd1cmF0aW9uIGZpbGUgaW5zdGVhZCBvZiB0aGUgZGVmYXVsdCBvbmUuIDwvaT48YnIgLz48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXBhY2hlXzE4LnBuZyIgLz48YnIgLz48YnIgLz5UaGVuIG9wZW4gdGhlIGNvbmZpZ3VyYXRpb24gZmlsZSBhbmQgcGFzdGUgdGhlIGZvbGxvd2luZyBjb2RlIGF0IHRoZSB2ZXJ5IGJvdHRvbSBvZiBpdDo8YnIgLz48YnIgLz48Y29kZT4mbHQ7VmlydHVhbEhvc3QgKjo0NDMmZ3Q7PGJyIC8+U2VydmVyTmFtZSAoRE9NQUlOIE5BTUUgT0YgVEhFIFdFQlNJVEUpPGJyIC8+RG9jdW1lbnRSb290IChST09UIEZPTERFUiBPRiBUSEUgV0VCU0lURSk8YnIgLz48YnIgLz48YnIgLz5TU0xFbmdpbmUgb248YnIgLz5TU0xDZXJ0aWZpY2F0ZUZpbGUgKENlcnRpZmljYXRlIFBBVEgpPGJyIC8+U1NMQ2VydGlmaWNhdGVLZXlGaWxlIChQcml2YXRlIGtleSBQQVRIKTxiciAvPlNTTENlcnRpZmljYXRlQ2hhaW5GaWxlIChDQSBCdW5kbGUgUEFUSCk8YnIgLz4mbHQ7L1ZpcnR1YWxIb3N0Jmd0OzwvY29kZT48YnIgLz48YnIgLz5NYWtlIHN1cmUgdG8gcmVwbGFjZSB0aGUgY29tbWFuZCB2YWx1ZXMgaW4gYnJhY2tldHMgd2l0aCB0aGUgdmFsaWQgaW5mb3JtYXRpb24gZm9yIHlvdXIgZG9tYWluIG5hbWUgb3Igd2Vic2l0ZS48YnIgLz48YnIgLz5JbiBvdXIgY2FzZSwgaXQgaXMgYXMgZm9sbG93czo8YnIgLz48YnIgLz48Y29kZT4mbHQ7VmlydHVhbEhvc3QgKjo0NDMmZ3Q7PGJyIC8+U2VydmVyTmFtZSBleGFtcGxlLmNvbTxiciAvPkRvY3VtZW50Um9vdCAvdmFyL3d3dy9odG1sPGJyIC8+PGJyIC8+PGJyIC8+U1NMRW5naW5lIG9uPGJyIC8+U1NMQ2VydGlmaWNhdGVGaWxlIC9ldGMvc3NsLzEuY3J0PGJyIC8+U1NMQ2VydGlmaWNhdGVLZXlGaWxlIC9ldGMvc3NsLzEua2V5PGJyIC8+U1NMQ2VydGlmaWNhdGVDaGFpbkZpbGUgL2V0Yy9zc2wvMS5jYS1idW5kbGU8YnIgLz4mbHQ7L1ZpcnR1YWxIb3N0Jmd0OzwvY29kZT48YnIgLz48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXBhY2hlXzE5LnBuZyIgLz48YnIgLz48YnIgLz5BZnRlciB0aGF0LCBzYXZlIHRoZSBmaWxlLjxiciAvPjxiciAvPjx1bD48bGk+SWYgdGhlIFNTTCBjZXJ0aWZpY2F0ZSB3YXMgYWxyZWFkeSBpbnN0YWxsZWQgb24gdGhlIHdlYnNlcnZlciwgY2hlY2sgdGhlIGNvbmZpZ3VyYXRpb24gZmlsZSBuYW1lIGZvciBwb3J0IDQ0MyBhbmQgb3BlbiBpdCBpbiB0aGUgdGV4dCBlZGl0b3IuPC9saT48L3VsPjxiciAvPlRoZSBjb25maWd1cmF0aW9uIGZpbGUgbmFtZSBjYW4gYmUgY2hlY2tlZCB1c2luZyB0aGUgY29tbWFuZDogPGNvZGU+YXBhY2hlY3RsIC1TPC9jb2RlPjxiciAvPjxiciAvPjxpbWcgY2xhc3M9ImtiLWltYWdlIiBzcmM9Imh0dHBzOi8vTmFtZWNoZWFwLnNpbXBsZWtiLmNvbS9TaXRlQ29udGVudHMvMi03QzIyRDUyMzZBNDU0M0VCODI3RjNCRDg5MzZFMTUzRS9tZWRpYS9hcGFjaGVfMjAucG5nIiAvPjxiciAvPjxiciAvPlRoZW4sIG1ha2Ugc3VyZSB0byByZXBsYWNlIHRoZSBwYXRocyBvZiB0aGUgY2VydGlmaWNhdGUgZmlsZXMgaW4gdGhlIGZvbGxvd2luZyBzZWN0aW9uczo8YnIgLz48YnIgLz48Y29kZT5TU0xDZXJ0aWZpY2F0ZUZpbGU8YnIgLz5TU0xDZXJ0aWZpY2F0ZUtleUZpbGU8YnIgLz5TU0xDZXJ0aWZpY2F0ZUNoYWluRmlsZTwvY29kZT48YnIgLz48YnIgLz5FbnRlciB0aGUgZnVsbCBwYXRocyB0byB0aGUgU1NMIGNlcnRpZmljYXRlLCBQcml2YXRlIGtleSBhbmQgQ0EgYnVuZGxlIGZpbGVzIHJlc3BlY3RpdmVseSB1cGxvYWRlZCBvciBsb2NhdGVkIG9uIHRoZSBzZXJ2ZXIuIEFmdGVyIHRoYXQsIG1ha2Ugc3VyZSB0byBzYXZlIHRoZSBjb25maWd1cmF0aW9uIGZpbGUuPGJyIC8+PGJyIC8+PC9saT4NCgkJCQk8bGk+DQoJCQkJCQk8Yj5DaGVja2luZyB0aGUgY29uZmlndXJhdGlvbiBmaWxlIGFuZCByZXN0YXJ0aW5nIHRoZSB3ZWJzZXJ2ZXI8L2I+DQoJCQkJCQk8YnIgLz4NCgkJCQkJCTxiciAvPk5vdywgbWFrZSBzdXJlIHRvIGNoZWNrIHRoZSBmaWxlIHN5bnRheCBieSBydW5uaW5nIHRoaXMgY29tbWFuZDo8YnIgLz48YnIgLz48Y29kZT5hcGFjaGVjdGwgLXQ8L2NvZGU+PGJyIC8+PGJyIC8+PGltZyBjbGFzcz0ia2ItaW1hZ2UiIHNyYz0iaHR0cHM6Ly9OYW1lY2hlYXAuc2ltcGxla2IuY29tL1NpdGVDb250ZW50cy8yLTdDMjJENTIzNkE0NTQzRUI4MjdGM0JEODkzNkUxNTNFL21lZGlhL2FwYWNoZV8yMS5wbmciIC8+PGJyIC8+PGJyIC8+SWYgdGhlIGNvbW1hbmQgcmVzcG9uZHMgd2l0aCDigJw8Y29kZT5TeW50YXggT0s8L2NvZGU+4oCdLCB5b3UgY2FuIHJlYm9vdCB0aGUgd2Vic2VydmVyLiBUbyBkbyB0aGF0LCBydW4gdGhlIGNvbW1hbmQ6PGJyIC8+PGJyIC8+PGNvZGU+c3VkbyBzZXJ2aWNlIGFwYWNoZTIgcmVzdGFydDwvY29kZT48YnIgLz48YnIgLz5UaGUgY29uZmlndXJhdGlvbiBmaWxlIHNob3VsZCBiZSBsaXN0ZWQgaW4gdGhlIEFwYWNoZSBjb25maWd1cmF0aW9uIGZpbGVzIGxpc3QgKGl0IGNhbiBiZSBjaGVja2VkIGJ5IHJ1bm5pbmcgPGNvZGU+YXBhY2hlY3RsIC1TPC9jb2RlPiBvbmNlIGFnYWluKTo8YnIgLz48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXBhY2hlXzIyLnBuZyIgLz48YnIgLz48YnIgLz5Eb25lISBUaGUgd2Vic2l0ZSBpcyBub3cgc2VjdXJlZC4gVGhlIGluc3RhbGxhdGlvbiBjYW4gYmUgY2hlY2tlZCA8YSBocmVmPSJodHRwczovL2RlY29kZXIubGluay9zc2xjaGVja2VyLyAiIGxpbmt0ZXh0PSJoZXJlIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+aGVyZTwvYT4uPGJyIC8+PGJyIC8+VGhlcmUgYXJlIG5vIGZ1cnRoZXIgb2JsaWdhdG9yeSBhY3Rpb25zIGZvciBzZWN1cmluZyB5b3VyIGRvbWFpbiBuYW1lLCBob3dldmVyLCB5b3UgbWlnaHQgd2lzaCB0byBzZXQgdXAgYSBIVFRQUyByZWRpcmVjdCBmb3IgdGhlIHdlYnNpdGUgdG8gYmUgc3dpdGNoZWQgdG8gYSBzZWN1cmVkIHZlcnNpb24gYXV0b21hdGljYWxseSB3aXRob3V0IGVudGVyaW5nIGh0dHBzOi8vIG1hbnVhbGx5IGludG8gdGhlIGJyb3dzZXIgYWRkcmVzcyBiYXIuIEZvciBhIG1vcmUgZGV0YWlsZWQgZXhwbGFuYXRpb24gYWJvdXQgc2V0dGluZyB1cCB0aGUgcmVkaXJlY3QsIGNoZWNrIDxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85ODIxLzM4L2FwYWNoZS1yZWRpcmVjdC10by1odHRwcyIgbGlua3RleHQ9InRoaXMgcGFnZSIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPnRoaXMgcGFnZTwvYT4uPGJyIC8+PGJyIC8+SWYgdGhlcmUgYXJlIGlzc3VlcyB3aXRoIHRoZSBpbnN0YWxsYXRpb24sIG1ha2Ugc3VyZSB0byBkb3VibGUtY2hlY2sgdGhpcyBndWlkZSBzdGVwLWJ5LXN0ZXAgdG8gYXZvaWQgbWlzdGFrZXMuIFlvdSBjYW4gYWxzbyBjaGVjayB0aGUgbmV4dCBwYXJ0IG9mIHRoaXMgZ3VpZGUgYXMgd2VsbC48L2xpPg0KCQkJCTxiciAvPg0KCQkJCTxiciAvPg0KCQkJCTxoMiBpZD0iMiI+VGlwcyBhbmQgdHJvdWJsZXNob290ZXJzPC9oMj4NCgkJCQk8cD5JZiB5b3UgZmFjZSBhbnkgU1NMLXJlbGF0ZWQgaXNzdWVzIHdpdGggeW91ciBBcGFjaGUtYmFzZWQgd2Vic2l0ZSwgaGVyZSBpcyBob3cgdG8gdHJvdWJsZXNob290IHRoZSBtb3N0IGtub3duIGVycm9ycyB0aGF0IG1pZ2h0IG9jY3VyIGR1cmluZyB0aGUgcmVzdGFydDo8L3A+DQoJCQkJPHVsPg0KCQkJCQkJPGxpPg0KCQkJCQkJCQk8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTc3MS8yMjM4L2FwYWNoZS1lcnJvci14NTA5Y2hlY2twcml2YXRla2V5a2V5LXZhbHVlcy1taXNtYXRjaCIgbGlua3RleHQ9Ilg1MDlfY2hlY2tfcHJpdmF0ZV9rZXk6a2V5IHZhbHVlcyBtaXNtYXRjaCIgbGlua3R5cGU9IkN1c3RvbSIgdGFyZ2V0PSJfYmxhbmsiPlg1MDlfY2hlY2tfcHJpdmF0ZV9rZXk6a2V5IHZhbHVlcyBtaXNtYXRjaDwvYT4NCgkJCQkJCTwvbGk+DQoJCQkJCQk8bGk+DQoJCQkJCQkJCTxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85NzkzLzIyMzgvaW52YWxpZC1jb21tYW5kLXNzbGVuZ2luZS1lcnJvci1vbi1hcGFjaGUiIGxpbmt0ZXh0PSInSW52YWxpZCBjb21tYW5kICdTU0xFbmdpbmUnIGVycm9yIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+J0ludmFsaWQgY29tbWFuZCAnU1NMRW5naW5lJyBlcnJvcjwvYT4NCgkJCQkJCTwvbGk+DQoJCQkJCQk8bGk+DQoJCQkJCQkJCTxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85ODA2LzIyMzgvdW50cnVzdGVkLWFuZC1taXNzaW5nLWludGVybWVkaWF0ZS1jZXJ0aWZpY2F0ZS1lcnJvci1vbi1hcGFjaGUiIGxpbmt0ZXh0PSJVbnRydXN0ZWQgYW5kIE1pc3NpbmcgSW50ZXJtZWRpYXRlIENlcnRpZmljYXRlIEVycm9yIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+VW50cnVzdGVkIGFuZCBNaXNzaW5nIEludGVybWVkaWF0ZSBDZXJ0aWZpY2F0ZSBFcnJvcjwvYT4NCgkJCQkJCTwvbGk+DQoJCQkJCQk8bGk+DQoJCQkJCQkJCTxhIGhyZWY9Imh0dHBzOi8vd3d3Lm5hbWVjaGVhcC5jb20vc3VwcG9ydC9rbm93bGVkZ2ViYXNlL2FydGljbGUuYXNweC85ODU1LzIyMzgvbmdpbnhhcGFjaGUtZXJyb3ItMDkwNmQwNjZwZW0tcm91dGluZXNwZW1yZWFkYmlvYmFkLWVuZC1saW5lIiBsaW5rdGV4dD0iMDkwNkQwNjY6UEVNIHJvdXRpbmVzOlBFTV9yZWFkX2JpbzpiYWQgZW5kIGxpbmUiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj4wOTA2RDA2NjpQRU0gcm91dGluZXM6UEVNX3JlYWRfYmlvOmJhZCBlbmQgbGluZTwvYT4NCgkJCQkJCTwvbGk+DQoJCQkJPC91bD4NCgkJCQk8YnIgLz4NCgkJCQk8dWw+DQoJCQkJPC91bD4NCgkJCQk8cD4NCgkJCQkJCTxiPkhlcmUgYXJlIHNvbWUgbW9yZSB1c2VmdWwgdGlwcyBhYm91dCB0aGUgcHJvY2Vzczo8L2I+DQoJCQkJPC9wPg0KCQkJCTxvbD4NCgkJCQkJCTxsaT5JZiB5b3UgZmFjZSBhIOKAmHBlcm1pc3Npb24gZGVuaWVk4oCZIGVycm9yIHdoZW4gcnVubmluZyBhIGNvbW1hbmQsIHRyeSBhZGRpbmcgdGhlIOKAmHN1ZG/igJkgcGFyYW1ldGVyIGJlZm9yZSB0aGUgY29tbWFuZCBhbmQgcnVuIGl0IG9uY2UgYWdhaW4uPGJyIC8+PGJyIC8+Rm9yIGluc3RhbmNlLCBpZiA8Y29kZT5uYW5vIHNzbC5jb25mPC9jb2RlPiByZXN1bHRzIGluIDxjb2RlPlBlcm1pc3Npb24gZGVuaWVkPC9jb2RlPiwgeW91IGNhbiB0cnkgcnVubmluZyA8Y29kZT5zdWRvIG5hbm8gc3NsLmNvbmY8L2NvZGU+IGluc3RlYWQuPGJyIC8+PGJyIC8+QWRkaW5nIHN1ZG8gd2lsbCBncmFudCB5b3Ug4oCYc3VwZXJ1c2Vy4oCZIHBlcm1pc3Npb25zIGFuZCB0aGUgYWJpbGl0eSB0byBwZXJmb3JtIHNvbWUgYWN0aW9ucyB0aGF0IHJlcXVpcmUgcm9vdCB1c2VyIGFjY2VzcyB3aXRob3V0IHJlYWwgcm9vdCBhY2Nlc3MuPGJyIC8+PGJyIC8+UGxlYXNlIGtlZXAgaW4gbWluZCB0aGF0IHlvdSBtYXkgbmVlZCB0byBlbnRlciBhIHBhc3N3b3JkIGZvciB0aGUgc3VkbyB1c2VyIGR1cmluZyB0aGlzIG9wZXJhdGlvbi4gSXRzIHN5bWJvbHMgbWlnaHQgbm90IGJlIHNob3duIHdoZW4gZW50ZXJpbmcgKGZvciBzZWN1cml0eSByZWFzb25zKSwgaG93ZXZlciwgdGhlIHBhc3N3b3JkIHdpbGwgYmUgYWNjZXB0ZWQgaWYgZW50ZXJlZCBwcm9wZXJseS4gVGhpcyBwYXNzd29yZCBtYXkgaGF2ZSBiZWVuIGdpdmVuIHRvIHlvdSBieSB5b3VyIHNlcnZlciBhZG1pbiBvciBob3N0aW5nIHByb3ZpZGVyIHN1cHBvcnQgdGVhbSwgc28gaWYgeW91IGRvbuKAmXQga25vdyB0aGUgcGFzc3dvcmQsIHdlIHN1Z2dlc3QgY29udGFjdGluZyB0aGVtIGZvciBmdXJ0aGVyIGFzc2lzdGFuY2UuPGJyIC8+PGJyIC8+PC9saT4NCgkJCQkJCTxsaT5JZiB5b3Ugc2VlIHRoYXQgdGhlIFNTTCBoYXMgYmVlbiBpbnN0YWxsZWQgd2l0aG91dCB0aGUgQ0EgYnVuZGxlLCBpdCBpcyBwb3NzaWJsZSB0byBhZGQgdGhlIENBIGJ1bmRsZSB3aXRob3V0IGFueSBzaWduaWZpY2FudCBjaGFuZ2VzIHRvIHRoZSBjb25maWd1cmF0aW9uIHNldHRpbmdzLjxiciAvPjxiciAvPkluIHRoaXMgY2FzZSwgcGxlYXNlIGZpbmQgdGhlIFNTTCBjb25maWd1cmF0aW9uIGZpbGUgb24geW91ciBzZXJ2ZXIgYnkgZm9sbG93aW5nIHRoZSBzdGVwcyBpbiB0aGUgZ3VpZGUgZm9yIGFwYWNoZTIgb3IgaHR0cGQuIExvY2F0ZSB0aGUgcGF0aCB0byB0aGUgU1NMQ2VydGlmaWNhdGVGaWxlIGluIHRoZSBjb25maWd1cmF0aW9uIGZpbGUsIGFuZCBvcGVuIHRoZSBmaWxlIHZpYSB0aGF0IHBhdGggZm9yIGVkaXRpbmcuIFlvdSB3aWxsIHNlZSBvbmUgYmxvY2sgb2YgY29kZSB0aGVyZSAod2hpY2ggaXMgdGhlIFNTTCBpdHNlbGYpLiBZb3UgY2FuIGRvd25sb2FkIHRoZSBDQSBidW5kbGUgZmlsZSBmcm9tIHlvdXIgTmFtZWNoZWFwIGFjY291bnQgKGl0IGlzIGRvd25sb2FkZWQgaW4gdGhlIHNhbWUgYXJjaGl2ZSB3aXRoIHRoZSBTU0wgY2VydGlmaWNhdGUpIG9yIGZyb20gPGEgaHJlZj0iaHR0cHM6Ly93d3cubmFtZWNoZWFwLmNvbS9zdXBwb3J0L2tub3dsZWRnZWJhc2UvYXJ0aWNsZS5hc3B4LzkzOTMvNjkvd2hlcmUtZG8taS1maW5kLXNzbC1jYS1idW5kbGUiIGxpbmt0ZXh0PSJ0aGlzIHBhZ2UiIGxpbmt0eXBlPSJDdXN0b20iIHRhcmdldD0iX2JsYW5rIj50aGlzIHBhZ2U8L2E+IGFuZCBjb3B5IHRoZSB3aG9sZSAuY2EtYnVuZGxlIGZpbGUgY29udGVudHMgdG8gdGhlIG9wZW5lZCBTU0xDZXJ0aWZpY2F0ZUZpbGUuPGJyIC8+PGJyIC8+VGhlIG5ldyBDQSBidW5kbGUgY29kZXMgc2hvdWxkIGJlIGVudGVyZWQgZnJvbSB0aGUgbmV3IGxpbmUgYWZ0ZXIgdGhlIFNTTCBjb2RlIHdoaWNoIGlzIGFscmVhZHkgcHJlc2VudCB0aGVyZSwgd2l0aG91dCBhZGRpbmcgYW55IG5ldyBsaW5lcyBiZXR3ZWVuIHRoZW0sIGxpa2UgdGhpczo8YnIgLz48YnIgLz48aW1nIGNsYXNzPSJrYi1pbWFnZSIgc3JjPSJodHRwczovL05hbWVjaGVhcC5zaW1wbGVrYi5jb20vU2l0ZUNvbnRlbnRzLzItN0MyMkQ1MjM2QTQ1NDNFQjgyN0YzQkQ4OTM2RTE1M0UvbWVkaWEvYXBhY2hlXzIzLnBuZyIgLz48YnIgLz48YnIgLz48L2xpPg0KCQkJCQkJPHAgaWQ9IjMiPg0KCQkJCQkJPC9wPg0KCQkJCQkJPGxpPkFzIGZvciA8Y29kZT5hcGFjaGUyPC9jb2RlPiwgdGhlcmUgYXJlIHNldmVyYWwgd2F5cyB0byBtYW5hZ2UgdGhlIGNvbmZpZ3VyYXRpb24gc2V0dGluZ3MgZm9yIHRoZSA0NDMgSFRUUFMgcG9ydC48YnIgLz48YnIgLz5JdCBpcyBwb3NzaWJsZSB0byBhZGQgdGhlIEhUVFBTIHNldHRpbmdzIGJsb2NrIHRvIHRoZSBzYW1lIGNvbmZpZ3VyYXRpb24gZmlsZSB0aGF0IGRldGVybWluZXMgdGhlIDgwIEhUVFAgcG9ydCBjb25uZWN0aW9ucyAodXN1YWxseSBpdCBpcyBjYWxsZWQgMDAwLWRlZmF1bHQuY29uZikuIFRoaXMgbWV0aG9kIHdhcyBvdXRsaW5lZCBpbiB0aGUgZ3VpZGUgcHJldmlvdXNseS4gVGhlIHByb3Mgb2YgdGhpcyBtZXRob2QgYXJlIHRoYXQgYWxsIHRoZSBzZXR0aW5ncyBmb3IgdGhlIHdlYnNpdGUgYXJlIG1hbmFnZWQgaW4gdGhlIHNhbWUgZmlsZSBhbmQgY2FuIGJlIGxvY2F0ZWQgYW5kIG1vZGlmaWVkIHF1aWNrbHkuIFRoZSBjb25zIGFyZSB0aGF0IHRoZSBTU0wgZmlsZXMgY291bGQgZ2V0IGxvc3QgYW1vbmcgb3RoZXIgY29kZXMgaW4gdGhlIGJpZyBjb25maWd1cmF0aW9uIGZpbGUsIGFuZCBjb3VsZCBiZSBkaWZmaWN1bHQgdG8gbG9jYXRlIGZvciBtb2RpZmljYXRpb25zIG9yIHJlbW92YWwuPGJyIC8+PGJyIC8+QW4gYWx0ZXJuYXRpdmUgbWV0aG9kIGlzIHRvIGNyZWF0ZSBhIHNlcGFyYXRlIGNvbmZpZ3VyYXRpb24gZmlsZSB3aXRoaW4gdGhlIHNhbWUgZm9sZGVyIGFzIHRoZSBkZWZhdWx0IGZpbGUgZm9yIEhUVFAgY29ubmVjdGlvbnMuIElmIHRoZSBmb2xkZXIgaXMgPGNvZGU+L2V0Yy9hcGFjaGUyL3NpdGVzLWVuYWJsZWQ8L2NvZGU+LCBubyBmdXJ0aGVyIHNwZWNpYWwgYWN0aW9ucyBzaG91bGQgYmUgbmVlZGVkIHRvIGFjY2VwdCBhbmQgdXNlIHRoZSBjb25maWd1cmF0aW9uIGZpbGUuIEp1c3QgZm9sbG93IHRoZSBzdGVwcyBmcm9tIHRoZSBndWlkZSByZWdhcmRpbmcgYWRkaW5nIGEgYmxvY2sgb2YgY29kZSwgc3ludGF4IGNoZWNrcywgYW5kIEFwYWNoZSBzZXJ2aWNlIHJlc3RhcnQuPGJyIC8+PGJyIC8+QW5kIGlmIHRoZSBuZXcgZmlsZSBpcyBjcmVhdGVkIHdpdGhpbiA8Y29kZT4vZXRjL2FwYWNoZTIvc2l0ZXMtYXZhaWxhYmxlPC9jb2RlPiBmb2xkZXIsIHlvdSB3aWxsIG5lZWQgdG8gdG8gcnVuIHRoZSBmb2xsb3dpbmcgY29tbWFuZCBhZnRlciB0aGUgZmlsZSBpcyBjcmVhdGVkIGFuZCB0aGUgbmVjZXNzYXJ5IGNvZGUgaXMgc2F2ZWQgaW4gaXQ6PGJyIC8+PGJyIC8+PGNvZGU+c3VkbyBhMmVuc2l0ZSB5b3VyX3NzbF9jb25maWdfbmFtZTwvY29kZT48YnIgLz48YnIgLz5BZnRlciB0aGF0LCBwbGVhc2UgcHJvY2VlZCB3aXRoIHRoZSBzeW50YXggY2hlY2sgYW5kIHRoZSBBcGFjaGUgc2VydmljZSByZXN0YXJ0IHRvIGZpbmFsaXplIHRoZSBpbnN0YWxsYXRpb24gcHJvY2Vzcy48L2xpPg0KCQkJCTwvb2w+DQoJCQkJPGJyIC8+DQoJCQkJPGJyIC8+DQoJCQkJPHA+DQoJCQkJCQk8YSBocmVmPSJodHRwczovL3d3dy5uYW1lY2hlYXAuY29tL3N1cHBvcnQva25vd2xlZGdlYmFzZS9hcnRpY2xlLmFzcHgvOTQyMy8zMy9pbnN0YWxsaW5nLWFuLXNzbC1jZXJ0aWZpY2F0ZS1vbi1hcGFjaGUiIGxpbmt0ZXh0PSJCYWNrIHRvIHRoZSBtYWluIGd1aWRlIiBsaW5rdHlwZT0iQ3VzdG9tIiB0YXJnZXQ9Il9ibGFuayI+QmFjayB0byB0aGUgbWFpbiBndWlkZSAmZ3Q7ICZndDs8L2E+DQoJCQkJPC9wPg0KCQk8L29sPg0K","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"2022-05-23T10:02:32.0000000","LiveDateTime":"1754-02-02T00:00:00.0000000","CreatedDateTime":"2020-09-17T10:35:26.0000000","ApprovalDatetime":"2020-09-17T13:19:22.0000000","RequestCount":36765,"MarkedAsNew":false,"MarkedAsFeatured":false,"RatingValue":0,"CategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":33,"CategoryName":"SSL Installation"}],"AssociatedCategories":[{"CategoryId":33,"CategoryName":"SSL Installation","CategoryDisplayName":"HostingSSL Installation"}],"AssociatedTags":[],"RelatedArticles":[],"AssociatedMedias":[],"PreferredCategoryId":0,"RootParentCategoryName":"","RootParentCategoryId":0},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategorybycategoryid:\"{\\\"categoryId\\\":33}\"":{"body":{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryDto","ParentCategoryId":12,"Parent_Category_Name":"Hosting","FriendlyId":null,"ApprovedYN":true,"TreatAsTopicYN":false,"CreatedDateTime":"07/21/2008 16:07:56","CurrentCategoryPaths":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":1,"CategoryId":12,"CategoryName":"Hosting"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryPathDto","Level":2,"CategoryId":33,"CategoryName":"SSL Installation"}],"RelatedCategories":[],"AssociatedArticles":[{"ArticleId":9593,"Title":"Installing an SSL certificate on Amazon Web Services (AWS)","ArticleName":"Installing an SSL certificate on Amazon Web Services (AWS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/02/2020"},{"ArticleId":9595,"Title":"HTTP to HTTPS redirection on IIS","ArticleName":"HTTP to HTTPS redirection on IIS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/25/2019"},{"ArticleId":9635,"Title":"Installing an SSL certificate on Synology NAS","ArticleName":"Installing an SSL certificate on Synology NAS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9681,"Title":"Installing an SSL Certificate in Vesta CP","ArticleName":"Installing an SSL Certificate in Vesta CP","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9686,"Title":"Installing an SSL Certificate on Sun Java System Web Server 7.x","ArticleName":"Installing an SSL Certificate on Sun Java System Web Server 7.x","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9702,"Title":"Installing an SSL certificate on Webmin","ArticleName":"Installing an SSL certificate on Webmin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9705,"Title":"Installing an SSL certificate on Node.js","ArticleName":"Installing an SSL certificate on Node.js","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9746,"Title":"Installing an SSL certificate in Exchange 2013 EAC","ArticleName":"Installing an SSL certificate in Exchange 2013 EAC","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/28/2024"},{"ArticleId":9749,"Title":"Installing