- Satisfied the sender address is correct, the recipient server asks for the receiver’. This is how envelope data is treated. The sending server will now forward the contents of the email contained in the envelope. Once the email has been received, the recipient server gives the mail server a receipt.
Types of MUA Retrieving email is tasked by a software program called a Mail User Agent (MUA). There are two types of MUA, and these are classed depending on how emails are accessed, via installed software (email client) or through a browser (webmail).
1. When an MUA is installed on a user’s system, it’s called an email client. To use an email client, MUA such as Microsoft Outlook, Mozilla Thunderbird, and Lotus Notes allows users to add the MUA program to their computer. This program is used to download and store email messages to their computers. With a client MUA, emails can be read and written offline.
2. When email is accessed online, it’s called webmail. Web-based MUAs such as Yahoo, Gmail, and Hotmail store messages on their mail servers and can only be accessed through a web page. The main advantage of webmail is sending and receiving mail from a web browser, anywhere. The main disadvantage of using a web-based application is the need to be connected to the internet to use it.
The journey of an emailLet’s break down how an email is transmitted. Like most Internet data, emails travel across the internet as a stream of packets using the internet’s TCP/IP protocol. This process can be broken down into three steps:
1. Once an email is sent, the TCP protocol breaks it down into packets ( ); each packet bears the sender and the email recipient’s address.
2. The IP protocol routes the packets to the intended destination. Routers over the world wide web examine the addresses in each packet to calculate the most efficient route to the email’s destination server. Once a pathway is planned, the packets are forwarded to the next router. Several factors go into how email packets are routed, such as traffic volume on any given network.
3. Once the packets have arrived at the recipient's email server, TCP recombines them into the email format in which it was sent (on that the recipient can read).
How are emails structured?It might have been a while, but consider how you’d formulate a formal letter you’d take to your mail office or drop in a mailbox. You start by taking pen to paper and writing your name and address on the right-hand side. On the left-hand side, you write the name and address of the intended recipient. Once you’ve written the body of the letter, you place it in an envelope. This is sealed, and the intended recipient's address is written on the front so that the sorting office knows where the letter will be sent. Just in case there is a problem finding the recipient, the sender's address is written on the back.
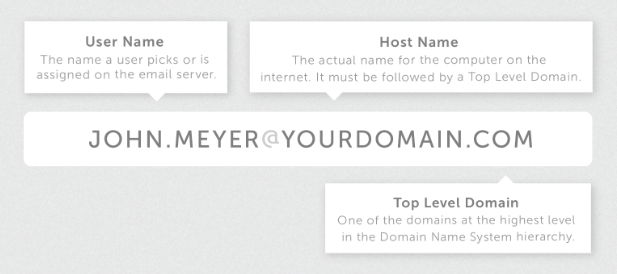
As technical as email might sound, the letter analogy is the same as how emails are structured. Emails are composed in a mail client (comparable to pen and paper). This is known as MIME data (multipurpose internet mail extensions). The mail server puts the email into an envelope, including the recipient and sender’s addresses (this is called envelope data). Email users won’t come across the envelope since it’s part of an internal process to route an email.
Email envelope, body, and headerAn email is constructed with three parts:
1. The envelope that we’ve just mentioned. This is separate from the body and header. Next is the body (that contains the content of the message). Email clients separate an email header and the body (the content text).
2. The body is distinct from the header; it contains everything within the message, including images, text, and other data (such as attachments).
3. The header is arguably the most exciting part of an email’s DNA. The header always precedes the body text. This is logical. When you receive an email, it’s often the header that’s scanned first before the email is opened.
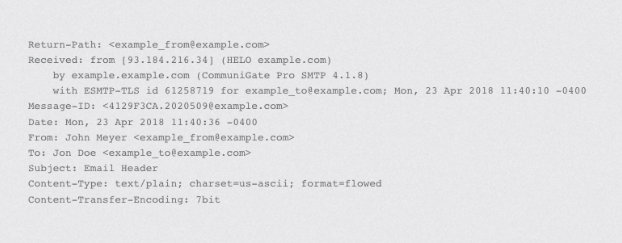
The header includes the mandatory information, including the sender, recipient, and date. Other header lines such as subject and cc are optional. Although only required headers appear to the user, the header includes additional details such as the route the email took as it was transferred from one computer to another. We’ve mentioned the job of Mail Transfer Agents (MTAs). When an MTA forwards an email, it is time-stamped. You’ll notice that some emails that had multiple destinations since the email origination have several received headers. Most of this extra information is hidden inside the email. When viewed in their entirety, they look something like this:
There’s a lot to digest here, but we hope this piece has given you some understanding of just how much goes into the seemingly simple act of sending an email.
Want to do more with email? Our
business email setup guide takes you through all the smart options to include from the very beginning when you get a business email address.
Already set up? Our
email support page has all you need to configure your email the way you like it.
If you want to work through which email plan is best for you, or even try Namecheap’s Private Email for free for the first two months, you can view our
Private email page, or ask our friendly
Customer Service Support to help you decide, anytime.