an SSL certificate in Exchange 2013 Shell","ArticleName":"Installing an SSL certificate in Exchange 2013 Shell","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9750,"Title":"How to export/import certificates on Exchange 2013 Shell","ArticleName":"How to export/import certificates on Exchange 2013 Shell","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/12/2020"},{"ArticleId":9754,"Title":"Installing an SSL certificate on IIS 8&10","ArticleName":"Installing an SSL certificate on IIS 8&10","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9823,"Title":"Installing an SSL certificate on Microsoft Azure Web App","ArticleName":"Installing an SSL certificate on Microsoft Azure Web App","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/04/2024"},{"ArticleId":9825,"Title":"Installing an SSL certificate on a GlassFish application server","ArticleName":"Installing an SSL certificate on a GlassFish application server","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/28/2019"},{"ArticleId":9842,"Title":"Installing an SSL certificate on Zimbra","ArticleName":"Installing an SSL certificate on Zimbra","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/12/2023"},{"ArticleId":9853,"Title":"Installing an SSL certificate on Google App Engine","ArticleName":"Installing an SSL certificate on Google App Engine","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9865,"Title":"Installing an SSL certificate on Exchange 2010","ArticleName":"Installing an SSL certificate on Exchange 2010","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9899,"Title":"Installing an SSL certificate on Mac OS X/Yosemite/El Capitan","ArticleName":"Installing an SSL certificate on Mac OS X/Yosemite/El Capitan","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9919,"Title":"Installing an SSL certificate on SonicWall","ArticleName":"Installing an SSL certificate on SonicWall","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9956,"Title":"Installing an SSL certificate on Plesk Onyx","ArticleName":"Installing an SSL certificate on Plesk Onyx","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9958,"Title":"Installing an SSL certificate on Citrix NetScaler VPX","ArticleName":"Installing an SSL certificate on Citrix NetScaler VPX","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/29/2019"},{"ArticleId":9970,"Title":"IIS: multiple certificates installation","ArticleName":"IIS: multiple certificates installation","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"10/29/2019"},{"ArticleId":10026,"Title":"Installing an SSL certificate on XAMPP","ArticleName":"Installing an SSL certificate on XAMPP","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/05/2026"},{"ArticleId":10050,"Title":"Installing an SSL certificate on Heroku SSL","ArticleName":"Installing an SSL certificate on Heroku SSL","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/25/2025"},{"ArticleId":10052,"Title":"Installing an SSL certificate in CWP 7","ArticleName":"Installing an SSL certificate in CWP 7","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10063,"Title":"Installing an SSL certificate on Windows using Certeq","ArticleName":"Installing an SSL certificate on Windows using Certeq","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/02/2019"},{"ArticleId":10134,"Title":"Installing an SSL certificate on Ubiquiti Unifi","ArticleName":"Installing an SSL certificate on Ubiquiti Unifi","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10154,"Title":"Installing an SSL certificate on ISPConfig","ArticleName":"Installing an SSL certificate on ISPConfig","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":10175,"Title":"Can I install an SSL Certificate on a Parked Domain in cPanel?","ArticleName":"Can I install an SSL Certificate on a Parked Domain in cPanel?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"04/27/2026"},{"ArticleId":10252,"Title":"How to set up an SSL certificate in SiteWorx account","ArticleName":"How to set up an SSL certificate in SiteWorx account","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/20/2020"},{"ArticleId":10313,"Title":"SSL Certificate installation on httpd (CentOS)","ArticleName":"SSL Certificate installation on httpd (CentOS)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/23/2022"},{"ArticleId":10314,"Title":"SSL Certificate installation on apache2 (Debian, Ubuntu)","ArticleName":"SSL Certificate installation on apache2 (Debian, Ubuntu)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/23/2022"},{"ArticleId":10332,"Title":"Importing/Exporting certificates on Mac OS via Keychain","ArticleName":"Importing/Exporting certificates on Mac OS via Keychain","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/06/2022"},{"ArticleId":633,"Title":"IIS","ArticleName":"IIS","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/22/2020"},{"ArticleId":9418,"Title":"Installing an SSL certificate on your server, using cPanel","ArticleName":"Installing an SSL certificate on your server, using cPanel","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/27/2026"},{"ArticleId":9419,"Title":"Installing an SSL certificate on Nginx","ArticleName":"Installing an SSL certificate on Nginx","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/05/2026"},{"ArticleId":9423,"Title":"Installing an SSL certificate on Apache","ArticleName":"Installing an SSL certificate on Apache","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9424,"Title":"Installing an SSL Certificate on IIS 7","ArticleName":"Installing an SSL Certificate on IIS 7","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"02/29/2024"},{"ArticleId":9425,"Title":"Installing an SSL Certificate using DirectAdmin","ArticleName":"Installing an SSL Certificate using DirectAdmin","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9439,"Title":"Installing an SSL Certificate using WHM","ArticleName":"Installing an SSL Certificate using WHM","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":9441,"Title":"Installing an SSL certificate on Tomcat","ArticleName":"Installing an SSL certificate on Tomcat","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9443,"Title":"Installing an SSL Certificate on Exchange 2007 (PowerShell)","ArticleName":"Installing an SSL Certificate on Exchange 2007 (PowerShell)","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/13/2022"},{"ArticleId":9448,"Title":"Installing an SSL certificate in Plesk 12","ArticleName":"Installing an SSL certificate in Plesk 12","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"01/31/2024"},{"ArticleId":786,"Title":"What is an SSL certificate and what is it used for?","ArticleName":"What is an SSL certificate and what is it used for?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/24/2023"},{"ArticleId":9260,"Title":"Why is it beneficial to have a dedicated IP address?","ArticleName":"Why is it beneficial to have a dedicated IP address?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/03/2021"},{"ArticleId":9259,"Title":"SNI technology","ArticleName":"SNI technology","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/06/2018"},{"ArticleId":214,"Title":"Can I install SSL certificates for a couple of domains at once on Namecheap hosting servers?","ArticleName":"Can I install SSL certificates for a couple of domains at once on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/21/2024"},{"ArticleId":215,"Title":"How many SSL certificates can I install under my Namecheap hosting account?","ArticleName":"How many SSL certificates can I install under my Namecheap hosting account?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"12/28/2020"},{"ArticleId":804,"Title":"SSL certificate activation and installation for domain(s) hosted on Namecheap hosting servers","ArticleName":"SSL certificate activation and installation for domain(s) hosted on Namecheap hosting servers","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"},{"ArticleId":9393,"Title":"Where do I find SSL CA Bundle?","ArticleName":"Where do I find SSL CA Bundle?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"09/22/2025"},{"ArticleId":211,"Title":"How can I get a CSR code for a domain hosted on Namecheap hosting servers?","ArticleName":"How can I get a CSR code for a domain hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"07/19/2024"},{"ArticleId":213,"Title":"Do you allow SSL installation on a subdomain of a domain hosted on Namecheap hosting servers?","ArticleName":"Do you allow SSL installation on a subdomain of a domain hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"06/05/2026"},{"ArticleId":9464,"Title":"Can I download an issued certificate on your site?","ArticleName":"Can I download an issued certificate on your site?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"11/12/2024"},{"ArticleId":9465,"Title":"How do I export my certificate from Apache?","ArticleName":"How do I export my certificate from Apache?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"03/21/2024"},{"ArticleId":122,"Title":"Is there a shared SSL certificate for domains hosted on Namecheap hosting servers?","ArticleName":"Is there a shared SSL certificate for domains hosted on Namecheap hosting servers?","LiveDateTime":"02/02/1754 00:00:00","NewTillDate":null,"FeaturedTillDate":null,"ModifiedDateTime":"05/09/2025"}],"AssociatedTags":[],"CategoryId":33,"CategoryName":"SSL Installation"},"status":200,"statusText":"OK"},"/api/v1/ncpl/simplekb/getcategories:\"{\\\"parentCategoryId\\\":0,\\\"getTree\\\":true}\"":{"body":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/cloud-red.png","ShortDesc":"","CategoryId":2228,"CategoryName":"Apps","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/easywp-red.png","ShortDesc":"","CategoryId":2239,"CategoryName":"EasyWP","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2251,"CategoryName":"Supersonic CDN"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2254,"CategoryName":"Domains How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2255,"CategoryName":"Hosting How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2257,"CategoryName":"Sales & Payments How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2258,"CategoryName":"cPanel Email How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2253,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2262,"CategoryName":"EasyWP How-To"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://download.namecheap.com/assets/img/domainvault-red@2x.png","ShortDesc":"","CategoryId":2289,"CategoryName":"Domain Vault","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2298,"CategoryName":"Site Maker"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/support-red.png","ShortDesc":"","CategoryId":5,"CategoryName":"General & Support","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2228,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":177,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2280,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2279,"CategoryName":"General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/savings-red.png","ShortDesc":"","CategoryId":2200,"CategoryName":"Checkout & Billing","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":7,"CategoryName":"Billing FAQ"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2201,"CategoryName":"Domains Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":21,"CategoryName":"Hosting Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2281,"CategoryName":"WordPress Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2282,"CategoryName":"Plugins and Themes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":71,"CategoryName":"SSL Certificates Billing"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/reseller-red.png","ShortDesc":"","CategoryId":34,"CategoryName":"Domains","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2232,"CategoryName":"DNSSEC"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2234,"CategoryName":"Google Workspace (formerly G Suite)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2237,"CategoryName":"Host records setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":46,"CategoryName":"Domain Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":10,"CategoryName":"DNS Questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":11,"CategoryName":"Dynamic DNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":35,"CategoryName":"Registrations"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/protection-red.png","ShortDesc":"","CategoryId":37,"CategoryName":"Domain Privacy Protection","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2200,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2177,"CategoryName":"Private Email"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2207,"CategoryName":"Renewal questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2284,"CategoryName":"WordPress Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2285,"CategoryName":"SFTP and Database access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/status-red.png","ShortDesc":"","CategoryId":2209,"CategoryName":"Domain Transfers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":8,"CategoryName":"Transfer Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":83,"CategoryName":"Transfer to Namecheap"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":84,"CategoryName":"Transfer to another provider"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2209,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":219,"CategoryName":"Canceled Transfers"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":36,"CategoryName":"Domains with extended attributes"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/server-red.png","ShortDesc":"","CategoryId":12,"CategoryName":"Hosting","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2219,"CategoryName":"PHP Configuration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2225,"CategoryName":"SEO"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2252,"CategoryName":"InterWorx questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2291,"CategoryName":"Webuzo questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":27,"CategoryName":"Getting Started"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":22,"CategoryName":"Hosting Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":29,"CategoryName":"cPanel questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2182,"CategoryName":"cPanel: Software Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2187,"CategoryName":"cPanel: WordPress"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2210,"CategoryName":"cPanel Add-ons"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":48,"CategoryName":"VPS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2188,"CategoryName":"Dedicated Server"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2286,"CategoryName":"Domains questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2288,"CategoryName":"Billing questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":30,"CategoryName":"WHM questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":51,"CategoryName":"FreeDNS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/email-red.png","ShortDesc":"","CategoryId":93,"CategoryName":"Email service","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2216,"CategoryName":"Spam Protection"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2226,"CategoryName":"Email Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2260,"CategoryName":"Private Email Contacts and Calendars Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2306,"CategoryName":"New Private Email Platform"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2179,"CategoryName":"Private Email: General Information"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2215,"CategoryName":"Private Email: Mailbox Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2214,"CategoryName":"Email Forwarding"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2176,"CategoryName":"Private Email: DNS Settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2178,"CategoryName":"Private Email: Webmail Features"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2175,"CategoryName":"Private Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2171,"CategoryName":"Private Email: Active Sync (Exchange) Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":31,"CategoryName":"cPanel Email FAQs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":32,"CategoryName":"DNS settings"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":15,"CategoryName":"Namecheap Market"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2186,"CategoryName":"cPanel Email: Client Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2239,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2287,"CategoryName":"SSL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2208,"CategoryName":"3rd Party Services Setup"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":93,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2204,"CategoryName":"Private Email: Video Overview"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/security-red.png","ShortDesc":"","CategoryId":14,"CategoryName":"SSL Certificates","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2217,"CategoryName":"Renewal"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2218,"CategoryName":"cPanel SSL Plugin"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2221,"CategoryName":"Multi-Domain SSL Certificates"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2222,"CategoryName":"Cancellation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2223,"CategoryName":"Browser errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2224,"CategoryName":"Site Seal, Logo"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2238,"CategoryName":"SSL installation errors"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2290,"CategoryName":"CSR code"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2293,"CategoryName":"Automated SSL management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":38,"CategoryName":"SSL General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":67,"CategoryName":"Activation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":68,"CategoryName":"Validation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":69,"CategoryName":"Installation"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":14,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":70,"CategoryName":"Reissuance"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":true,"Description":"","ImageUrl":"/assets/img/pictograms/150/performance-red.png","ShortDesc":"","CategoryId":9,"CategoryName":"My Account","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":45,"CategoryName":"Account Security"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":43,"CategoryName":"Profile Management"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":9,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":44,"CategoryName":"Account Access"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":34,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2278,"CategoryName":"Handshake TLDs"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":103,"CategoryName":"LVE (CloudLinux)"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/affiliates-red.png","ShortDesc":"","CategoryId":55,"CategoryName":"Affiliates","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":89,"CategoryName":"SSH Access"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/tools-red.png","ShortDesc":"","CategoryId":2211,"CategoryName":"API & Resellers","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2227,"CategoryName":"SSL Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2229,"CategoryName":"Hosting Resellers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":63,"CategoryName":"Namecheap API"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2211,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2196,"CategoryName":"WHMCS module for SSL"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/timer-red.png","ShortDesc":"","CategoryId":2212,"CategoryName":"Legacy Products","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":205,"CategoryName":"FTP questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2180,"CategoryName":"MySQL questions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2199,"CategoryName":"Hosting Migration"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"/assets/img/pictograms/150/premiumdns-red.png","ShortDesc":"","CategoryId":2231,"CategoryName":"PremiumDNS","SubCategories":[]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2194,"CategoryName":"Tips & Tricks"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":0,"TreatAsTopicYN":false,"Description":"","ImageUrl":"https://static.nc-img.com/live-resource/icons/knowledgebase/fastVPN_icon-150px.png","ShortDesc":"","CategoryId":2265,"CategoryName":"FastVPN","SubCategories":[{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2292,"CategoryName":"Browser Extensions"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2274,"CategoryName":"General"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2270,"CategoryName":"Routers"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2272,"CategoryName":"TV"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2273,"CategoryName":"Gaming Consoles"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2268,"CategoryName":"macOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2269,"CategoryName":"iOS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2271,"CategoryName":"Linux"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2266,"CategoryName":"Windows"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":2265,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":2267,"CategoryName":"Android"}]},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":239,"CategoryName":"WHMCS"},{"__type":"Nc:SimpleKB:Abstractions:Dtos:CategoryItemDto","ParentCategoryId":12,"TreatAsTopicYN":false,"Description":"","ImageUrl":"","ShortDesc":"","CategoryId":33,"CategoryName":"SSL Installation"}],"status":200,"statusText":"OK"}}| Note: Before you begin, ensure you’re all set with the prerequisites. |
| SSL installation instructions for CentOS |
sudo apachectl -S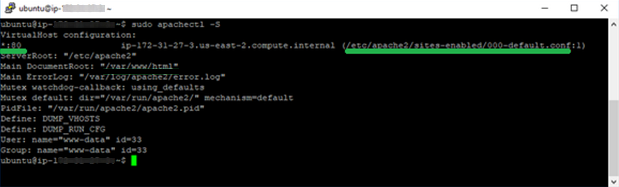
000-default.conf"./etc/apache2/sites-enabled./etc/apache2/sites-available or /etc/apache2/sites-enabled folder - here
in the 'Tips and troubleshootings' part of this guide.sudo a2enmod ssl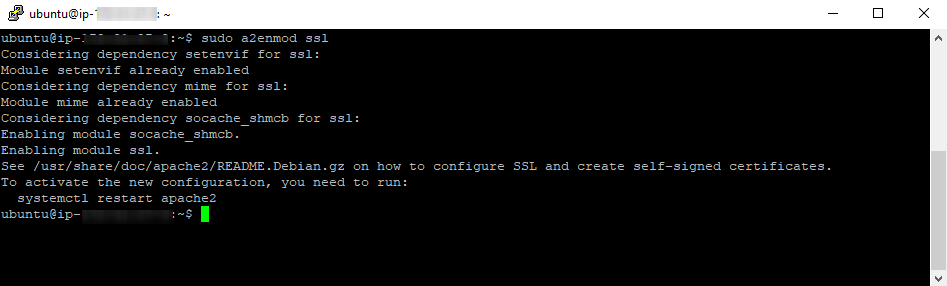
Module ssl already enabled”, then the module has already been enabledEnabling module ssl’ and will complete the module enabling.sudo service apache2 restart
apachectl -S/etc/apache2/sites-enabled folder.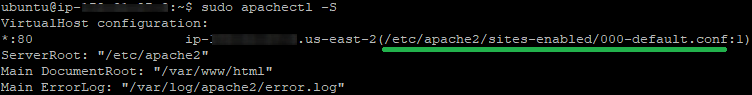
<VirtualHost *:443>
ServerName (DOMAIN NAME OF THE WEBSITE)
DocumentRoot (ROOT FOLDER OF THE WEBSITE)
SSLEngine on
SSLCertificateFile (Certificate PATH)
SSLCertificateKeyFile (Private key PATH)
SSLCertificateChainFile (CA Bundle PATH)
</VirtualHost><VirtualHost *:443>
ServerName example.com
DocumentRoot /var/www/html
SSLEngine on
SSLCertificateFile /etc/ssl/1.crt
SSLCertificateKeyFile /etc/ssl/1.key
SSLCertificateChainFile /etc/ssl/1.ca-bundle
</VirtualHost>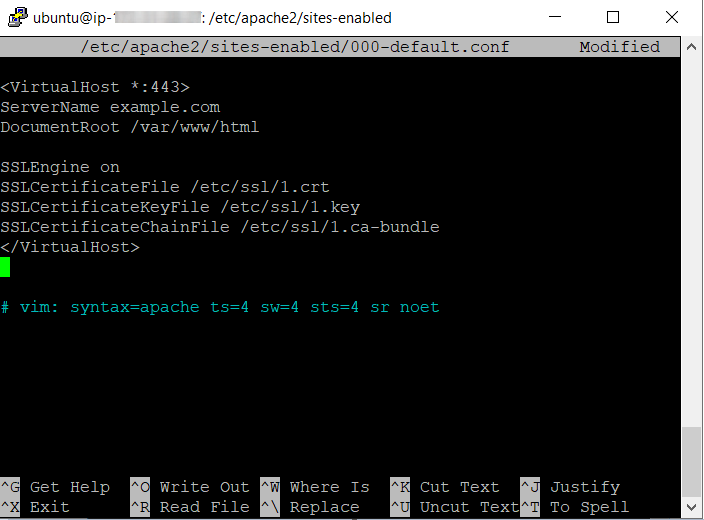
apachectl -S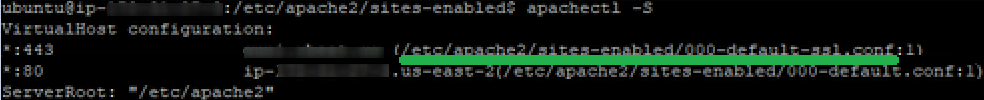
SSLCertificateFile
SSLCertificateKeyFile
SSLCertificateChainFileapachectl -t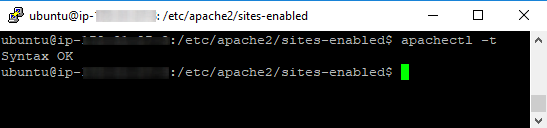
Syntax OK”, you can reboot the webserver. To do that, run the command:sudo service apache2 restartapachectl -S once again):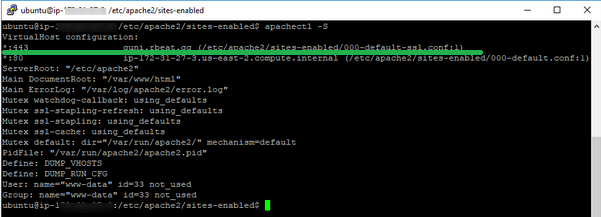
If you face any SSL-related issues with your Apache-based website, here is how to troubleshoot the most known errors that might occur during the restart:
Here are some more useful tips about the process:
nano ssl.conf results in Permission denied, you can try running sudo nano ssl.conf instead.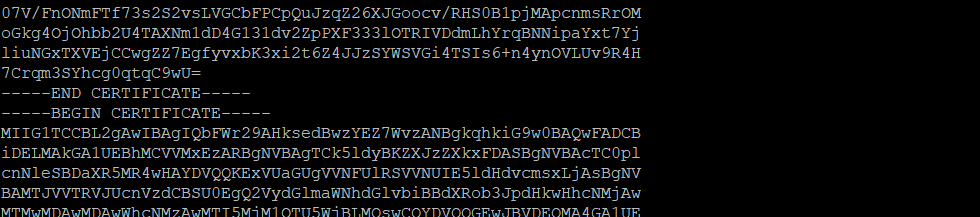
apache2, there are several ways to manage the configuration settings for the 443 HTTPS port./etc/apache2/sites-enabled, no further special actions should be needed to accept and use the configuration file. Just follow the steps from the guide regarding adding a block of code, syntax checks, and Apache service restart./etc/apache2/sites-available folder, you will need to to run the following command after the file is created and the necessary code is saved in it:sudo a2ensite your_ssl_config_nameNeed help? We're always here for you.